
Cybersecurity researchers have uncovered a large-scale fraud operation that uses Telegram’s Mini App feature to run crypto scams, impersonate well-known brands, and distribute Android malware.
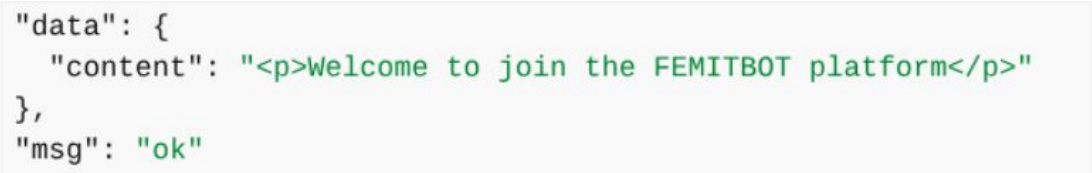
A new report by CTM360 says the platform, dubbed FEMITBOT, is based on a string found in API responses and uses Telegram bots and embedded Mini Apps to create convincing, app-like experiences directly within the messaging platform.
Telegram Mini Apps are lightweight web applications that run inside Telegram’s built-in browser, enabling services such as payments, account access, and interactive tools without requiring users to leave the app.
Abusing Telegram mini apps
According to a CTM360 report shared with BleepingComputer, the FEMITBOT platform is used to conduct multiple types of scams, including fake cryptocurrency platforms, financial services, AI tools, and streaming sites.
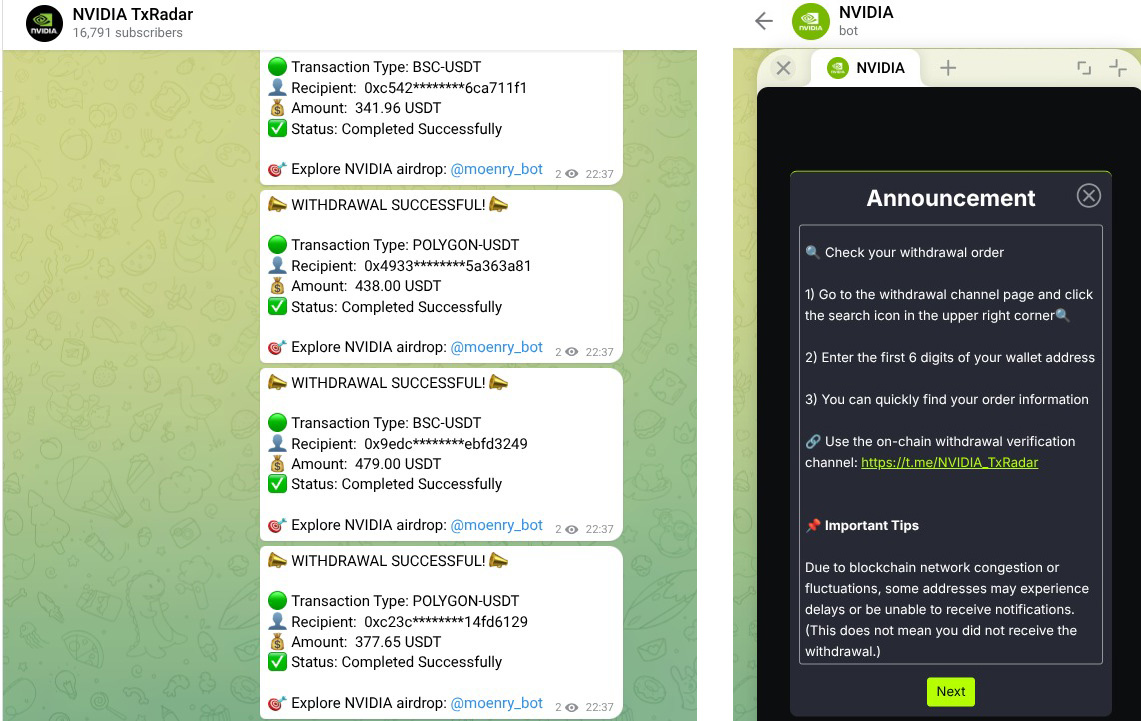
In various campaigns, threat actors impersonated widely recognized brands to increase credibility and engagement, while using the same backend infrastructure with different domains and Telegram bots.
Some of the brands impersonated in this campaign include Apple, Coca-Cola, Disney, eBay, IBM, Moon Pay, NVIDIA, YouKu,
Source: CTM360
Researchers say the activity uses a shared backend, where multiple phishing domains use the same API response, “Welcome to join the FEMITBOT platform,” indicating they are all using the same infrastructure.
Source: CTM360
The operation uses Telegram bots to display phishing sites directly within the social media platform. When a user interacts with a bot and clicks “Start,” the bot launches a Mini App that displays a phishing page in Telegram’s built-in WebView, making it appear as part of the app itself.
Once inside, victims are shown dashboards with fake balances or “earnings,” often paired with countdown timers or limited-time offers to create a sense of urgency.
When users attempt to withdraw funds, they are prompted to make a deposit or complete referral tasks, a common tactic in investment and advance-fee scams.
The researchers say the infrastructure is designed to be used across different campaigns, allowing attackers to easily switch branding, languages, and themes.
The campaigns also use tracking scripts, such as Meta and TikTok tracking pixels, to track users’ activity, measure conversions, and likely to optimize performance.
Some Mini Apps also attempted to distribute malware in the form of Android APKs that impersonated brands like the BBC, NVIDIA, CineTV, Coreweave, and Claro.

Source: CTM360
Users are prompted to download Android APK files, open links within the in-app browser, or install progressive web apps that mimic legitimate software.
“The APK filenames are carefully chosen to resemble legitimate applications or use random-looking names that don’t immediately trigger suspicion,” explains CTM360.
“The APKs are hosted on the same domain as the API, ensuring TLS certificate validity and avoiding mixed-content warnings in the browser.”
Users should be cautious when interacting with Telegram bots that promote crypto investments or prompt them to launch Mini Apps, especially if they are asked to deposit funds or download apps.
As a general rule, Android users should avoid sideloading APK files, which are commonly used to distribute malware outside the Google Play Store.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls hold, and closes the remediation loop.

