
Threat actors across underground forums and chat groups are increasingly crafting structured fraud methods aimed at exploiting weaknesses in work processes of financial institutions. Rather than isolated or opportunistic scams, these discussions reflect an organized, process-driven approach that combines stolen identity data, social engineering, and knowledge of financial workflows.
Within these conversations, smaller institutions, particularly small-sized to mid-sized credit unions, are often referenced as more attractive targets due to perceived gaps in verification systems and limited fraud prevention resources.
Flare researchers recently identified a detailed loan fraud method circulating within one such underground group, outlining how attackers can move through credit checks, identity verification, and loan approval processes using stolen identities while avoiding traditional security triggers.
The approach does not rely on exploiting software vulnerabilities, but instead focuses on navigating legitimate onboarding and lending workflows as if the applicant were genuine.
The structure of the post reflects a methodical approach, breaking down the process from identity use to loan approval in a way that can be consistently replicated, pointing to a more organized use of fraud techniques.
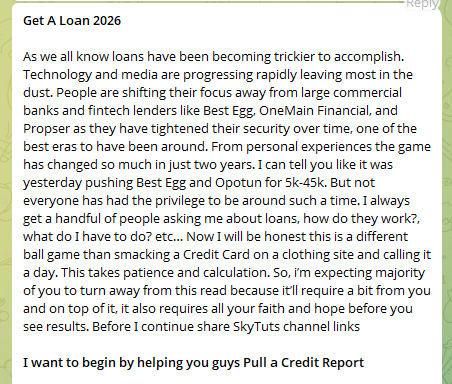
showing the threat actor’s opening
A Process Built on Identity, Not Intrusion
At its core, this approach relies on obtaining sufficient personal data to convincingly impersonate a legitimate borrower. This includes identifiers such as names, addresses, dates of birth, and in some cases, credit-related details.
The process is all digitized, and the attacker is using false identity to submit for a loan. This distinction is critical: the attack does not “break the system,” but he exploits the flaws in its design.
A central component of the method is the ability to pass identity verification checks, particularly those based on knowledge-based authentication (KBA). These systems typically rely on questions derived from:
In practice, much of this information can be reconstructed or inferred from: publicly available data, social media profiles, previously leaked datasets, and aggregated identity records.
This method highlights how attackers can anticipate and prepare for these checks in advance, effectively turning verification into a predictable step rather than a true barrier.
It demonstrates how what was once considered a strong identity control can quickly be learned, adapted to, and ultimately exploited by cybercriminals, who evolve their identity theft tools specifically to collect and bypass these requirements.
By the time a fraudulent application hits your queue, the hard work is already done. Attackers source stolen identities, KBA answers, and financial histories from dark web forums and underground markets—long before they ever contact your institution.
Flare monitors thousands of these sources continuously, so you can detect exposed data at the source, not after the damage is done.
The Fraud Workflow – step by step
-
Identity Acquisition
Stolen personal data is obtained, including full identity details and background information sufficient to impersonate a legitimate individual. -
Credit Profile Assessment
The attacker reviews the victim’s financial profile to determine loan eligibility and likelihood of approval. -
Verification Preparation (KBA Readiness)
Additional personal details are gathered to anticipate and correctly answer identity verification questions. -
Target Selection
Small- to mid-sized credit unions are selected based on perceived weaker verification processes and lower fraud detection maturity. -
Loan Application Submission
A loan application is submitted using the stolen identity, ensuring consistency across all provided data. -
Identity Verification Passed
KBA and standard checks are successfully completed, establishing legitimacy. -
Loan Approval and Fund Release
The institution approves the loan and releases funds through standard channels. -
Fund Movement and Cash-Out
Funds are transferred to controlled accounts, moved through intermediaries, and withdrawn or converted to complete monetization.
