
Hackers have been exploiting a critical vulnerability (CVE-2026-22679) in the Weaver E-cology office automation since mid-March to run discovery commands.
The attacks started five days after the software vendor released a security update to address the issue, and two weeks before disclosing it publicly.
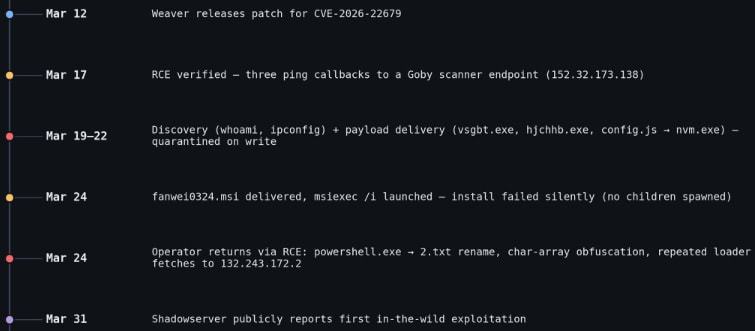
Researchers at threat intelligence company Vega documented the malicious activity and reported that the attacks lasted roughly a week, each with several distinct phases.
Weaver E-cology is an enterprise office automation (OA) and collaboration platform used for workflows, document management, HR, and internal business processes. The product is primarily used by Chinese organizations.
CVE-2026-22679 is a critical unauthenticated remote code execution flaw affecting E-cology 10.0 builds prior to March 12.
The flaw is caused by an exposed debug API endpoint that improperly allows user-supplied parameters to reach backend Remote Procedure Call (RPC) functionality without authentication or input validation.
This lets attackers pass crafted values that are ultimately executed as system commands on the server, effectively turning the endpoint into a remote command execution interface.
According to Vega, the attackers first checked for remote code execution (RCE) capabilities by triggering ping commands from the Java process to a Goby-linked callback, and then proceeded to multiple PowerShell-based payload downloads. However, all these were blocked by endpoint defenses.
Next, they attempted to deploy a target-aware MSI installer (fanwei0324.msi), but this failed to execute properly, and no follow-up activity was observed.
After those failed attempts, the attackers reverted to the RCE endpoint, using obfuscated and fileless PowerShell to repeatedly fetch remote scripts.
Throughout all attack phases, the threat actors executed reconnaissance commands, such as whoami, ipconfig, and tasklist.
Source: Vega
Vega explains that although the attackers had the RCE opportunity by exploiting CVE-2026-22679, they never established a persistent session on the targeted host.
Users of Weaver E-cology 10.0 are recommended to apply the security updates available through the vendor’s site as soon as possible.
“Every attacker process we observed is parented by java.exe (Weaver’s Tomcat-bundled Java Virtual Machine), with no preceding authentication,” explained Vega, adding that “the vendor fix (build 20260312) removes the debug endpoint entirely.”
No alternative mitigations or workarounds are listed in the official bulletin, so upgrading is the only recommendation.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls hold, and closes the remediation loop.

