
The MuddyWater Iranian hackers disguised their operations as a Chaos ransomware attack, relying on Microsoft Teams social engineering to gain access and establish persistence.
Although the attack involved credential theft, persistence, remote access, data exfiltration, extortion emails, and an entry on the Chaos leak portal, the attackers used infrastructure and techniques associated with the MuddyWater attacks.
Rapid7 researchers believe that the ransomware component was likely used to conceal the actual cyber-espionage operation and to complicate attribution.
“The strategy highlights the convergence between state-sponsored intrusion activity and criminal tradecraft, where a big “tell” lies in the techniques that were deployed – and those that weren’t. This strategy suggests the primary goal was not financial gain,” explains Rapid7.
Despite the facade, Rapid7 has moderate confidence in attributing the incident to MuddyWater, a threat group also known as Static Kitten, Mango Sandstorm, and Seedworm.
The conclusion is based on infrastructure overlap, a specific code-signing certificate that the state-sponsored group used to sign Stagecomp and Darkcomp malware attributed to the threat actor, and various operational tradecraft.
MuddyWater is an Iranian state-sponsored cyber-espionage group, notorious for long-term network intrusion campaigns that align with the country’s Ministry of Intelligence and Security (MOIS).
The Chaos is a ransomware-as-a-service (RaaS) operation that emerged in 2025 and is known for big-game hunting attacks, double-extortion tactics, and social engineering campaigns mostly targeting organizations in the United States.
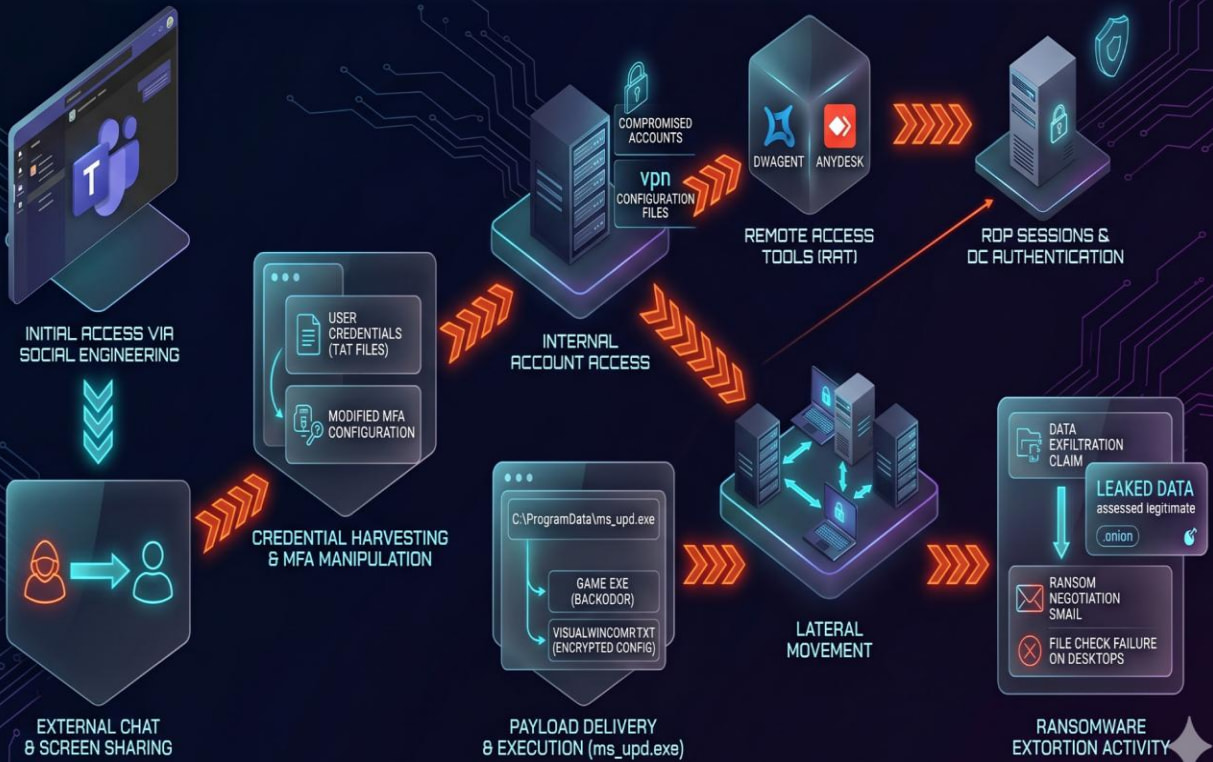
Attack progression
The intrusion Rapid7 examined started through Microsoft Teams social engineering, where the attackers initiated chats with employees, established screen-sharing sessions, harvested credentials, manipulated multi-factor authentication (MFA) settings, and, in some cases, deployed AnyDesk for remote access.
Credential theft occurred either via phishing pages masquerading as Microsoft Quick Assist or by tricking victims into typing their passwords into local text files.
After compromising accounts, the attackers authenticated to internal systems, including a domain controller, and established persistence using RDP, DWAgent, and AnyDesk.
Next, they leveraged a malware loader (ms_upd.exe) to drop a custom backdoor (Game.exe), disguised as a Microsoft WebView2 application.
The malware features anti-analysis and anti-VM checks, and supports 12 commands, including PowerShell and CMD command execution, file upload and deletion, and persistent shell access.
Source: Rapid7
Rapid7 notes that MuddyWater has used ransomware in the past to mask its cyber-espionage operations. In late 2025, the threat actor deployed Qilin ransomware in an attack against an Israeli organization.
The researchers suggest that the threat group might have pivoted to a different ransomware branding following the attribution of that late 2025 to MOIS operatives.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls hold, and closes the remediation loop.

