VulnCheck is committed to accelerating visibility and improving data quality for defenders. We support the CVE Program and continue to expand our contributions by assigning CVE IDs to vulnerabilities observed by, discovered by, or reported to VulnCheck. In addition to assigning CVE IDs, VulnCheck also coordinates disclosure on behalf of security researchers through our free report a vulnerability service, which removes the burden of coordinated disclosure from the individuals who discover vulnerabilities.
At VulnCheck Research, we routinely observe, discover and analyze vulnerabilities that have not yet been assigned a CVE. These often include cases where there is a real-world threat, such as publicly available exploits, weaponized exploit code, or confirmed exploitation activity observed by VulnCheck canaries or third parties, including ShadowServer. The chart below highlights VulnCheck assigned CVEs to date and the threat profile of each vulnerability.

We frequently research, discover, and observe both new and older vulnerabilities that are known to be exploited, weaponized, or have publicly available proof-of-concept code. This chart illustrates that newer vulnerabilities are not the only ones posing real-world risk, and that assigning CVEs is important for both older and more recent issues.
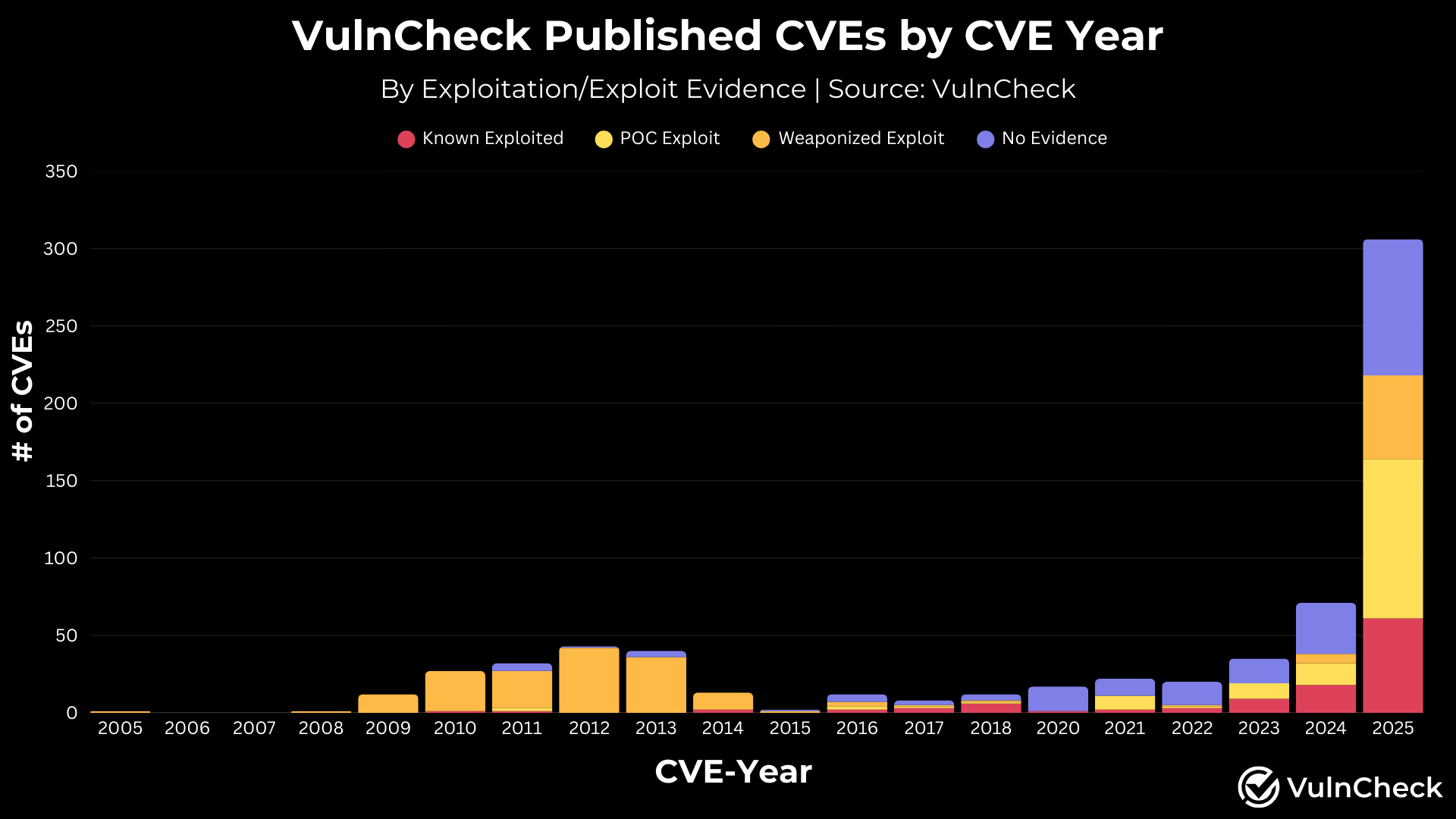
*In late June, we began assigning CVEs with the “CVE-YEAR” prefix based on the year the vulnerability originally became public. As a result, many known exploited or weaponized vulnerabilities that received a CVE with the “CVE-2025” prefix are actually older vulnerabilities.
As part of our broader effort to close gaps in CVE coverage, we partnered with ShadowServer to assign CVEs to vulnerabilities they observed being exploited in the wild, but that had never received an identifier. We issued CVEs for these vulnerabilities, which were actively exploited despite most having been disclosed in previous years.
We also assigned hundreds of CVEs to vulnerabilities with Metasploit modules to ensure that widely used and easily weaponized vulnerabilities receive the CVE coverage defenders rely on.
If you are interested in exploring older vulnerabilities that are actively being exploited, the ShadowServer Exploited Vulnerabilities Dashboard provides visibility into hundreds of such cases: ShadowServer Exploited Vulnerabilities Dashboard
