Fraud prevention and user experience have long been treated as opposing forces: tighten security, and you risk alienating legitimate customers; loosen it, and you open the door to account takeovers, synthetic identities, and payment fraud. But modern threat intelligence platforms are dismantling that false choice.
Today’s most effective fraud prevention strategies operate silently in the background, combining dozens of risk signals in real time to block bad actors before they cause damage, without ever asking a legitimate user to jump through an extra hoop.
Security friction is not a neutral tax. Every unnecessary CAPTCHA, every step-up authentication prompt served to a legitimate user, and every false positive that blocks a good customer from completing a transaction carries a measurable cost. Cart abandonment rates spike when checkout flows become cumbersome.
New user registrations drop when signup forms are burdened with verification delays. And customer service costs rise when account recovery processes are opaque or slow.
At the same time, the cost of under-detection is catastrophic. The Association of Certified Fraud Examiners estimates that organizations lose approximately 5% of annual revenue to fraud each year.
Payment fraud, account takeover, promo abuse, and synthetic identity fraud are not edge cases – they are persistent, organized, and increasingly automated. Fraudsters are running bots, rotating proxies, and leveraging credential stuffing toolkits that would make any IT professional’s hair stand on end.

Fraud at Signup: The Battle for Clean Accounts
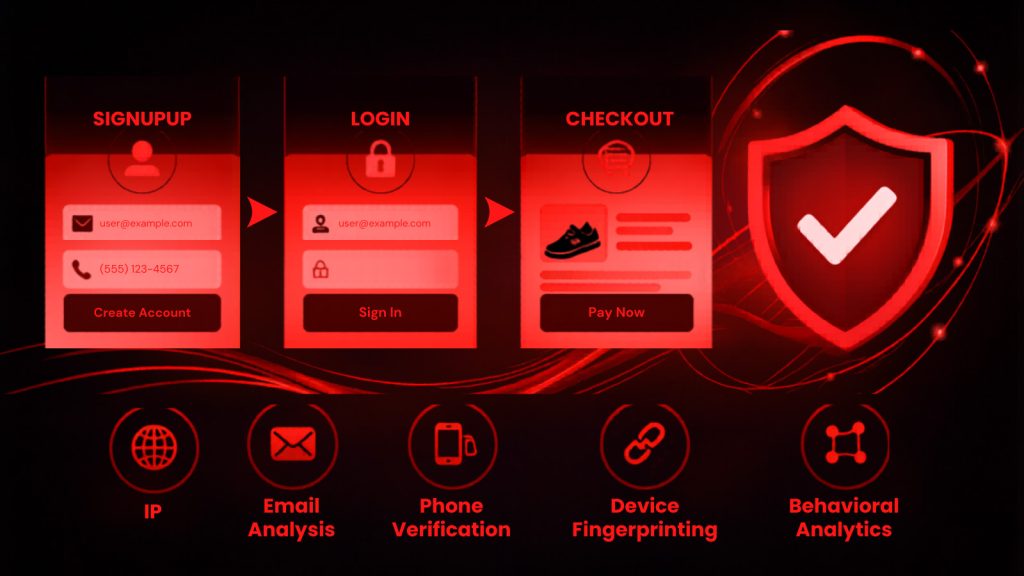
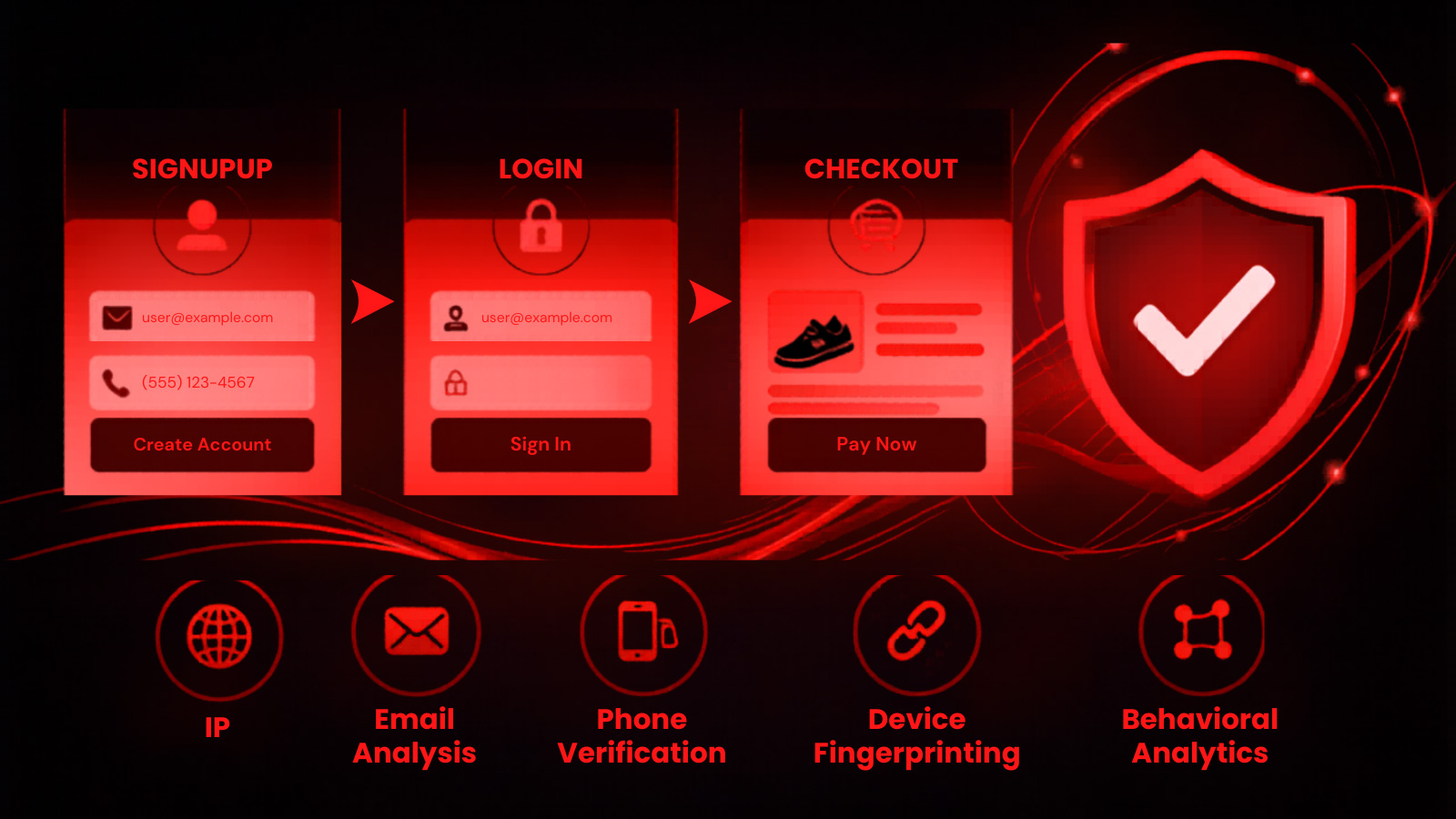
Signup is the highest-leverage intervention point in the fraud lifecycle. Stop a fraudster from creating an account, and you prevent every downstream attack that account would have enabled — account takeovers, payment fraud, promo abuse, referral fraud, and synthetic identity monetization.
The challenge is that signup is also the highest-volume, highest-visibility touchpoint for legitimate new users, making false positives especially damaging to business growth.
At signup, the signals available to a fraud team are rich but must be evaluated with speed. Email address analysis should go far beyond simple syntax validation.
Is the domain newly registered? Is the mailbox active and deliverable? Has this address appeared in breach databases? Is it associated with a pattern of fraudulent registrations?
Similarly, phone number intelligence should evaluate carrier type (VOIP vs. mobile), line activity, porting history, and whether the number has been flagged across fraud networks.
