
A set of 26 malicious apps on Apple App Store impersonate popular wallets, such as Metamask, Coinbase, Trust Wallet, and OneKey, to steal recovery or seed phrases and drain them of cryptocurrency assets.
The threat actor used multiple methods to imitate official products, including typosquatting and fake branding, to lure users in China into downloading them.
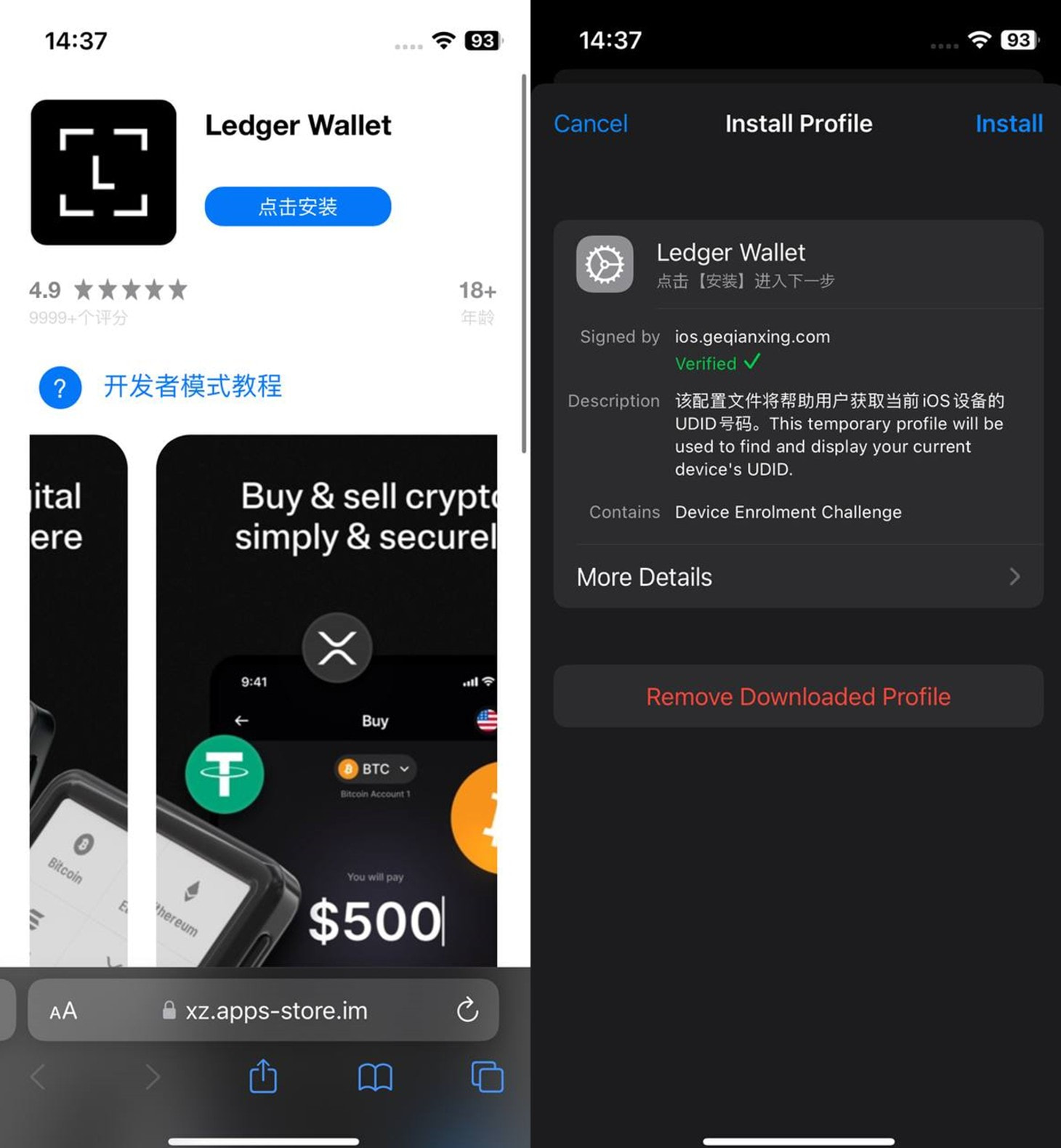
Because such apps are restricted in the country, the attacker published them as games or calculator apps, likely in the hope of being perceived by the users as a trick to bypass the bans in the country.
