Start reporting your vulnerabilities through an organization equipped to handle Coordinated Vulnerability Disclosure (CVD) AND CVE assignment on your behalf. VulnCheck is here to service you, and we invite you to give it a whirl.
Security researchers often encounter obstacles when attempting to disclose vulnerabilities independently, whether discovered firsthand or observed in the wild. Each software supplier has its own disclosure process, which can introduce unnecessary friction and, over time, lead to frustration or abandonment of responsible disclosure altogether.
Common challenges we observe include:
- Limited or inconsistent supplier security resources
- Lack of responsiveness or a clear security contact
- Lengthy validation and remediation workflows
- Legal or policy concerns imposed on researchers
To address these issues, VulnCheck offers a free vulnerability reporting service designed to reduce the burden of disclosure and support researchers.
VulnCheck works directly with researchers to coordinate disclosure and manage communications with affected suppliers. This minimizes the time and effort you spend navigating disclosure processes while ensuring vulnerabilities are handled responsibly and consistently. All of this is done while ensuring proper credit is given to the researcher.
Simply submit the technical details of your vulnerability to VulnCheck. We do not require a specific format and aim to keep initial questions to a minimum. That said, providing thorough technical detail helps us validate the issue and proceed efficiently.
Once submitted, VulnCheck will handle the disclosure process and keep you informed at every stage.
You may submit a report via:
Web portal
Email: disclosure@vulncheck.com
Submissions can range from a public reference to an unidentified vulnerability to a full technical report with reproduction steps and proof of concept. At a minimum, we ask for enough information to either populate a CVE record or initiate coordination with the supplier.
When using the web form, you will be asked to provide:
- Vendor name
- Product name
- Affected and tested version(s)
- Vulnerability details: a clear description of the issue, its impact, and exploitation method, including reproduction steps and a proof of concept if available
- Whether you would like VulnCheck to coordinate disclosure on your behalf
