- In 2024, VulnCheck’s Initial Access Intelligence (IAI) team delivered custom exploits and detection artifacts for 169 CVEs.
- Among these, 99 CVEs (58.6%) were actively exploited in the wild.
- For 27 CVEs, IAI coverage was provided before exploitation in the wild was reported, helping customers stay ahead of attackers by an average of two CVEs per month.
- Additionally, 17 CVEs not yet known to be exploited in the wild have malicious activity on GreyNoise tags or queries generated by the IAI team.
- Nine of the CVEs were zero-day vulnerabilities, with VulnCheck offering advanced warnings to its customers.
- The go-exploit framework saw significant improvements to the C2 system and a novel scanless feature.
VulnCheck delivers Exploit & Vulnerability Intelligence through a robust, automated system that gathers extensive metadata for every vulnerability documented across the internet.
Complementing this offering is VulnCheck’s Initial Access Intelligence. This offering focuseson carefully curated exploits, detections, scanners, and queries targeting the most critical vulnerabilities. Together, these services provide a balanced approach: broad, high-level insights for all vulnerabilities and in-depth analysis of the most significant threats.
Our Initial Access Intelligence aims to give users a complete understanding of the vulnerability and how to find it. The data isn’t targeted at any one demographic. Red teams, detection engineers, vulnerability management groups, attack surface management, incident response pros all would find this information useful. When possible, the IAI team develops:
- In-house exploits using our go-exploit framework, which incorporate asset discovery and version scanning capabilities.
- Search engine queries for finding exploitable systems. Currently supporting: Censys, Shodan, FOFA, ZoomEye, Google, and Baidu.
- GreyNoise queries for identifying ongoing attacks in the wild.
- Snort and Suricata network signatures for detecting active exploitation.
- PCAPs that capture exploitation attempts or malicious behavior.
- YARA rules tailored for identifying indicators of compromise.
- Vulnerable docker images to support testing and analysis efforts.
This extensive package equips users with the tools needed to not only detect vulnerabilities but also analyze and simulate exploitation scenarios.
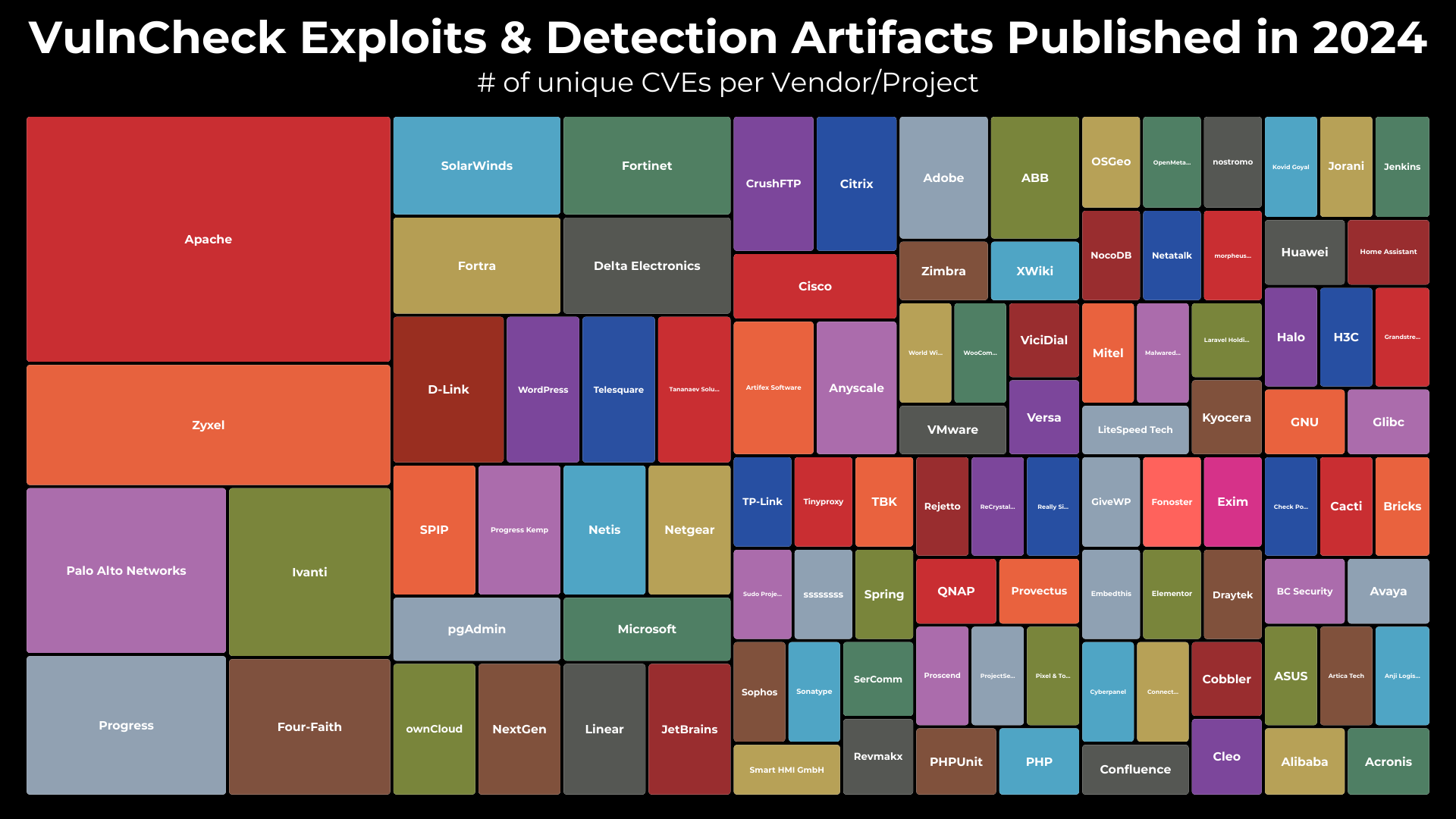
In 2024, the IAI team delivered coverage for 169 CVEs, covering 101 different vendors.
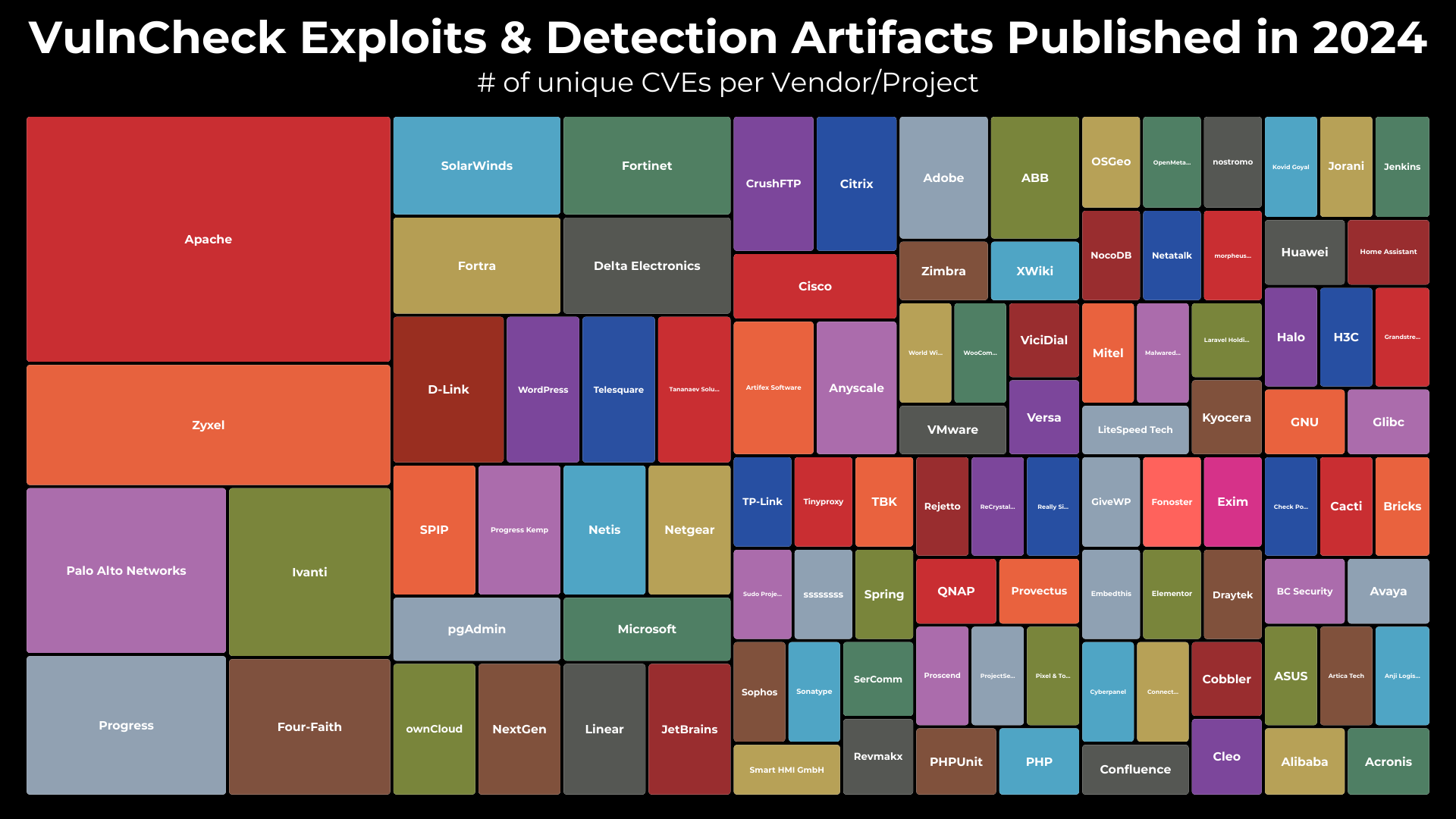
Leading the way in coverage, perhaps surprisingly to some, was the Apache Project. The Apache Project is the steward of many important software projects. There were so many that there were 17 Apache Project CVEs added to VulnCheck KEV in 2024 (only five of which are listed in CISA KEV).
Unsurprisingly, router and VPN manufacturers like Zyxel, Palo Alto Networks, Ivanti, and Fortinet followed Apache. These products are staples for any effective initial access team: they are challenging to monitor, not always easy to patch, and frequently exposed directly to the internet by design. Each of these vendors faced significant vulnerabilities in 2024 that warranted in-depth analysis by VulnCheck’s team.