Kaspersky researchers say that all 26 fake apps are part of the same campaign, which they named FakeWallet, and associate them with the SparkKitty operation that has been running since last year.
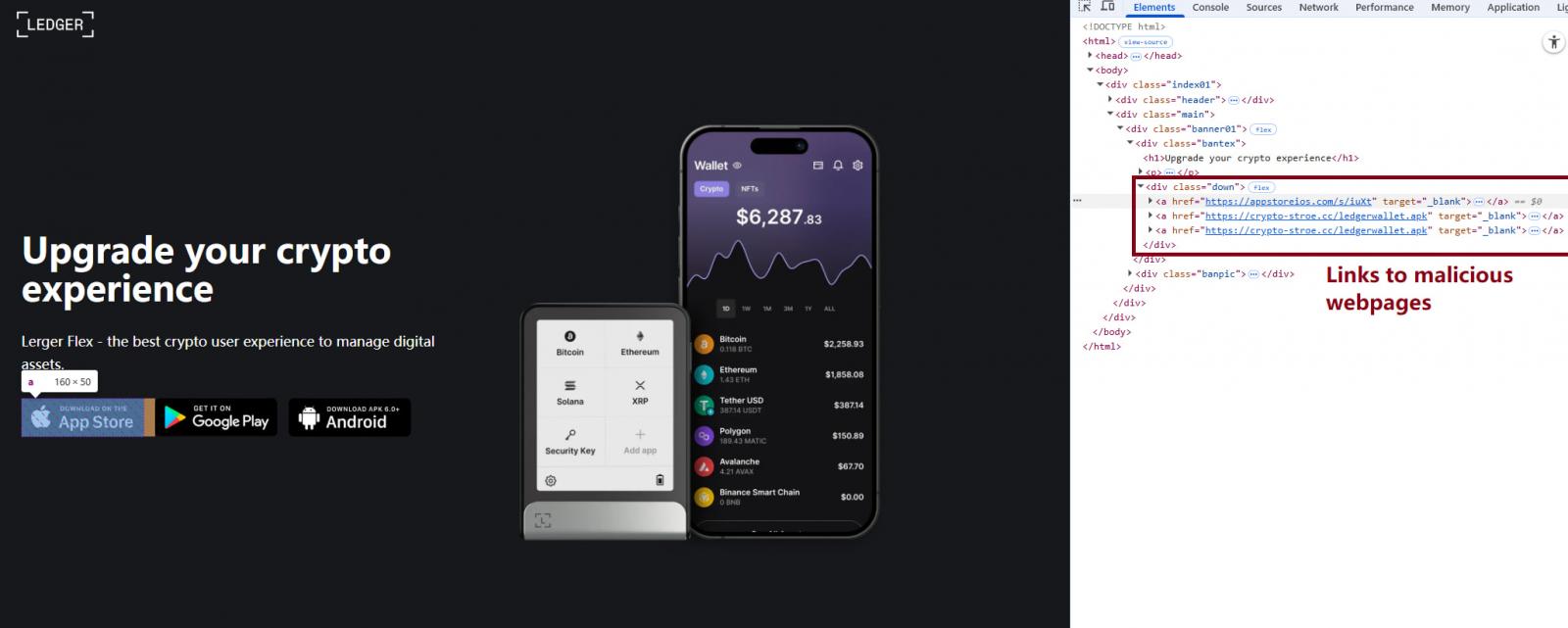
Once opened, the apps redirect users to phishing pages designed to appear as legitimate portals for the crypto services.
Source: Kaspersky
These sites convince victims to download trojanized wallet apps using iOS provisioning profiles, a legitimate enterprise feature that is abused to sideload malware onto their devices. The same technique was also observed in SparkKitty.