We understand that coordinating with software suppliers can be challenging for security researchers. Our focus is on helping reduce the burden researchers face when reporting vulnerabilities. VulnCheck offers a free vulnerability reporting service that supports responsible disclosure.
Security researchers commonly encounter several obstacles, including limited responsiveness and in some cases, even combative behavior from software suppliers when researchers submit vulnerability reports.
Here is an example of a security researcher, Chocapikk, reporting a vulnerability to VulnCheck for responsible disclosure. After receiving no reply from the vendor, the security researcher reported the vulnerability to VulnCheck, who attempted to coordinate with the software vendor.
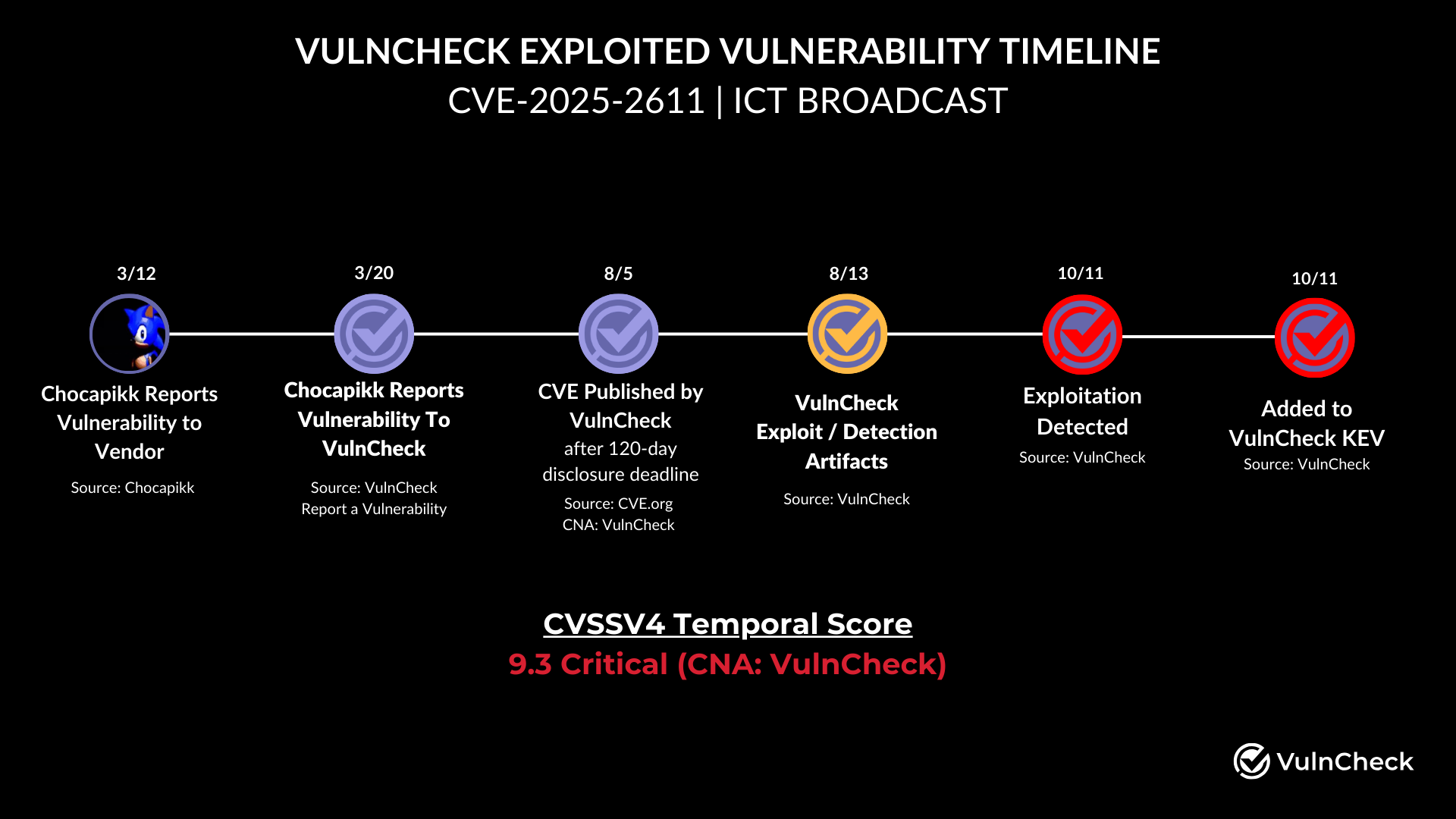
After coordinating with the researcher to disclose the vulnerability, VulnCheck issued a CVE, validated the vulnerability with a weaponized exploit and built detection rules. With these detection rules, VulnCheck was able to confirm real world exploitation of the vulnerability through our Canary Intelligence service and the vulnerability was added to VulnCheck KEV, a free service we provide to the security community.
