
A phishing campaign delivered through Google sponsored search results is targeting credentials for ManageWP, GoDaddy’s platform for managing fleets of WordPress websites.
The threat actor is using an adversary-in-the-middle (AitM) approach where the fake login page acts as a real-time proxy between the victim and the legitimate ManageWP service.
ManageWP is a centralized remote administration platform for WordPress websites, enabling users to manage multiple sites from a single panel instead of logging into separate dashboards. Common users include web developers, web agencies managing client sites, and enterprises.
Researchers at Guardio Labs warn that the fake result is displayed above the real one for the ‘managewp’ query, luring users who rely on Google to find the URL for logging into ManageWP.
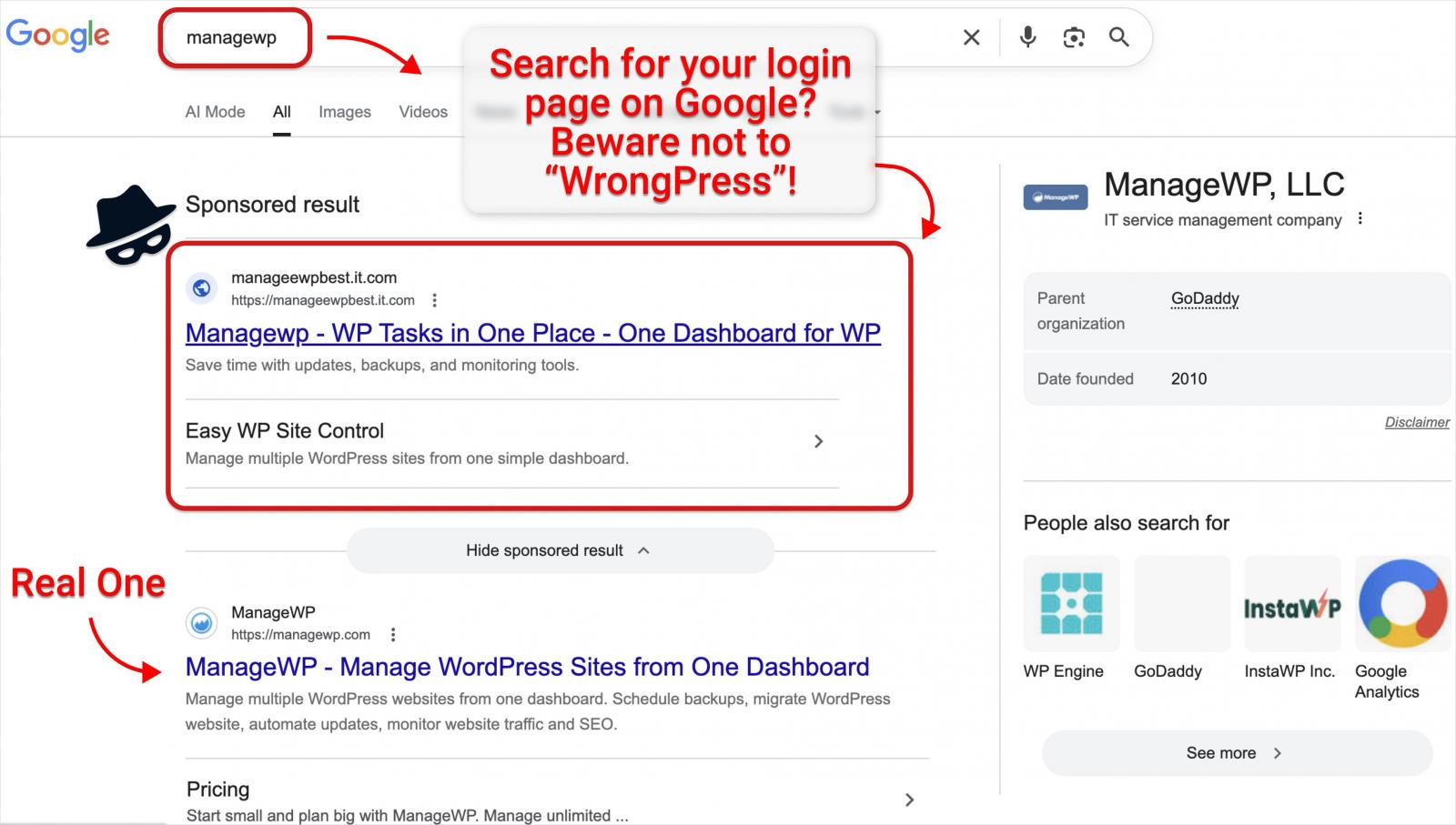
Source: Guardio Labs
Users clicking on the malicious result are taken to a login page that looks identical to the real one. However, any credentials typed in are delivered to a Telegram channel controlled by the attacker.
Unlike the more common phishing pages that capture username and password pairs, the campaign uses a live AiTM setup, as the attacker uses the credentials to log into the platform in real-time.