Source: Kaspersky
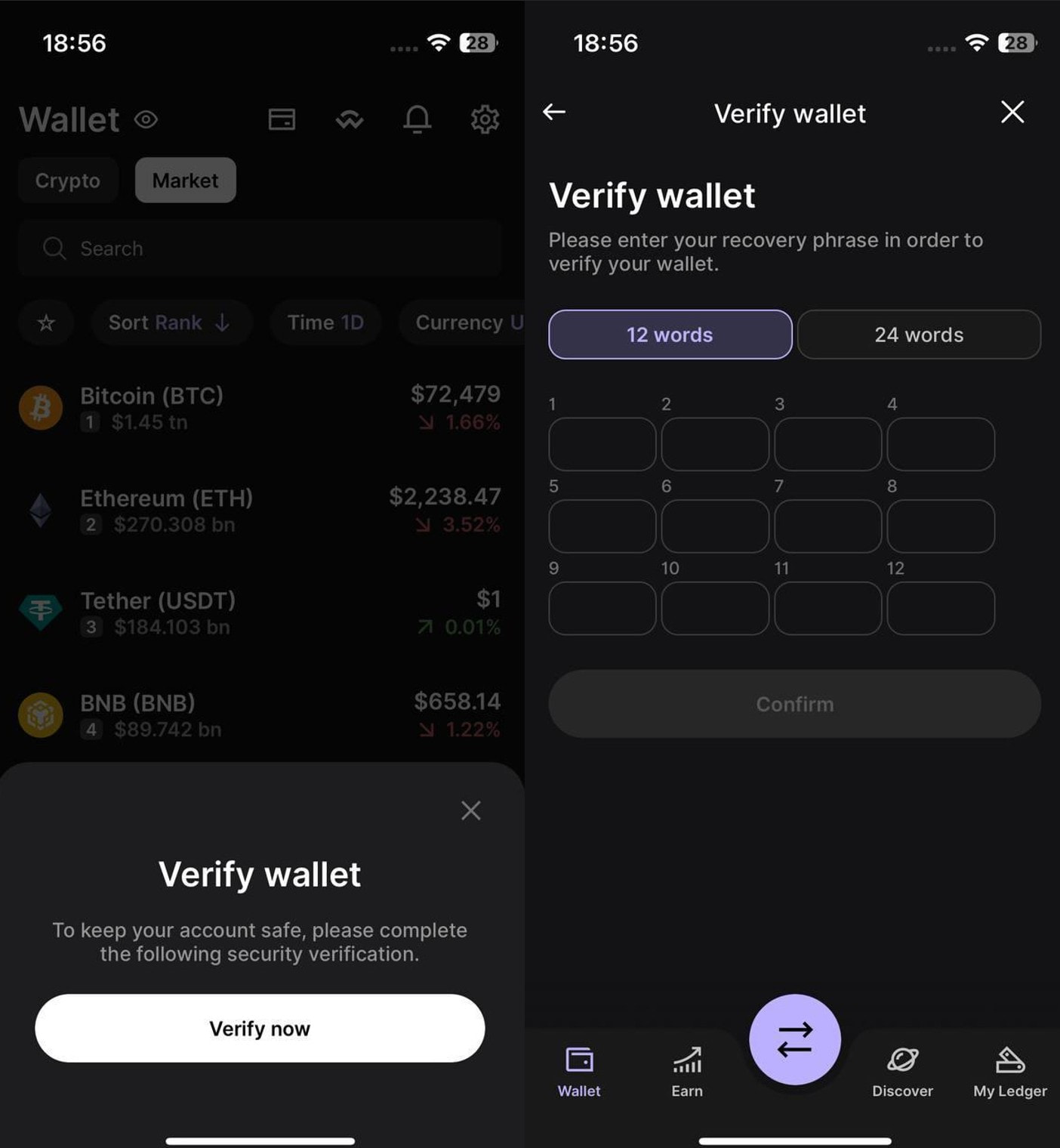
The trojanized apps contain additional code that intercepts mnemonic phrases during wallet setup or recovery screens, encrypts them with RSA and Base64, and sends them to the attacker.
For cold wallets like Ledger, attackers rely on in-app phishing prompts that trick users into manually entering their seed phrases via fake security verification screens.
These phrases, which are only held by the rightful wallet owner, are intended for wallet porting/recovery to new devices and require no further confirmation or passwords.
Hence, threat actors can use them to restore the victim’s wallet on their own devices and drain the wallet without the possibility of recovering the funds.
Source: Kaspersky
Kaspersky noted that the campaign primarily targets users in China. However, the malware itself has no geographic restrictions, so it could affect users globally if the operators decide to expand their targeting scope.
Cryptocurrency holders are advised to double-check the publisher of the apps they download, even from official app stores, and use only the links provided on the official website.
Last week, it was uncovered that a fraudulent Ledger app that made it into Apple’s App Store stole $9.5 million worth of cryptocurrency from 50 macOS users.
Apple has removed all 26 FakeWallet apps from the App Store following Kaspersky’s responsible disclosure.
BleepingComputer has contacted Apple with questions about the threat actor’s process to bypass the company’s App Store verfications but we have not received a response by publication time.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls hold, and closes the remediation loop.