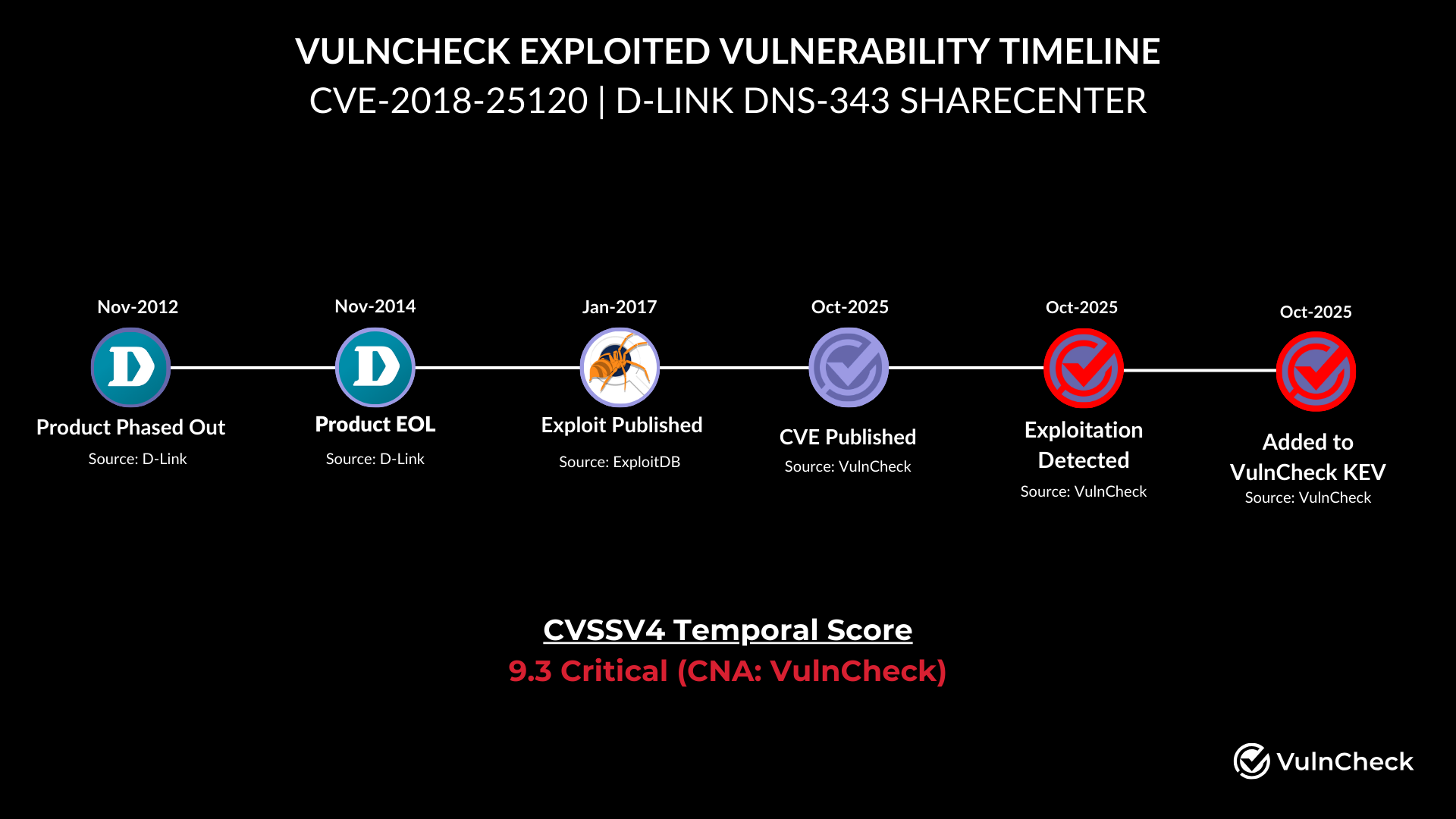
As our research team reviews hundreds of vulnerability intelligence sources, we often discover older publicly disclosed vulnerabilities that have no CVE assignment. Ensuring these issues receive a CVE is important because defenders rely on that visibility to understand and respond to potential threats.
For example, we published CVE-2018-25120 in October, a vulnerability that first had an exploit released in January 2017 and was later added to ExploitDB. Our analysis confirmed that this vulnerability was being used in the wild through VulnCheck Canary Intelligence. As a result, it was added to VulnCheck KEV, giving defenders critical insight into a real-world threat targeting technology that is more than a decade old.
Data quality is essential for CVE consumers, enabling them to efficiently identify, detect, and prioritize vulnerabilities across the various tools in their environments. We recognize both the importance of assigning CVEs to all vulnerabilities and of enriching those CVE records with meaningful, actionable information.