Fraud at Login: Defending the Account Layer
Login fraud – primarily account takeover (ATO) – represents one of the most damaging attack vectors in digital fraud. Credential stuffing attacks can compromise even accounts with strong original passwords if those credentials have been reused.
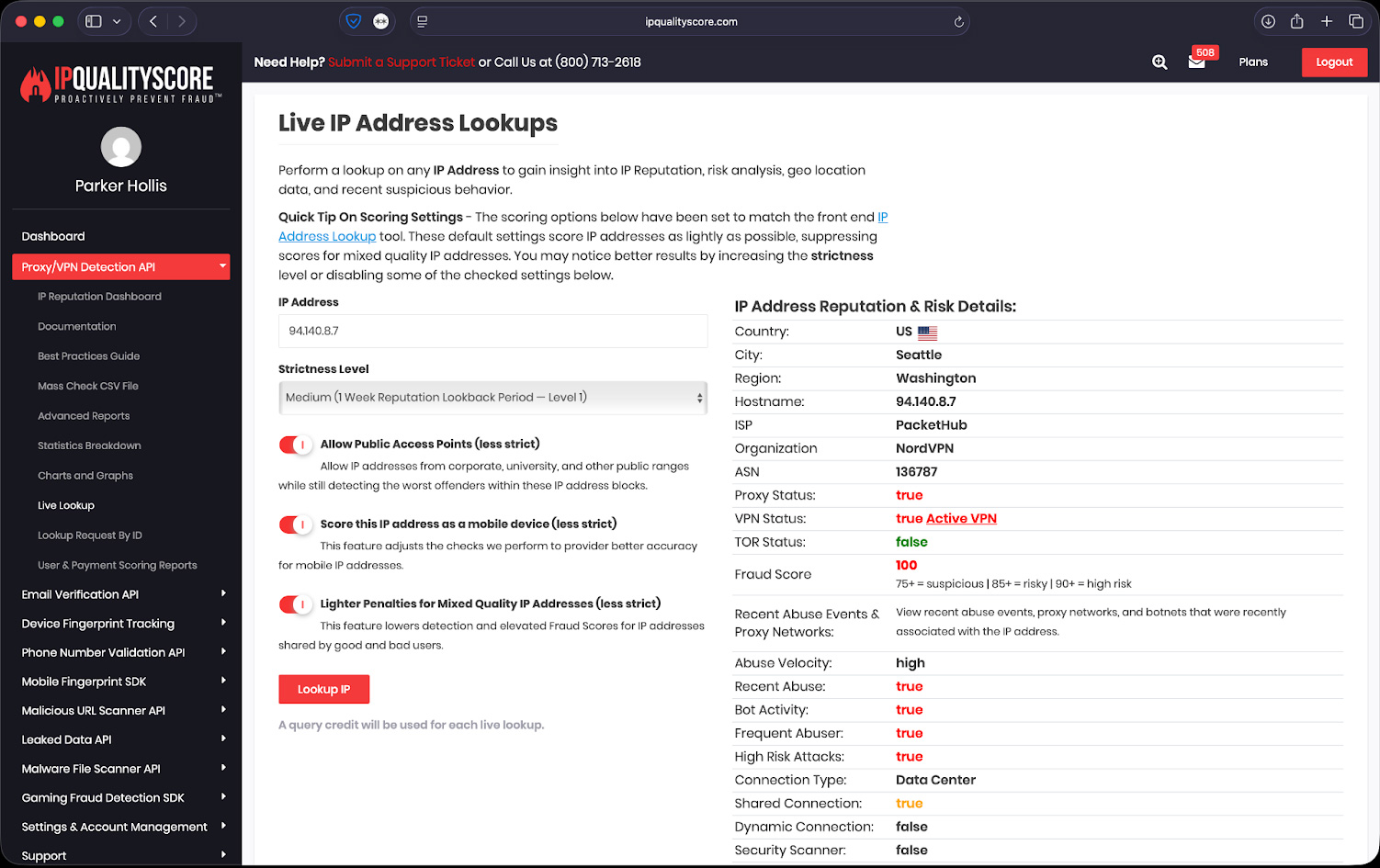
The scale of these attacks is staggering: automated toolkits can test hundreds of thousands of credential pairs per hour against a single target, and residential proxy networks make them difficult to block with traditional rate-limiting or IP filtering.
