Stake-holder Specific Vulnerability Categorization (SSVC) is a methodology for prioritizing vulnerabilities that has created at Carnagie Melon’s Software Engineering Institute largely been popularized by the Cybersecurity & Infrastructure Security Agency encouraging federal agencies and enterprises to modernize their approach to vulnerability management. In 2024, CISA released Vulnrichment which is an effort to provide the enrichment of SSVC decisions on CVE records which has set a foundational example on how to implement SSVC.
After hearing from federal agencies and enterprise organizations adopting SSVC across their vulnerability management program, we decided to set out to automate the creation of SSVC decisions across all CVEs to help make SSVC adoption a more realistic possibility.
Example CISA SSVC Decision Tree
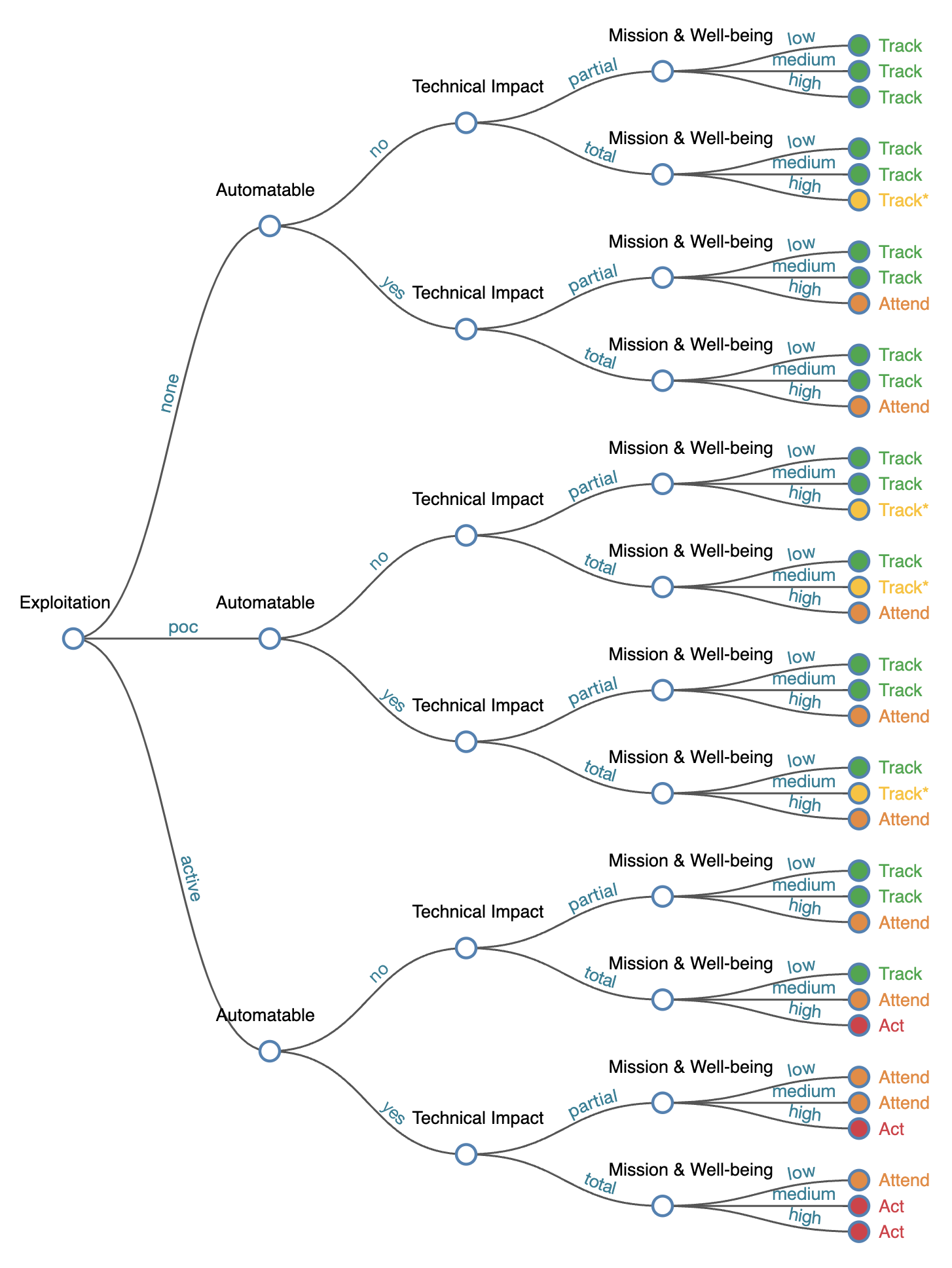
Source: CISA SSVC
We’ve focused on automating the creation of SSVC decisions that can be generated through existing vulnerability and exploitation intelligence which include the Exploitation, Automatable and Total Impact decisions. We follow the same structure for the SSVC decisions as outlined in CISA’s SSVC Guide.