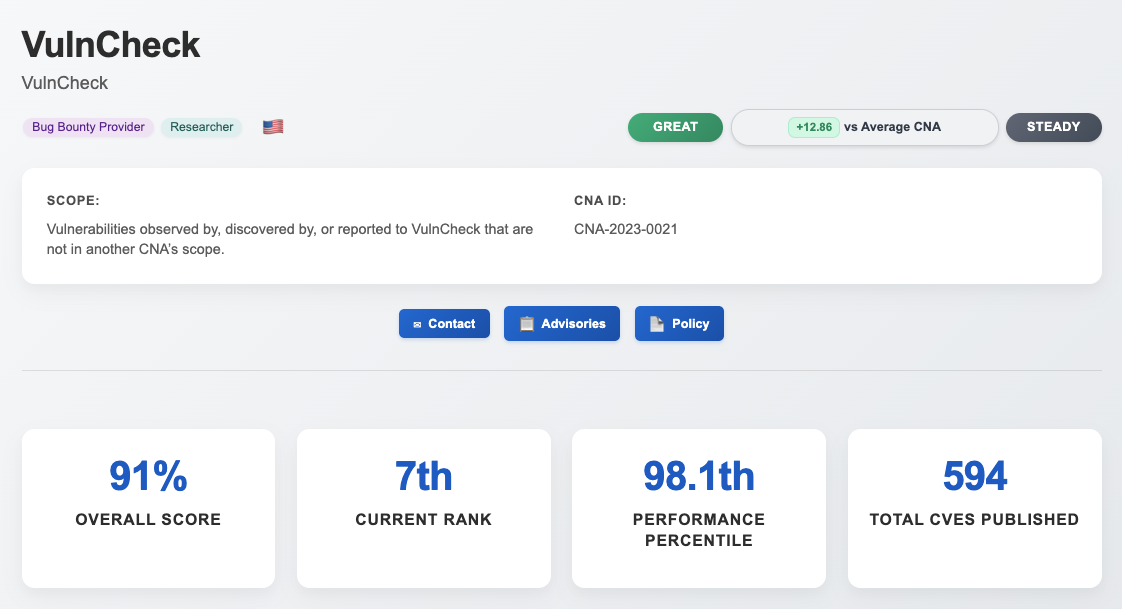
With the recent expansion of our vulnerability research team, we conducted an audit of our CVE records to ensure we consistently provide key enrichments, such as Patch Information and Common Platform Enumeration (CPE). Patch information helps defenders understand how to remediate vulnerabilities, while CPE data supports accurate detection and identification of vulnerabilities within an organization’s environment.
Following this audit, we used CNA ScoreCard to benchmark our record completeness against other CVE Numbering Authorities (CNAs) within the CVE Program. As a result of our efforts, we increased our overall completeness score to 91%, placing VulnCheck among the top seven CNAs. We issued the largest number of CVEs of any CNA achieving this level of CVE record completeness.
We are committed to investing in resources that give defenders broader visibility into real world threats through the CVE Program. To support this commitment, we have expanded our team and strengthened our public service and research efforts. This includes increasing our research capabilities, improving our CVE processing capacity, dedicating resources to coordinated disclosure, and investing in new tooling that will automate and streamline our ability to manage higher volumes of reported vulnerabilities and CNA CVE issuance.
VulnCheck is helping organizations not just to solve the vulnerability prioritization challenge – we’re working to help equip any product manager, CSIRT/PSIRT or SecOps team and Threat Hunting team to get faster and more accurate with infinite efficiency using VulnCheck solutions.
We knew that we needed better data, faster across the board, in our industry. So that’s what we deliver to the market. We’re going to continue to deliver key insights on vulnerability management, exploitation and major trends we can extrapolate from our dataset to continuously support practitioners.
Are you interested in learning more? If so, VulnCheck’s Exploit & Vulnerability Intelligence has broad threat actor coverage. Register and demo our data today.
