
Google has announced a new mechanism in Android called Advanced Flow, which will allow sideloading APKs from unverified developers for power users in a more secure manner.
The new system, scheduled to roll out this August, aims to allow installing Android apps from unverified developers while minimizing the risk of malware infections and scams, which caused an estimated $442 billion in losses last year, according to the Global Anti-Scam Alliance (GASA).
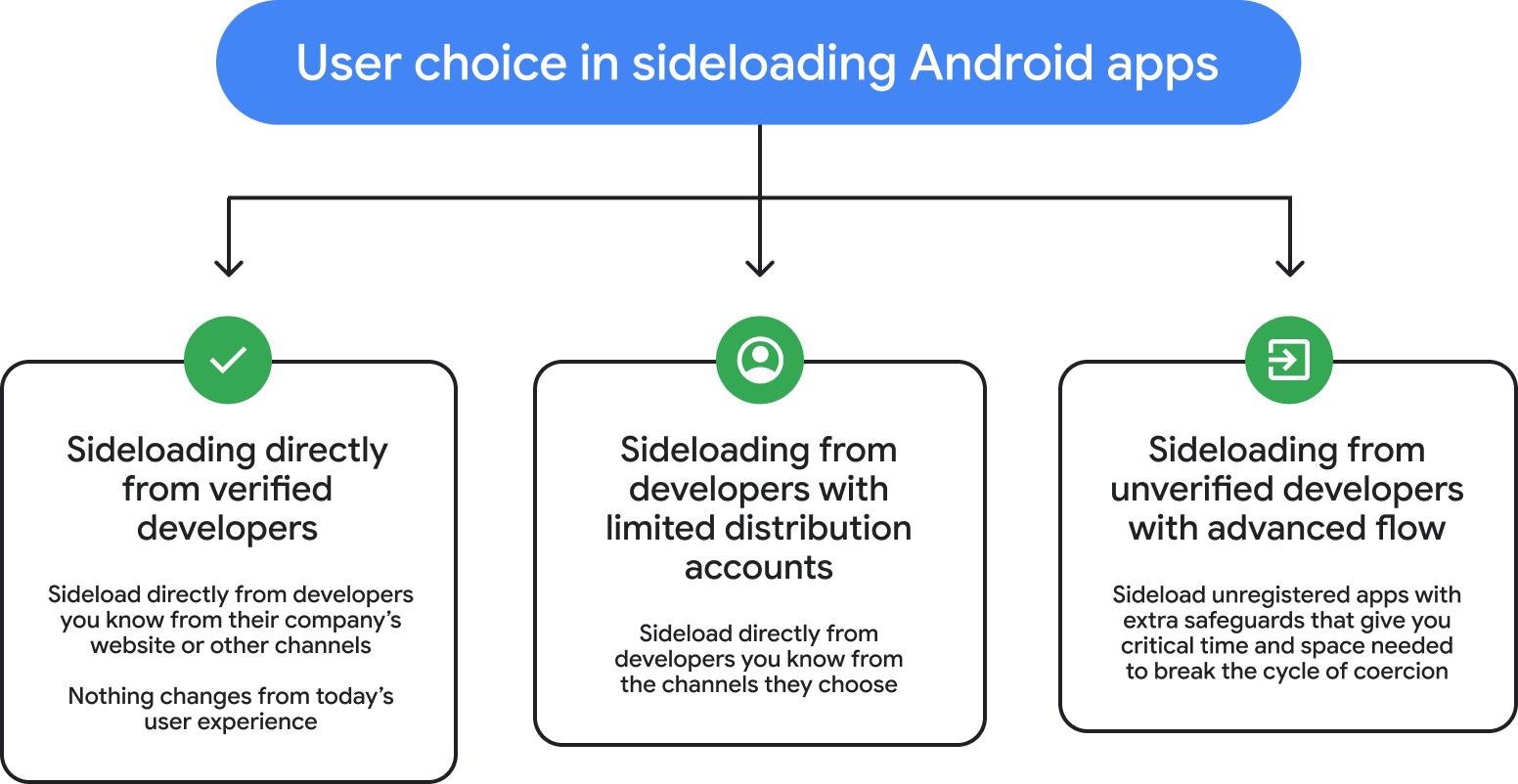
Source: Google
Power users who want to install APKs on their devices will have to go through a one-time process involving the following steps:
- Turn on Developer Mode from system settings
- Confirm they are not being coached by threat actors
- Restart the phone and reauthenticate
- Wait one day and then confirm that the modifications are legitimate
Then users can install apps from unverified developers and enable them for a week or indefinitely. Android will display a warning that the app is from an unverified developer.
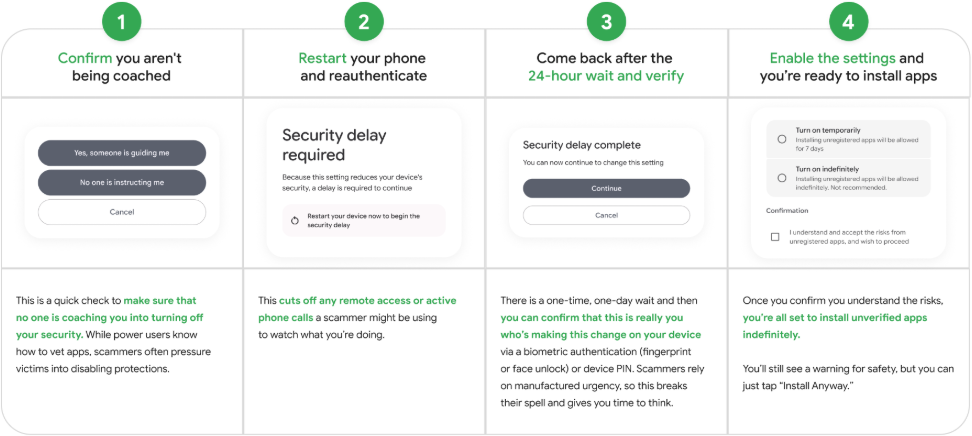
Source: Google
The process is designed to add friction and disrupt typical scamming tactics that trick people into installing unsafe apps on their devices by playing on the urgency of the operation.
“This flow is a one-time process for power users – it was designed carefully to prevent those in the midst of a scam attempt from being coerced by high-pressure tactics to install malicious software,” explains Google.
“In these scenarios, scammers exploit fear – using threats of financial ruin, legal trouble, or harm to a loved one – to create a sense of extreme urgency.”
“They stay on the phone with victims, coaching them to bypass security warnings and disable security settings before the victim has a chance to think or seek help.”
Google frames the Advanced Flow system as a safe compromise between Android’s openness and user protection, needed for a smooth transition to the new developer verification requirements scheme, first announced last August.
Developer verification is meant as an anti-malware measure, requiring all Android app publishers, regardless of the distribution method they use, to have their identity verified by Google; otherwise, the installation of their software on certified Android devices will be blocked.
Although Google retracted the original timeline for applying the new rule after backlash from the community, it didn’t abandon plans to implement the identity verification system.
This is still coming in August 2026, according to the latest announcement, and app developers are urged to visit this webpage for more information.

