A new vulnerability dubbed Pack2TheRoot could be exploited in the PackageKit daemon to allow local Linux users to install or remove system packages and gain root permissions.
The flaw is identified as CVE-2026-41651 and received a high-severity rating of 8.8 out of 10. It has persisted for almost 12 years in the PackageKit daemon, a background service that manages software installation, updates, and removal across Linux systems.
Earlier this week, some information about the vulnerability has been published, along with PackageKit version 1.3.5 that addresses the issue. However, technical details and a demo exploit have been not been disclosed to allow the patches to propagate.
An investigation from the Deutsche Telekom Red Team uncovered that the cause of the bug is the mechanism PackageKit uses to handle package management requests.
Specifically, the researchers found that commands like ‘pkcon install’ could execute without requiring authentication under certain conditions on a Fedora system, allowing them to install a system package.
Using the Claude Opus AI tool, they further explored the potential for exploiting this behavior and discovered CVE-2026-41651.
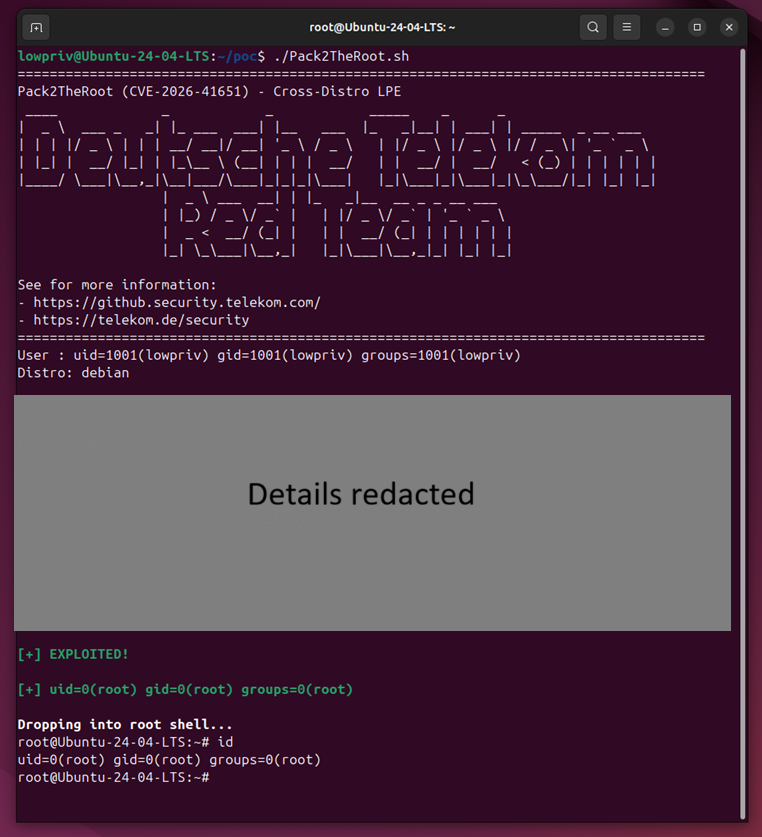
Source: Deutsche Telekom
Impact and fixes
Deutsche Telekom’s Red Team reported their findings to Red Hat and PackageKit maintainers on April 8. They state that it’s safe to assume that all distributions that come with PackageKit pre-installed and enabled out-of-the-box are vulnerable to CVE-2026-41651.
The vulnerability has been present in PackageKit version 1.0.2, released in November 2014, and affects all versions through 1.3.4, according to the project’s security advisory.
Researchers’ testing have confirmed that an attacker could exploit the the CVE-2026-41651 vulnerability in the following Linux distributions:
- Ubuntu Desktop 18.04 (EOL), 24.04.4 (LTS), 26.04 (LTS beta)
- Ubuntu Server 22.04 – 24.04 (LTS)
- Debian Desktop Trixie 13.4
- RockyLinux Desktop 10.1
- Fedora 43 Desktop
- Fedora 43 Server
The list is not exhaustive, though, and any Linux distribution using PackageKit should be treated as potentially vulnerable to attacks.
Users should upgrade to PackageKit version 1.3.5 as soon as possible, and ensure that any other software using the package as a dependency has been moved to a safe release.
Users can use the commands below to check if they have a vulnerable version of the PackageKit installed and if the daemon is running:
dpkg -l | grep -i packagekit
rpm -qa | grep -i packagekit
Users can run systemctl status packagekit or pkmon to check if the PackageKit daemon is available and running, which indicates that the system may be at risk if left unpatched.
Although no details about the state of exploitation have been shared, the researchers noted that there are strong signs showing compromise because exploitation leads to the PackageKit daemon hitting an assertion failure and crashing.
Even if systemd recovers the daemon, the crash is observable in the system logs.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls hold, and closes the remediation loop.