- go-exploit, VulnCheck’s open-source exploit framework, now includes a new C2 feature called ShellTunnel.
- ShellTunnel captures reverse shell traffic and routes it through an intermediary attacker-controlled server before reaching the main command-and-control (C2) server.
- This setup ensures that the victim device never directly connects to the C2, which can be beneficial in bypassing network egress restrictions.
- ShellTunnel is fully compatible with older exploits and requires minimal modification to implement.
go-exploit is a Go-based exploit framework built and maintained by VulnCheck’s Initial Access Intelligence team. The design uniquely supports a range of flexible C2 configurations. The latest feature to hit go-exploit is ShellTunnel, a new C2 that adds flexibility and operational security by capturing and forwarding reverse shell traffic from an intermediary server before sending it on to the primary C2 server.
What makes ShellTunnel especially appealing is its simplicity and ease of integration. The C2 effectively acts as a proxy shell, allowing teams to redirect traffic through a middle server instead of a direct connection. This is valuable for a variety of operational reasons, including network egress rules that can limit direct connections to external servers.
The ShellTunnel setup is straightforward yet powerful. Here’s how it operates:
- Exploitation: The attacker initiates an attack from an intermediary system using go-exploit. A good example would be an attacker that has compromised a firewall, and is attempting to pivot inwards. The intermediary is the firewall.
- Reverse Shell Capture: The compromised system sends the reverse shell back to the attacker’s server (intermediary server or firewall in the above example), where go-exploit is running.
- Data Forwarding to C2: go-exploit’s ShellTunnel then forwards this reverse shell traffic to the main C2 server, creating a separation between the compromised device and the C2.
This separation means that the target device only connects to the attacker’s intermediary server, never to the main C2, which may help avoid detection and reduce certain types of network logging.
To showcase ShellTunnel, we used an example based on our previously open sourced go-exploit for CVE-2023-22527, affecting Confluence servers (see our previous writeup, Does Confluence Dream of Shells?). We updated the exploit to incorporate the new ShellTunnel feature. This required only a minor version bump and specifying ShellTunnel in the C2 list within the go-exploit configuration.
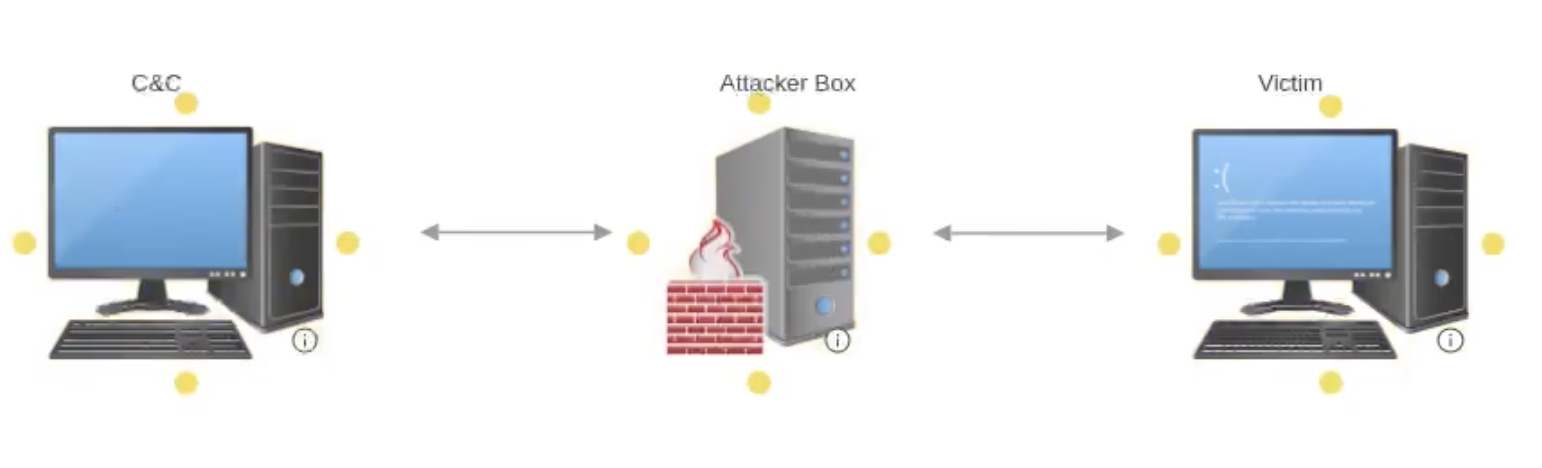
To better illustrate, we deployed ShellTunnel in a lab environment using three key components:
- Victim Machine: A Windows machine running Confluence, serving as the target of exploitation.
- Attacker Server: This intermediary server captures the reverse shell before forwarding it to the C2.
- Command and Control Server (C2): The final destination for the reverse shell traffic, providing centralized control over the compromised device.
Using this setup, we initiated the attack from the attacker server. After capturing the reverse shell, we forwarded it to the C2 using SSL encryption, enabling us to monitor the traffic with Wireshark for verification. This setup allowed us to observe the traffic flow between each component, with unencrypted traffic between the victim and attacker, and SSL-encrypted traffic from the attacker to the C2.
ShellTunnel’s separation of attacker and C2 connections offers several advantages for exploitation efforts:
- Network Evasion: Network rules designed to prevent direct outbound connections may be bypassed, as the victim only needs to connect to the attacker server.
- Enhanced Operational Security: Because the target device does not connect directly to the C2, it reduces exposure to network scans and detection tools that monitor external connections.
- Ease of Implementation: ShellTunnel’s configuration in go-exploit requires minimal changes, making it compatible with existing exploits without extensive modification.
The ShellTunnel update is part of go-exploit’s open-source package, available on GitHub. Once set up, adding ShellTunnel to an exploit requires only a few tweaks to the C2 list within go-exploit, making it accessible for various operational scenarios with minimal setup.
We welcome contributions to go-exploit from the community, so if this feature inspires you to build out new C2 methods or you’d like to see specific functionalities in future releases, feel free to submit a pull request.
ShellTunnel brings a new level of flexibility to go-exploit’s C2 capabilities, adding valuable proxying functionality with easy configuration. By separating the attacker from the C2, it provides an added layer of evasion and operational security, making it a promising addition for scenarios where avoiding direct C2 connections is critical.
The VulnCheck Initial Access team is always looking to advance the state of attack on initial access vulnerabilities. For more research and updates like this, see our blogs, Exploring ABB Vulnerabilities, PaperCut Exploitation and Fileless Remote Code Execution on Juniper Firewalls
. Sign up to start a trial of our Initial Access Intelligence and Exploit & Vulnerability Intelligence product today.