Also notable on the graph are enterprise vendors like Fortra, Progress, and SolarWinds. These companies’ products are fixtures in enterprise environments but continue to feature prominently on known exploitable target lists year after year. This persistent pattern underscores the importance of monitoring these solutions for vulnerabilities that attackers are quick to exploit.
In total, the team would cover 99 vulnerabilities that had been exploited in the wild. Some of our coverage was in the “rapid response” style, like for CVE-2024-4577 (affecting PHP) in which the team delivered content one day before the CVE was even published. But the team also worked on important historical vulnerabilities like Sophos CVE-2020-25223 with the knowledge that attackers still pursue the vulnerability today.
The team has also generated coverage for 61 CVEs that have not been exploited in the wild yet, but have a high probability of being targeted in the future. That includes targets that have been in VulnCheck KEV before, like TeamCity (CVE-2024-23917), Spring Cloud (CVE-2024-37084), and Sonatype Nexus (CVE-2024-4956). That also includes some things off the beaten path, like Anyscale Ray (CVE-2023-6019), Traccar (CVE-2024-31214), and Laravel (CVE-2024-29291). The team focuses on not just what is well-known to US enterprises, but also global attackers.
Finally, as part of this work, the team inevitably finds zero-day vulnerabilities, of which we found nine in the last year. We handle these by providing detection to our customers and then working on disclosure with the vendor according to our disclosure policy.
Around May 2024, the Initial Access team doubled in size, resulting in a significant increase in monthly deliverables.
