- VulnCheck KEV has expanded to provide Email and Slack alerting.
- In 2025, VulnCheck KEV has 142% more KEVs than CISA.
- Based on VulnCheck intelligence, 70.3% of CISA KEVs have publicly available exploitation evidence days, months or years before being added to the CISA KEV catalog.
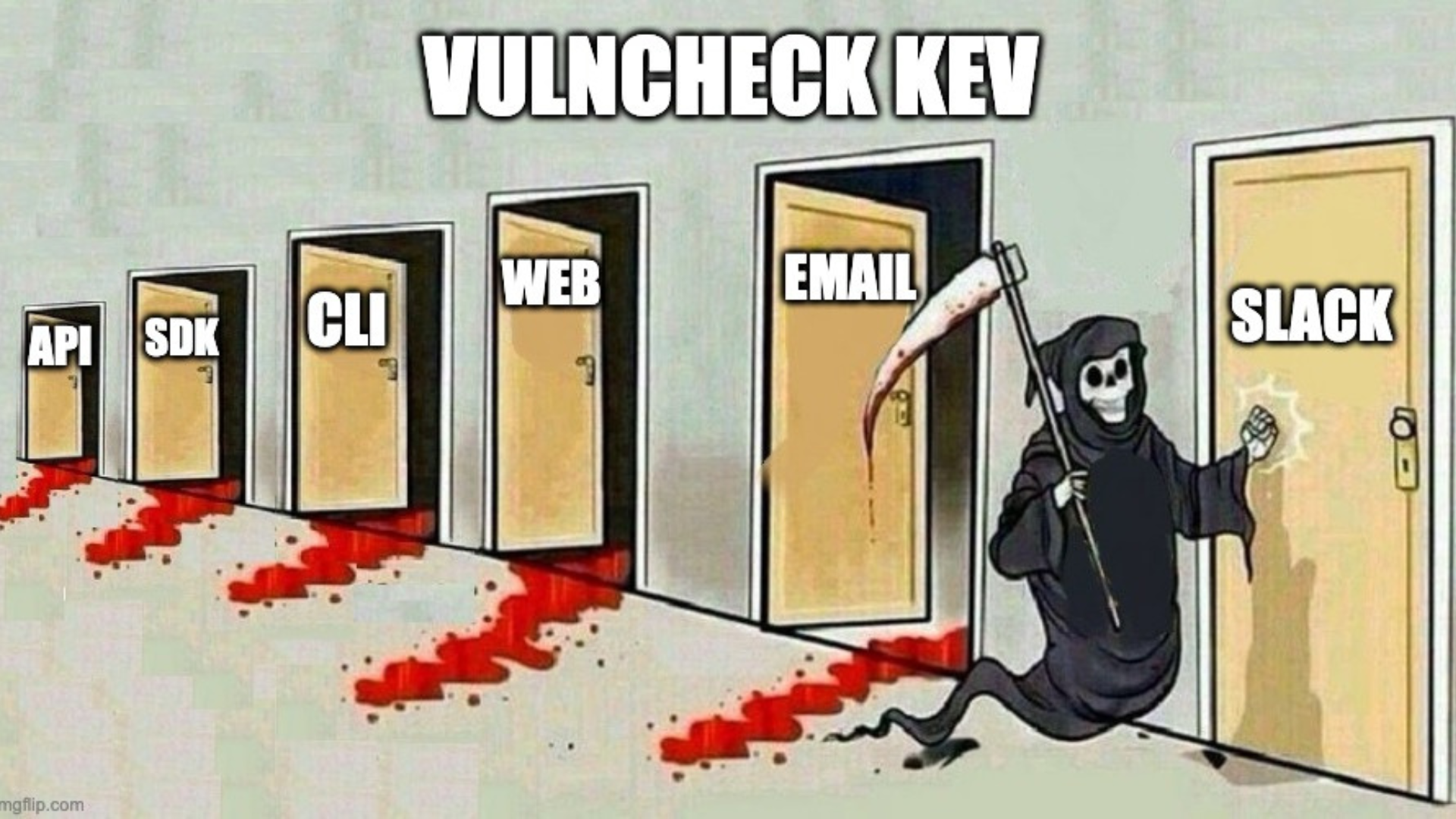
We’re excited to announce the expansion of VulnCheck Community to include VulnCheck KEV Alerts: you can now receive alerts via Email and Slack. This further enhances the accessibility of VulnCheck KEV, which is now available through the VulnCheck API, Go SDK, Python SDK, CLI, web interface, and, most recently, via email and Slack.