Why Small/Mid Credit Unions Are More Targeted
One of the more notable aspects of the method is its focus on smaller financial institutions. Rather than targeting large banks or highly secured fintech platforms, the approach explicitly leans toward small-sized to mid-sized credit unions, which are perceived as:
-
More reliant on traditional identity verification methods
-
Less equipped with advanced behavioral fraud detection
-
More likely to prioritize customer accessibility over strict controls
and thus easier to target for fraud
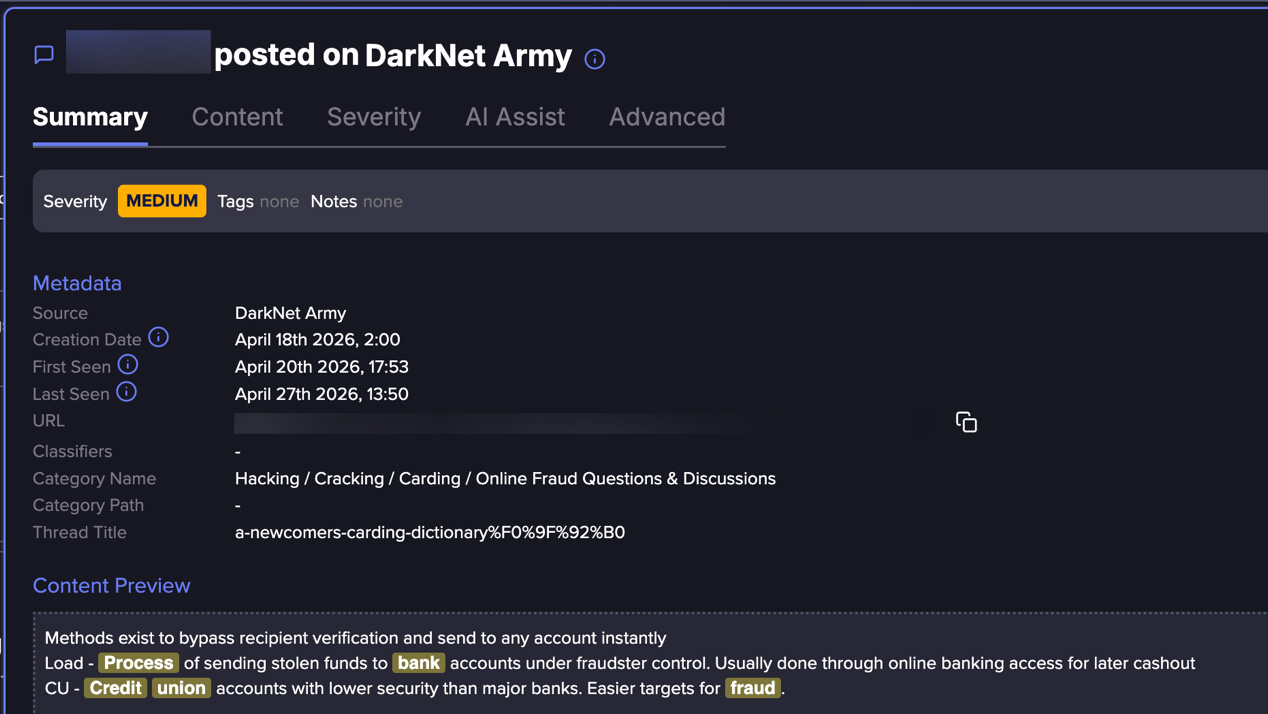
Flare link to post, sign up for the free trial to access if you aren’t already a customer
While not universally true, this perception alone is enough to influence attacker behavior, driving targeting decisions toward institutions believed to offer a higher success rate.
Recent industry reporting supports this trend. In auto lending alone, fraud exposure is projected to reach $9.2 billion in 2025, with smaller and regional lenders facing increasing pressure from organized fraud schemes.
Cash-Out and Monetization
Once a loan is approved, the operation shifts into its most critical phase – turning access into money. At this point, the attacker has already done the hard part: passing identity checks and establishing trust under a stolen identity. From the institution’s perspective, the process appears legitimate, and funds are released through standard channels just as they would be for a real customer.
The focus then moves to speed and separation. Rather than leaving funds in place, they are quickly moved away from the originating account, often through intermediary accounts that create distance from the source.
This stage overlaps with broader fraud ecosystems, where access to additional accounts and financial channels enables funds to be routed, split, or repositioned to reduce traceability.
What makes this phase particularly effective (and difficult to detect) is that each step mirrors normal financial behavior. Transfers, withdrawals, and account activity are not inherently suspicious on their own.
Instead, the risk lies in how these actions are chained together within a compressed timeframe, allowing attackers to complete the cash-out before detection systems or manual reviews can intervene.
Who is Most at Risk?
The method provides indirect insight into which individuals and institutions are most frequently targeted for identity theft.
-
Individuals with Established Credit Histories – Attackers benefit from targeting individuals with strong or stable credit profiles, increasing the likelihood of loan approval.
-
Digitally Exposed Individuals – Those with a significant online presence may inadvertently expose personal details that can assist in passing verification checks.
-
Customers of Smaller Financial Institutions – Users of small-sized to mid-sized credit unions may face increased exposure if their institutions rely on less advanced fraud detection systems.
This loan scam method offers a clear example of how financial fraud is evolving. Instead of targeting systems directly, attackers are increasingly targeting the processes that surround them, leveraging identity, predictability, and trust to achieve their goals.
As these approaches become more structured and accessible, the line between legitimate activity and fraud continues to blur, making detection more complex and requiring a more adaptive defensive approach.
Learn more by signing up for our free trial.
Sponsored and written by Flare.