- Whether you previously requested CVEs from MITRE without response
- Whether the vulnerability has already been publicly disclosed (with references, if applicable)
- Whether you plan to publish your findings on or after the coordinated disclosure date
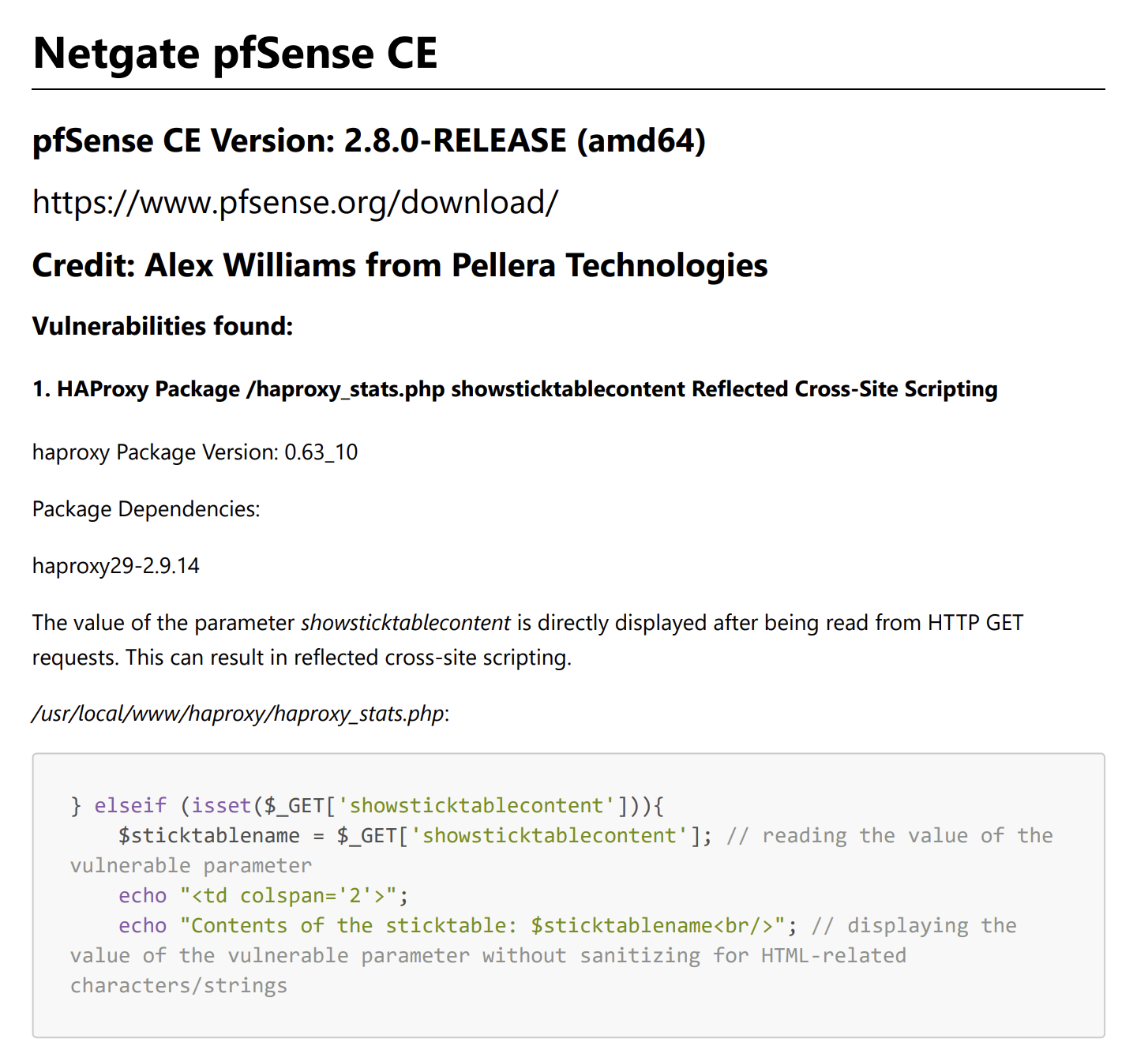
Here is an example of a comprehensive CVD submission presented in a format that enables us to go quickly from intake to vendor outreach:
You should expect an analyst to engage with you within 1 business day.
- CVE assignments for publicly disclosed issues or already-coordinated cases often occur within hours.
- For coordinated disclosures, VulnCheck’s average time from initial report to public disclosure is approximately 48 days, well within our 120-day disclosure policy.
Yes. After appropriate coordination, VulnCheck will issue a CVE directly or work with the most appropriate CVE Numbering Authority, depending on scope and ownership.
VulnCheck is a CVE Numbering Authority and can issue a CVE ID directly or coordinate assignment as needed.
No. VulnCheck does not provide financial incentives for vulnerability submissions.
There are limited circumstances in which VulnCheck will decline to coordinate disclosure:
- Not CVE-eligible
- We can help determine eligibility, but we do not coordinate disclosure for issues that do not qualify for CVE assignment.
- Unable to reproduce the issue
- If neither VulnCheck nor the supplier can validate the vulnerability after reasonable attempts, the case may be closed.
- Embargo violations
- If a researcher breaches an agreed embargo, VulnCheck may decline future coordination.
- Unethical or unauthorized discovery
- Vulnerabilities identified through testing on production systems without authorization will not be coordinated.
No – this service does not have any legal authority. We adhere to our Vulnerability Disclosure Policy. Participants are expected to respect mutual embargoes during coordinated disclosure. Researchers may choose to break an embargo at any time; however, VulnCheck reserves the right to refuse future service in such cases.
Sign up for the VulnCheck community today to get free access to our VulnCheck KEV, enjoy our comprehensive vulnerability data, and request a trial of our Initial Access Intelligence, IP Intelligence, and Exploit & Vulnerability Intelligence products.