This new capability enables defenders to receive real-time notifications whenever a new vulnerability is added to VulnCheck KEV, helping you stay ahead of exploitation activity and respond more quickly to emerging threats.
VulnCheck Alerts Configuration Documentation: https://docs.vulncheck.com/alerts
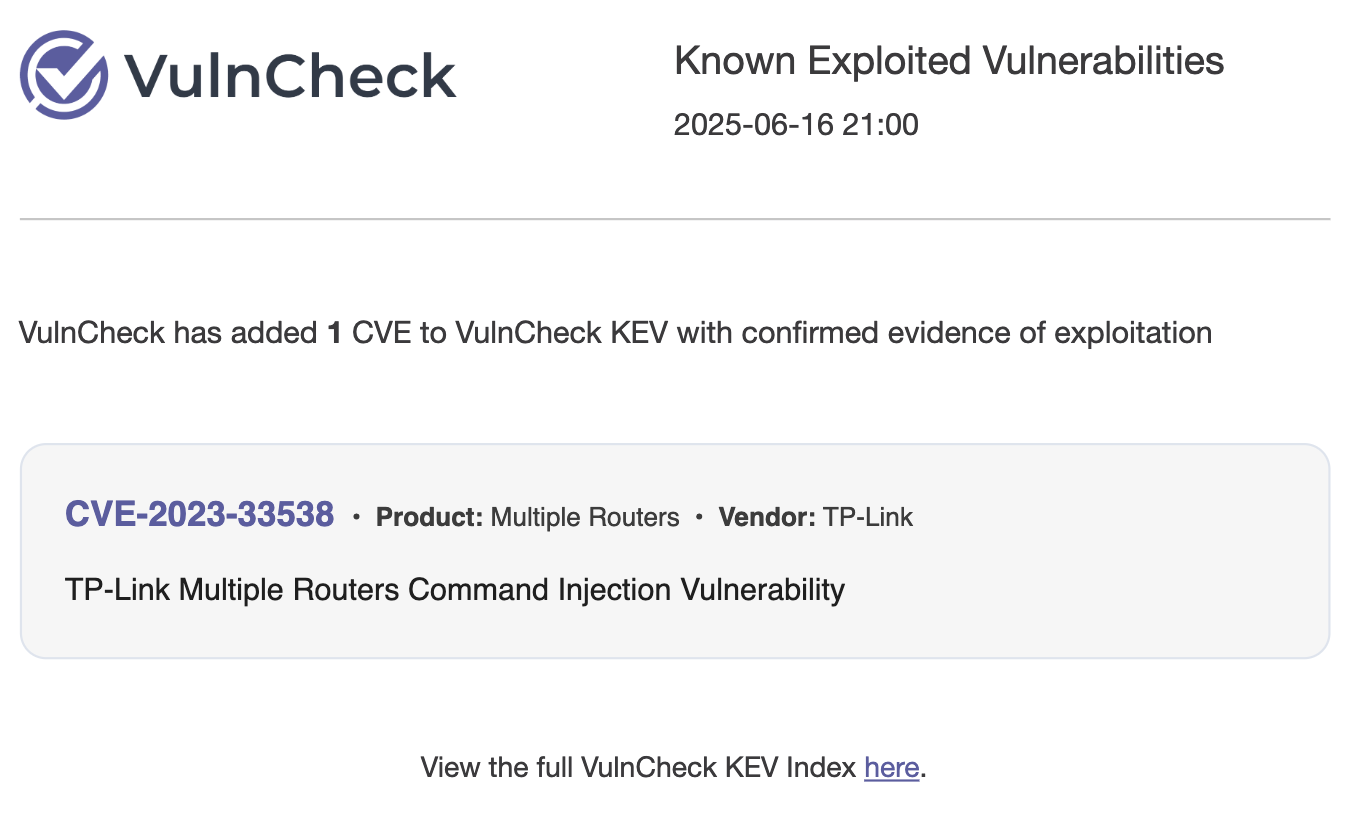
Subscribe to receive an email notification every time VulnCheck adds a new Known Exploited Vulnerability. Get exploitation intelligence delivered straight to your inbox.