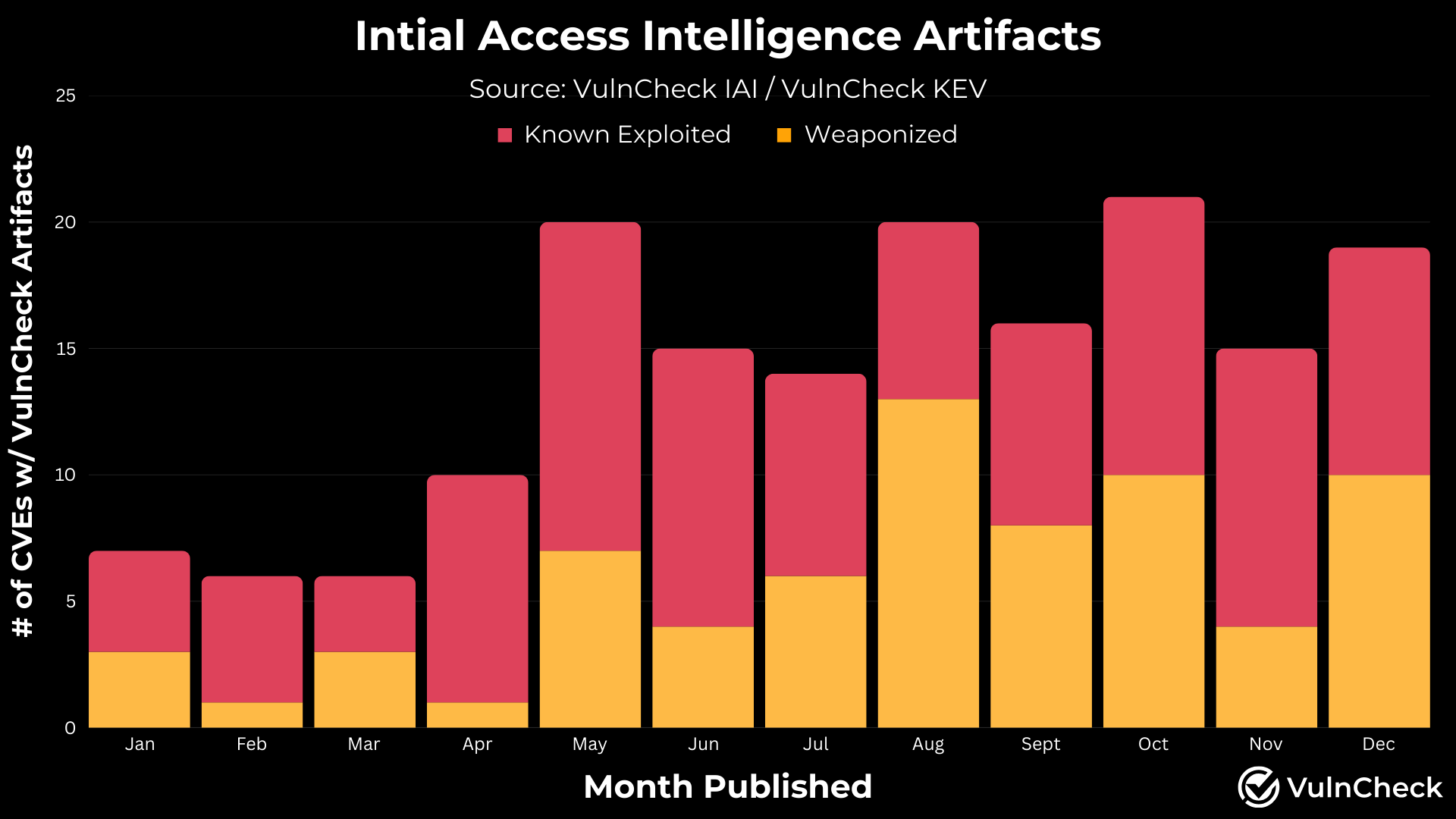
The team strives to consistently provide actionable intelligence on a minimum of four vulnerabilities per week (on average).By definition, all the vulnerabilities we work on are essential, so such detailed coverage is a boon to any organization.
The team doesn’t just focus on providing coverage for vulnerabilities. We are also intensely interested in how they can be exploited in real world scenarios. That requires maintenance of our exploit framework go-exploit. This year, we saw three major updates:
- In July, we updated go-exploit to allow for the exploits to share information across runs. This makes go-exploit the only exploit framework to scan HTTP targets without ever connecting to them!
- In October, we expanded the capabilities of go-exploit to include a new command and control feature called ShellTunnel which captures reverse shell traffic and routes it through an intermediary server before sending it on to the primary C2 server
- In September, we added external C2s to go-exploit. This feature enables community members to create C2 channels and payloads with direct integration into the go-exploit framework. The changes initially pushed in 1.25.0 give go-exploit the flexibility to import external C2 modules and define multiple types of external C2s.
Finally, the team loves to blog and share details of our work when possible. The following is a listing of the interesting blogs the IAI team helped develop in 2024:
The VulnCheck Initial Access team is always on the lookout for new exploitation in the wild. For more research like this, see our blogs, PaperCut Exploitation, ProjectSend CVE-2024-11680 Exploited in the Wild, Fileless Remote Code Execution on Juniper Firewalls
, and Does Confluence Dream of Shells?
Sign up to our website today to get free access to our VulnCheck KEV and request a trial of our Initial Access Intelligence and Exploit & Vulnerability Intelligence products.