
A new malware-as-a-service called CrystalRAT is being promoted on Telegram, offering remote access, data theft, keylogging, and clipboard hijacking capabilities.
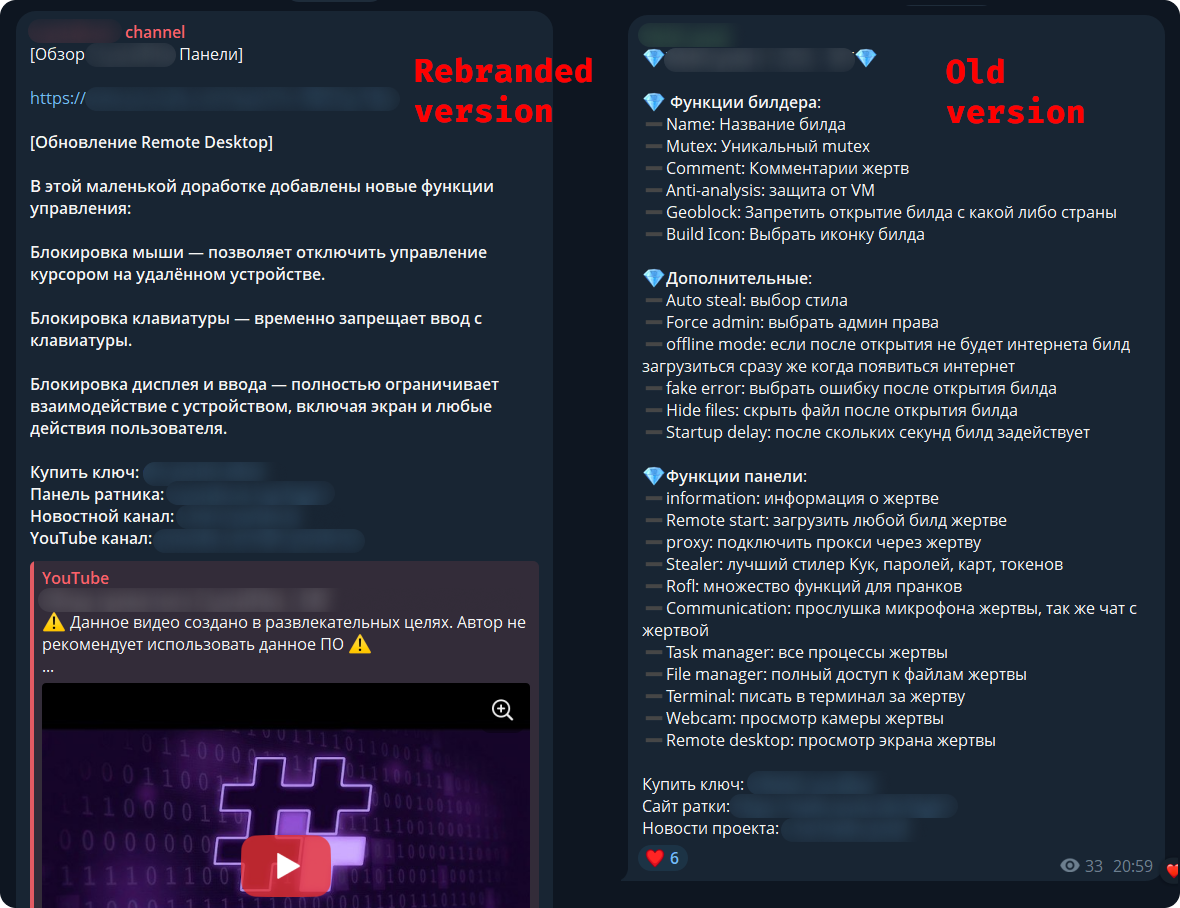
The malware emerged in January with a tiered subscription model. Apart from the Telegram channel, the MaaS was also promoted on YouTube, via a dedicated marketing channel that showcased its capabilities.
Kaspersky researchers say in a report today that the malware features strong similarities to WebRAT (Salat Stealer), including the same panel design, Go-based code, and a similar bot-based sales system.
CrystalX also includes an extensive list of prankware features designed to annoy the user or disrupt their work. Despite its “fun” side, CrystalX offers a large set of data theft capabilities.
Source: Kaspersky
CrystalX RAT details
Kaspersky says that the malware provides a user-friendly control panel and an automated builder tool that supports customization options, including geoblocking, executable customization, and anti-analysis features (anti-debugging, VM detection, proxy detection, etc.).
The generated payloads are zlib-compressed and encrypted with the ChaCha20 symmetric stream cipher for protection.
The malware connects to the command-and-control (C2) via WebSocket and sends info about the host for profiling and infection tracking.
CrystalX’s infostealer component, which Kaspersky found to be temporarily disabled as it is being prepared for an upgrade, targets Chromium-based browsers via the ChromeElevator tool, Yandex, and Opera. Additionally, the tool collects data from desktop apps such as Steam, Discord, and Telegram.