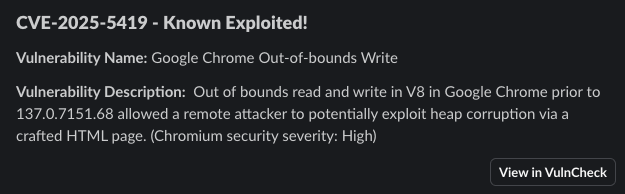
Configure Slack integration to receive real-time alerts in the channel of your choice whenever a new KEV is published. Keep your team in the loop and act fast without leaving your workspace.
Today, VulnCheck KEV includes over 3,700 known exploited vulnerabilities. It’s trusted by thousands of defenders worldwide and integrated into a growing number of security products. This milestone reflects our commitment to arming the security community with the data necessary to act quickly and effectively against the most significant threats.
VulnCheck provides timely, high-quality intelligence on exploited vulnerabilities, including:
Publicly referenceable exploitation evidence
Ransomware attribution Exploits from VulnCheck XDB (eXploit DataBase) – so defenders know what/how to block an attack.
We continue to support and complement CISA’s efforts. Still, our focus remains on delivering broader, faster, and more actionable exploitation intelligence to all defenders, without restrictions, while extending alerting and tooling that provides easy access to both VulnCheck community and commercial offerings..
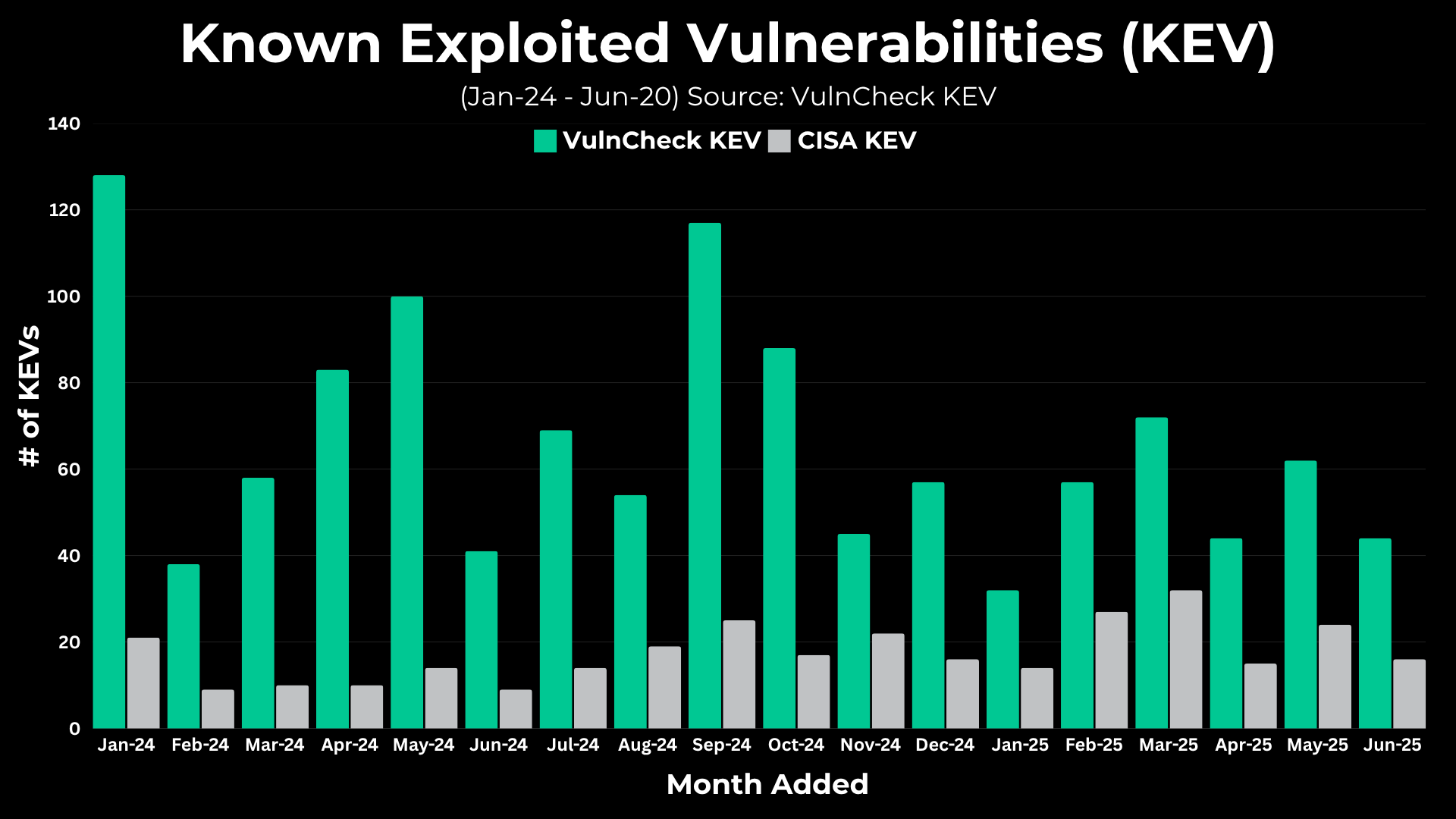
VulnCheck fully incorporates the CISA Known Exploited Vulnerabilities (KEV) catalog, but our intelligence goes further; we continuously aggregate exploitation evidence from hundreds of independent sources every day. For defenders, understanding the volume of new KEVs each month is crucial for capacity planning, prioritization and timely mitigation.
