
Device code phishing attacks that abuse the OAuth 2.0 Device Authorization Grant flow to hijack accounts have surged more than 37 times this year.
In this type of attack, the threat actor sends a device authorization request to a service provider and receives a code, which is sent to the victim under various pretexts.
Next, the victim is tricked into entering the code on the legitimate login page, thus authorizing the attacker’s device to access the account through valid access and refresh tokens.
This flow was designed to simplify connecting devices that do not have accessible input options (e.g., IoT devices, printers, streaming devices, and smart TVs).
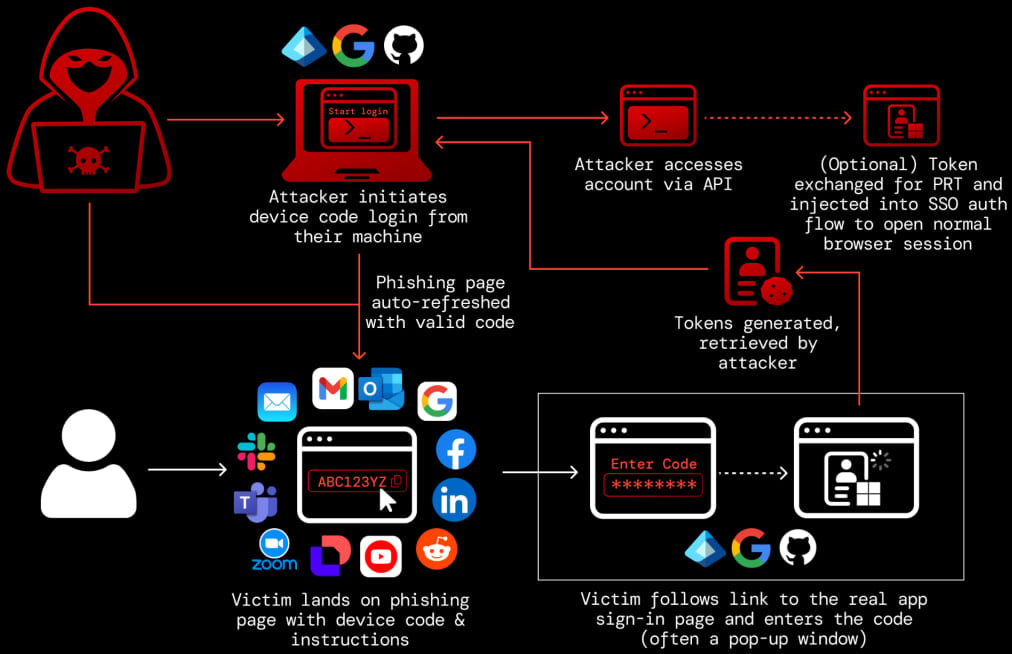
Source: Push Security
The device code phishing technique was first documented in 2020, but malicious exploitation was recorded a few years later, and has been used by both state-hackers and financially-motivated ones [1, 2, 3, 4].
Researchers at Push Security observed a massive increase in the use of these attacks, warning that they have been widely adopted by cybercriminals.
“At the start of March (2026), we’d observed a 15x increase in device code phishing pages detected by our research team this year, with multiple kits and campaigns being tracked — with the kit now identified as EvilTokens the most prominent. That figure has now risen to 37.5x.” – Push Security
Earlier this week, threat detection and response company Sekoia published research on the EvilTokens phishing-as-a-service (PhaaS) operation. The researchers underline that it is a prominent example of a phishing kit that “democratizes” device code phishing, making it available to low-skilled cybercriminals.
Push agrees that EvilTokens has been a major driver of the technique’s mainstream adoption, but notes that there are several other platforms competing on the same market, which could become more prominent in the event of law enforcement disrupting EvilTokens:
- VENOM – A closed-source PhaaS kit offering both device code phishing and AiTM capabilities. Its device code component appears to be an EvilTokens clone.
- SHAREFILE – A kit themed around Citrix ShareFile document transfers, using node-based backend endpoints to simulate file sharing and trigger device code flows.
- CLURE – A kit using rotating API endpoints and an anti-bot gate, with SharePoint-themed lures and backend infrastructure on DigitalOcean.
- LINKID – A kit leveraging Cloudflare challenge pages and self-hosted APIs, using Microsoft Teams and Adobe-themed lures.
- AUTHOV – A workers.dev-hosted kit using popup-based device code entry and Adobe document-sharing lures.
- DOCUPOLL – A kit hosted on GitHub Pages and workers.dev that mimics DocuSign workflows, including injected replicas of real pages.
- FLOW_TOKEN – A workers.dev-hosted kit using Tencent Cloud backend infrastructure, with HR and DocuSign-themed lures and popup-based flows.
- PAPRIKA – An AWS S3–hosted kit using Microsoft login clone pages with Office 365 branding and a fake Okta footer.
- DCSTATUS – A minimal kit with generic Microsoft 365 “Secure Access” lures and limited visible infrastructure markers.
- DOLCE – A Microsoft PowerApps-hosted kit with Dolce & Gabbana–themed lures, likely a one-off or red-team-style implementation rather than widely used.
It should be noted that other than Venom and EvilTokens, the names of the other phishing kits were given by Push researchers to track the malicious activity.
Push Security also published a video showing how the DOCUPOLL kit works. The threat actor uses DocuSign branding and a lure for an alleged contract, asking the victim to sign into the Microsoft Office application.
In total, there are at least 11 phishing kits offering cybercriminals this type of attack, all using realistic SaaS-themed lures, anti-bot protections, and abusing cloud platforms for hosting.
To block device-code phishing attacks, Push Security suggests that users disable the flow when not needed by setting conditional access policies on their accounts.
It is also recommended to monitor logs for unexpected device code authentication events, unusual IP addresses, and sessions.