Frictionless ATO prevention requires detecting the anomaly without punishing the legitimate user. Legitimate logins follow recognizable patterns: familiar devices, typical geographic locations, consistent time-of-day windows, normal session velocities.
Deviations from these patterns, even subtle ones, can be powerful risk signals when combined with network and identity intelligence.
Learn how to apply the right fraud checks at the right time without slowing users down, request sample risk scoring data from IPQS for free today.
See how multi-layered detection identifies bots, emulators, and high-risk sessions to proactively prevent fraud before it hits your bottom line.
Fraud at Checkout: Protecting Revenue at the Finish Line
Checkout fraud sits at the intersection of identity fraud, payment fraud, and social engineering. At checkout, the convergence of identity and transaction signals is most powerful.
The email and phone attached to a new order should be evaluated for consistency with the claimed billing identity. The IP address should be checked not just for proxy use but for geographic consistency with the shipping address.
Device signals should be compared against the account’s login history. Payment instrument intelligence, including velocity across merchants, prior chargeback rates, and card BIN data, adds a financial risk dimension that purely identity-based approaches cannot provide.
How IPQS Operationalizes Frictionless Intelligence
IPQS represents the class of platform-level fraud intelligence tools that operationalize the multi-signal, layered approach described above.
While offering discrete point solutions for IP reputation, email validation, or phone verification, IPQS operates as a unified intelligence platform that evaluates all of these signals through a shared data model and returns composite risk scores optimized for real-time decision-making.
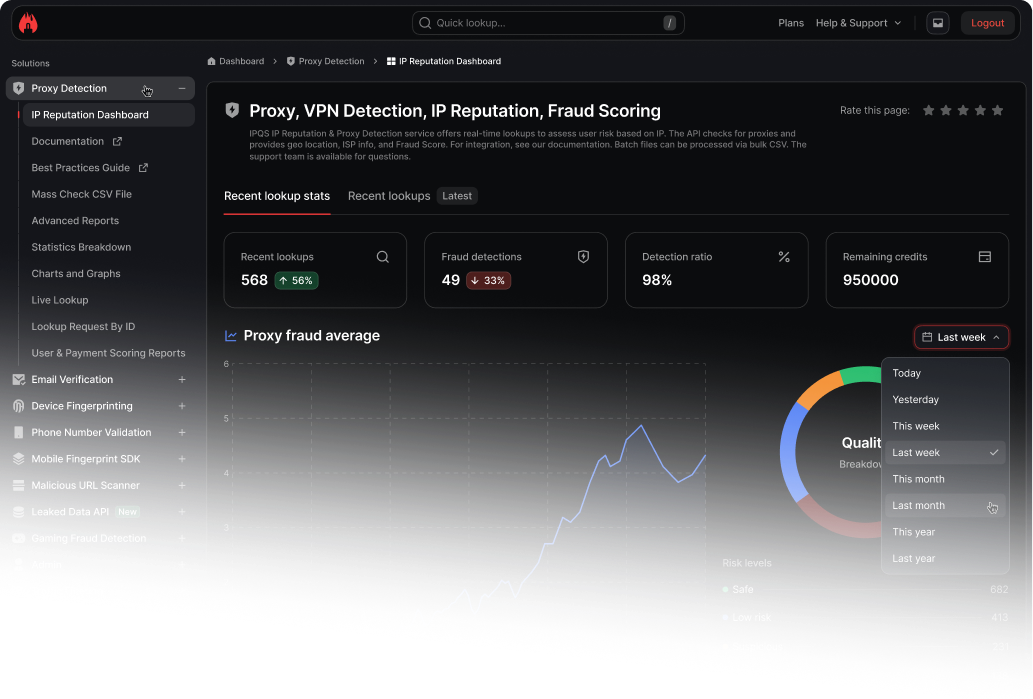
A tiered response strategy maps risk score ranges to response types that are proportional to both the likelihood and severity of fraud at each threshold.