On average, security teams can expect VulnCheck KEV to identify between 40 and 100 CVEs per month that have confirmed evidence of exploitation. While most months fall within this range, there are occasional outliers.
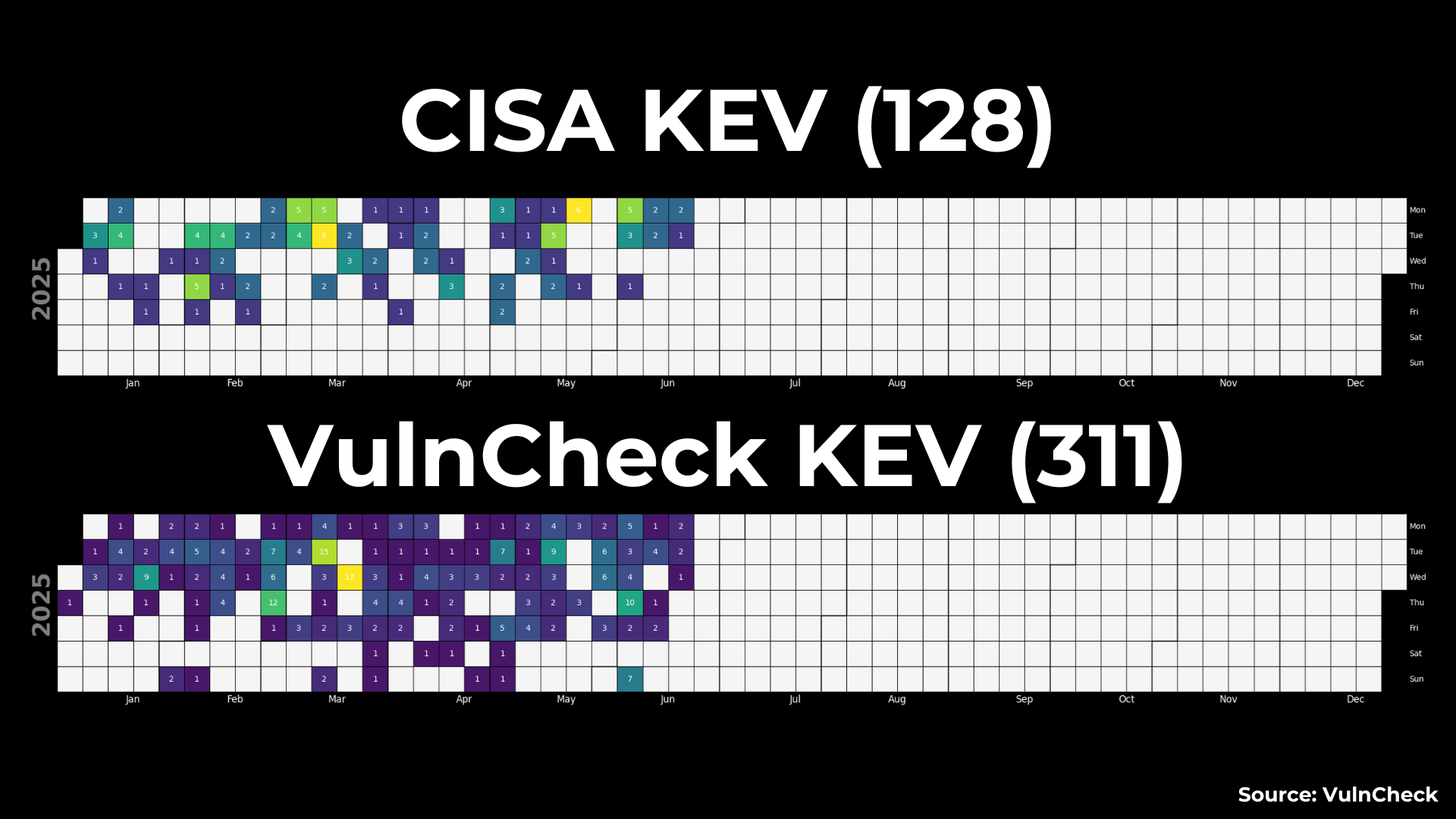
We have prioritized the automation of trusted sources such as CISA KEV, Shadow Server, and Microsoft MSRC, while our analyst team actively triages and validates exploitation evidence from additional channels. From January 24 through June 20 of this year, VulnCheck identified 311 CVEs with evidence of exploitation, resulting in 142% more KEVs than CISA in 2025.