The victim is then served a fake prompt to enter the two-factor authentication (2FA) code, which the threat actor uses to gain access to the ManageWP account.
Guardio Labs head researcher Nati Tal told BleepingComputer that each ManageWP account typically hosts hundreds of sites.
According to WordPress.org stats, ManageWP’s plugin, which gives the platform control over registered sites, is active on more than 1 million websites.
Guardio Labs was able to infiltrate the attacker’s command-and-control (C2) infrastructure and observed a dropdown command system that enables an interactive and operator-driven phishing flow.
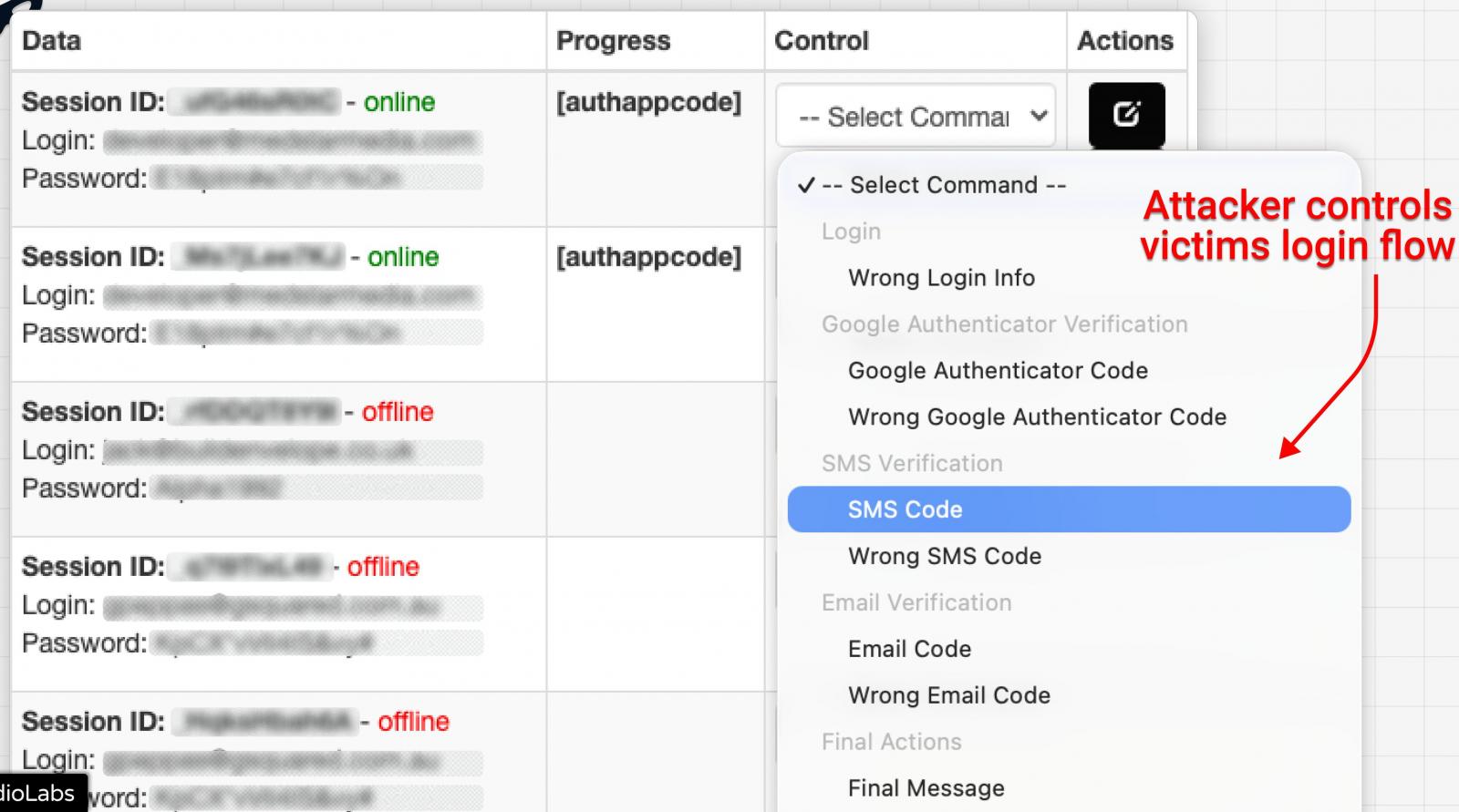
Source: Guardio Labs
Tal also said that the platform does not seem to be part of a commodity kit but rather a private phishing framework.
Interestingly, the researcher found embedded in the code a Russian-language agreement, in which the author denounces responsibility for illegal activity, includes an educational/research use disclaimer, and prohibits public leaks of panel files or use against Russia-based systems.
Guardio Labs has captured victim data from the attackers and started to contact victims to alert them about the exposure. The researchers have confirmed 200 unique victims at the time of writing.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls hold, and closes the remediation loop.