High-risk sessions can be challenged with targeted, lightweight verification, a single tap push notification to a registered device, for example, rather than a full OTP flow. Only the highest-risk sessions, where the composite evidence strongly suggests fraud, should result in hard blocks or declines.
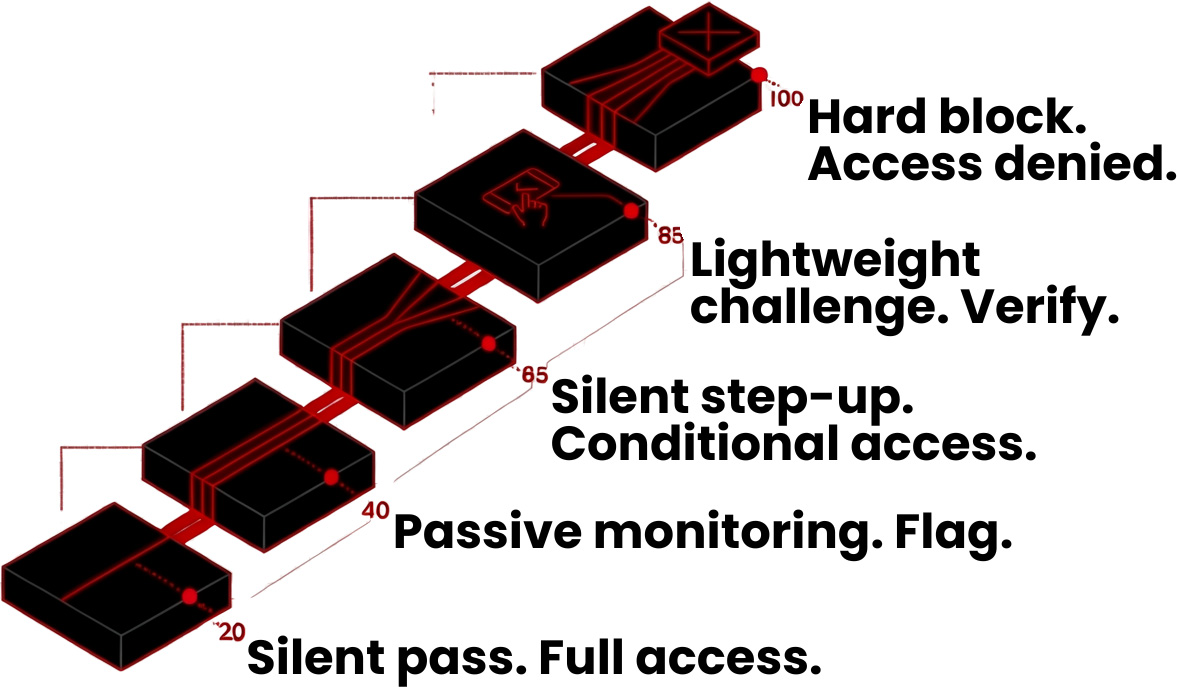
For the vast majority of legitimate users, who will score in the low-risk tier, the experience is entirely seamless. For the small cohort of genuinely high-risk sessions, the additional friction is proportional, defensible, and targeted at exactly the sessions that warrant it.
IPQS provides unparalleled fraud prevention by producing the freshest and richest data available.
We offer real-time fraud prevention solutions with unmatched accuracy through our cyberthreat honeypot network, covering IP, device, email, phone number, and URL scanning worldwide. Our suite of tools provides tight security with customizable scoring settings and a simple fraud score for easy detection.
Book a free fraud consultation with one of our specialists today!
Sponsored and written by IPQS.