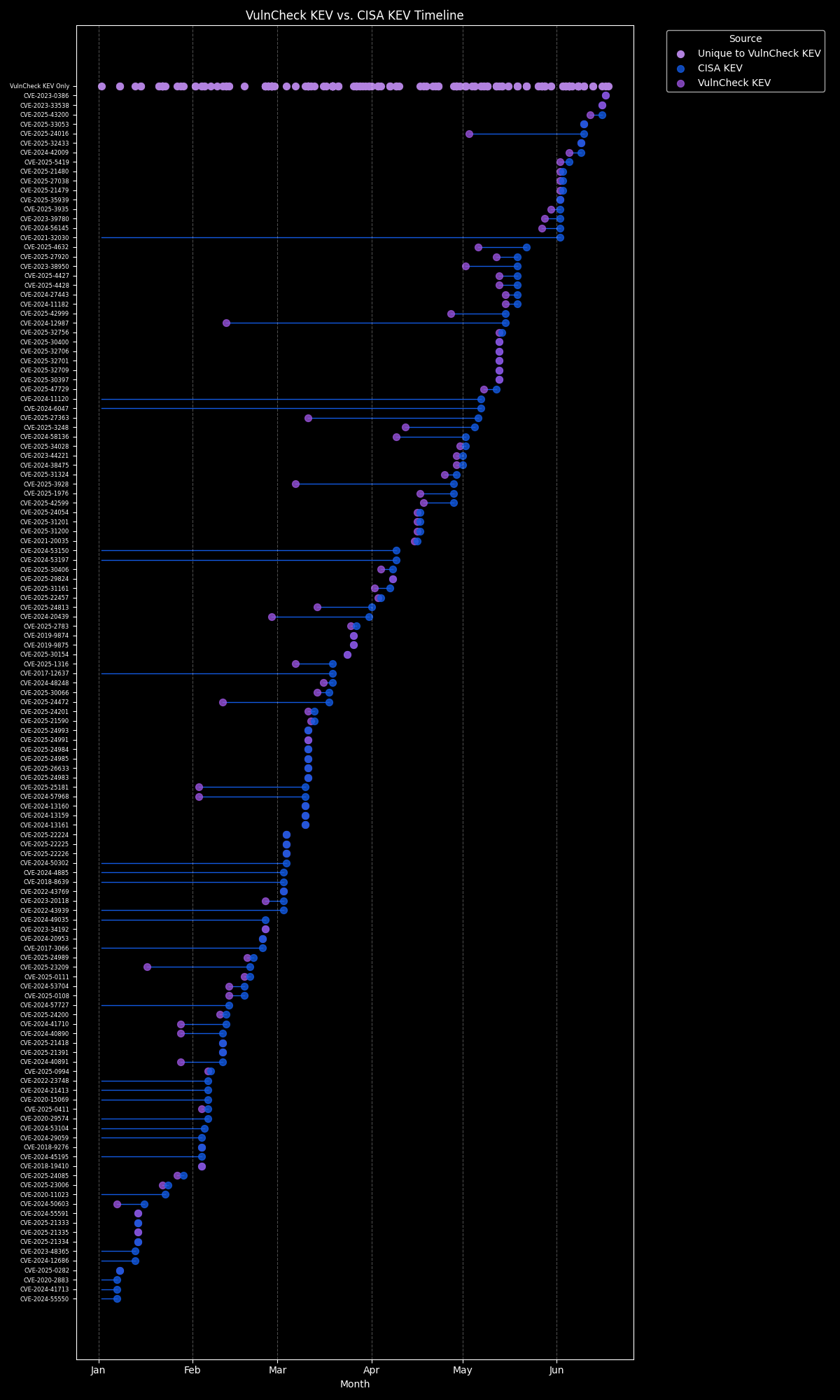
A key focus of VulnCheck KEV is speed, ensuring defenders receive early visibility when a vulnerability is being actively exploited in the wild. In 2025, VulnCheck added 311 exploited vulnerabilities to its KEV. Of those, only 128 have also been included in the CISA KEV so far. For 90 of the 128 vulnerabilities, representing 70.3%, evidence of exploitation existed days, months, or even years before their inclusion in the CISA KEV.
VulnCheck is helping organizations not just to solve the vulnerability prioritization challenge – we’re working to help equip any product manager, security team and threat hunting team to get faster and more accurate intelligence with infinite efficiency using VulnCheck solutions.
We knew that defenders needed better data, faster across the board, in our industry. So that’s what we deliver to the market. We deliver key insights on vulnerability management, exploitation and major trends we can extrapolate from our dataset to continuously support practitioners.
Join the VulnCheck Community today and get access to our VulnCheck NVD++ and the VulnCheck KEV in 30 seconds or less.