Exploitation Decision
| Value | Definition |
|---|---|
| None | There is no evidence of active exploitation and no public proof of concept (PoC) of how to exploit the vulnerability. |
| Public PoC | A known POC exploit exists which is sourced from VulnCheck’s Exploit Intelligence. This includes Proof-of-Concept, Commercial and Weaponized exploits. |
| Active | Reliable evidence that cyber threat actors have used the exploit in the wild sourced from VulnCheck KEV which references credible sources. |
Technical Impact Decision
| Value | Definition |
|---|---|
| Partial | CVSS metrics are used to identify when a decision node is Technical Impact:Partial. When CVSS metrics are not equal to ConfidentialityImpact: “HIGH”, IntegrityImpact: “HIGH” the vulnerabilities is marked with Total. |
| Total | CVSS metrics are used to identify when a decision node is Technical Impact:Total. When CVSS metrics are equal to ConfidentialityImpact: “HIGH”, IntegrityImpact: “HIGH” the vulnerabilities is marked with Total. |
Automatable Decision
| Value | Definition |
|---|---|
| Yes | CVSS metrics are used to identify when a decision node is automatable. The CVE is marked as automatable when the vulnerability is not a memory corruption vulnerability and the CVSS metrics are equal to AttackVector: “NETWORK”, PrivilegesRequired: “NONE”, UserInteraction: “NONE”, AttackComplexity: “LOW”. |
| No | Vulnerabilities without the conditions listed for automatable = Yes are marked as non-automatable. |
We’ve included CISA Vulnrichment alongside VulnCheck SSVC so you can compare between VulnCheck and CISA. Notable differences include a significant increase in CVE coverage, more exploitation evidence and more timely SSVC node generation.
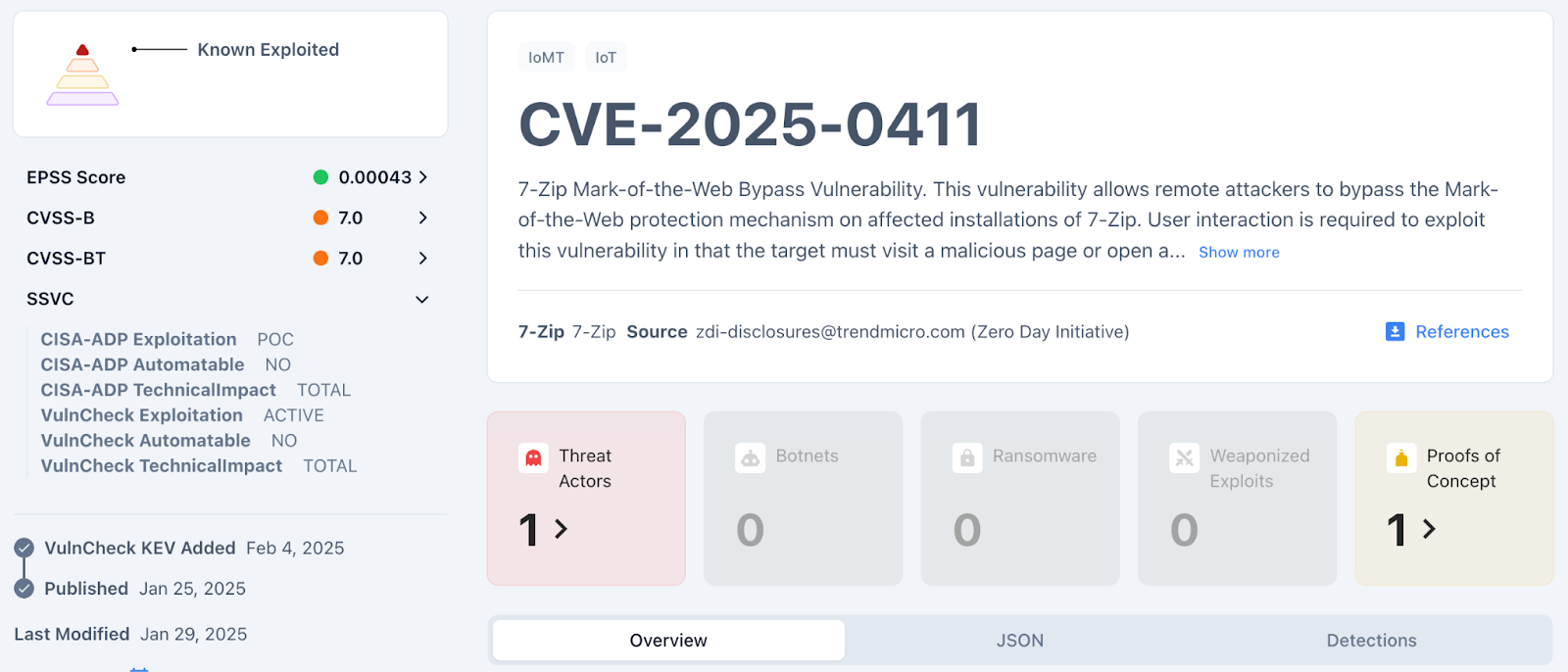
VulnCheck-NVD2 API Response Example