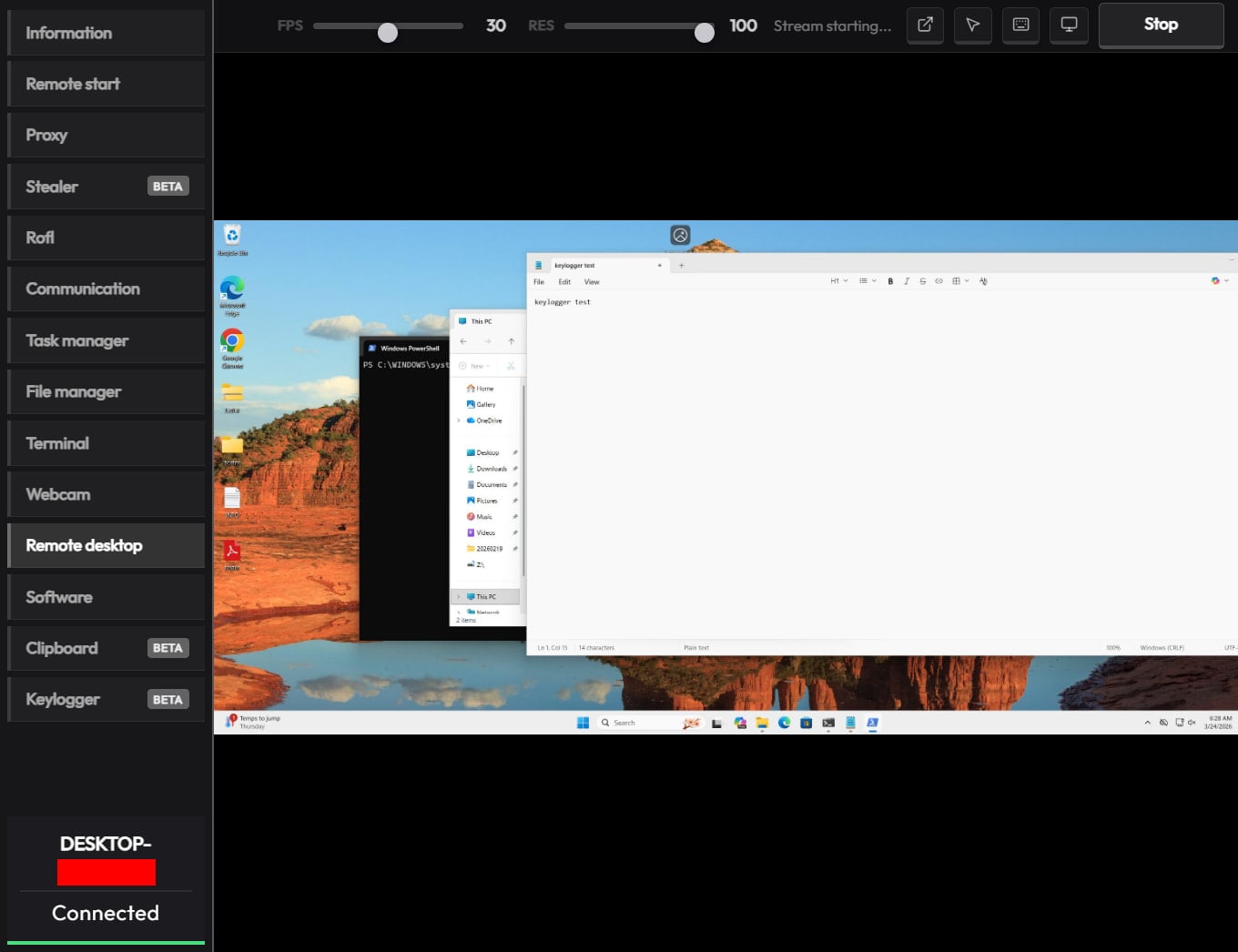
The remote access module can be used to execute commands via CMD, upload/download files, browse the file system, and control the machine in real time via built-in VNC.
The malware also exhibits spyware-like behavior, as it can capture video and audio from the microphone.
Finally, CrystalX features a keylogger that streams keystrokes in real time to the C2, and a clipper tool that uses regular expressions to detect wallet addresses in the clipboard and replace them with ones the attacker provides.
Source: Kaspersky
Putting some “fun” in the package
What sets CrystalX apart in the crowded MaaS space is its rich set of prankware features.
According to Kaspersky, the malware can do the following on infected devices:
- change desktop wallpaper
- alter display orientation to various angles
- force system shutdown
- remap mouse buttons
- disable input devices (keyboard/mouse/monitor)
- show fake notifications
- change cursor position on the screen
- hide various components (desktop icons, taskbar, the Task Manager, and the Command Prompt executable)
- Provide attacker-victim chat window
While the above features do not improve the attack’s monetization potential for cybercriminals, they certainly make the product distinctive, and could bait script kiddies and low-skilled/entry-level threat actors into getting a subscription.
Another reason for the prank features could be potential for victim manipulation, or even distraction, while the data theft modules run in the background.
To reduce the risk of malware infections, users are advised to exercise caution when interacting with online content and avoid downloading software or media from untrusted or unofficial sources.