"ssvc": [
{
"source": "CISA-ADP",
"exploitation": "POC",
"automatable": "NO",
"technicalImpact": "TOTAL"
},
{
"source": "VulnCheck",
"exploitation": "ACTIVE",
"automatable": "NO",
"technicalImpact": "TOTAL"
}
],
VulnCheck currently has SSVC coverage for 244,866 CVE’s while CISA Vulnrichment has SSVC coverage for only 64,142 CVE’s.
We’ve calculated a CISA / VulnCheck match rate for each decision node that is calculated using the % match for VulnCheck of CISA Vulnrichment. It’s worth mentioning that when we did a manual audit of mismatched decisions we often found inconsistencies in the decision generated by CISA that we believe would increase our match rates if these decisions were correct. This is common for manually generated vulnerability data that often lacks data validation.
| CISA SSVC Decision | VulnCheck SSVC Decision Match Rate |
|---|---|
| exploitation:active | 100% |
| exploitation:poc | 86.7% |
| exploitation:none | 90.6% |
| automatable:yes | 88.9% |
| automatable:no | 92.3% |
| technicalimpact:total | 95.2% |
| technicalimpact:partial | 85.6% |
VulnCheck is helping organizations not just to solve the vulnerability prioritization challenge – we’re working to help equip any product manager, security team and threat hunting team to get faster and more accurate intelligence with infinite efficiency using VulnCheck solutions.
We knew that we needed better data, faster across the board, in our industry. So that’s what we deliver to the market. We’re going to continue to deliver key insights on vulnerability management, exploitation and major trends we can extrapolate from our dataset to continuously support practitioners.
Are you interested in learning more? If so, VulnCheck’s Exploit & Vulnerability Intelligence has the broadest coverage.
