👋 Welcome to the 103rd issue of The OSINT Newsletter. This issue contains OSINT news, community posts, tactics, techniques, and tools to help you become a better investigator. Here’s an overview of what’s in this issue:
-
What the Dark Web is
-
The difference between surface, deep and dark web
-
The kinds of data you’ll find
-
OSINT vs. DARKINT
-
…and why Dark Web users are like onions.
🪃 If you missed the last newsletter, here’s a link to catch up.
⚡ OSINT Methods for Archiving and Searching Video by Keyword
🎙️ If you prefer to listen, here’s a link to the podcast instead.
Let’s get started. ⬇️
While OSINT operates out in the open – it is open source intelligence, after all – some of the most significant data lurks in the dark corners of the internet. So this time, we’re getting shady with it. Dark Web intelligence (or DARKINT) is the hidden side of OSINT. It sounds dangerous; but it’s perfectly safe to step into the gloom if you know how. Let’s begin our two-issue trip into the shadows with an overview of Dark Web OSINT. In Part One, we’ll cover:
-
What the Dark Web is
-
The difference between surface, deep and dark web
-
The kinds of data you’ll find
-
OSINT vs. DARKINT
-
…and why Dark Web users are like onions.
Let’s go dark.
The internet looks a little like an iceberg. It’s divided into multiple layers: the surface web at the top, the dark web at the bottom, and the deep web in the middle.
-
Surface Web: The normie ”internet”. The stuff you use every day, that is indexed by conventional search engines (Google, Bing etc.), and easily searchable.
-
Deep Web: Also known as the “invisible web” or “hidden web’. Unindexed and not easily searchable, but still accessible without a specialised browser. Content on the deep web includes online banking services, private networks and corporate systems. It makes up around 90% of the internet.
-
Dark Web: Unindexed, encrypted, and only accessible with specialised tools like onion browsers. The Dark Web makes up somewhere between 1% and 6% of the internet; and unlike its deep cousin, it’s always anonymised. Data found on this layer is known as dark web intelligence (DARKINT).
The important thing to remember about the Dark Web is that it’s not a single place; it’s a collection of anonymous websites hosted on encrypted networks. Some of these networks play host to financial fraudsters, terrorist cells, CSAM, drug dealing and weapons sales.
But – despite the scare stories – not everything on the dark web is dodgy. Although many criminals do ply their wares on the internet’s dark side, it also has legitimate privacy-driven and anti-censorship use cases. For example, even major news outlets mirror their sites on the Dark Web, to give citizens secret access under harsh state censorship.
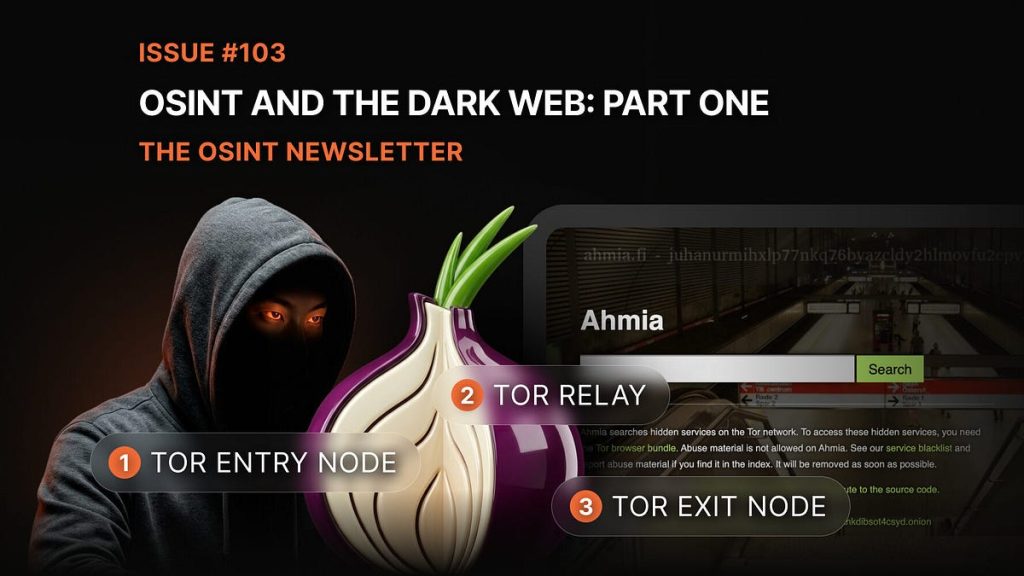
To access the Dark Web, you’ll need special tools. Enter TOR: short for The Onion Router. Onion browsers like TOR are too complicated to explain in detail here; but they basically work by encrypting your connections through multiple layers – like the skin of an onion. Each layer only knows part of the journey, making it extremely difficult to trace your activities. What makes the Dark Web a-peel-ing (sorry) to its users is anonymity; and onion browsers have this built-in.
Meanwhile, websites on the Dark Web use .onion domains, too, meaning both the user and the host are completely obscured. These sites are officially called ‘hidden services’ – and without them, there’s no Dark Web.
Hosted within the TOR network, hidden services work similarly; both user and host build encrypted connections instead of linking up directly. Each hidden service will send out a descriptor on the TOR network, that’s discoverable to all users that know the .onion address. When users gain access to the site, they actually go to this rendezvous point – so neither side knows each other’s real IP. This process means mutual anonymity for everybody involved.
So in Shrek terms, Dark Web users are the ogres of the internet. They’ve got layers.
From an OSINT perspective, the most important part of the Dark Web will always be the data we meet along the way. But what data types can you expect to find on the shadowy side of the net? Here’s what’s usually lurking down there.
One of the most valuable (and most common) forms of DARKINT is the good old breach dump. Compromised data – leaked logins, for example – proliferates all over the Dark Web. You can find:
The boon with breach dumps is they often “package” multiple data points together; terrible for the subjects’ anonymity, but perfect for OSINT pros piecing together an identity profile. These datasets can even be traded, reused or repackaged across multiple Dark Web platforms. However, it’s important to bear in mind the compliance problem when handling potentially dirty data.
Remember the fraud, drugs and guns we discussed earlier? Those Dark Web forums and marketplaces are central to the hidden net’s ecosystem; although they’re dangerous and damaging for the offline world, they allow OSINT investigators to catch bad guys in the act. Cybercriminal activity can include:
-
Discussion of terrorist activities
-
Organising financial fraud
-
Buying and selling personal data
-
“Service” marketplaces (drugs, guns, porn etc)
Even though the Dark Web is anonymised, it can still provide data that unmasks serious criminals. Many investigations have been cracked with DARKINT – exposing heinous offenders including child sexual abusers.
Paste sites – like Pastebin – are social media platforms that allow their users to dump large quantities of plain-text data online. They were created as innocent spaces for coders to share snippets of work, but have become increasingly popular with threat actors as a staging ground for dangerous activity.
These are often used to share sensitive information from stolen credit card details, to malware, to exploit code. Although they aren’t often persistent, they can still be full of data that gets widely distributed – data that can also be crucial for OSINT.
All DARKINT is OSINT, but not all OSINT is DARKINT. OSINT includes the publicly accessible, indexed or easily reachable by the normie-net data. Meanwhile, DARKINT is just the hidden, encrypted data that only specialised Dark Web tools can dig up.
The question remains, however: why risk digging into DARKINT at all? Surely – unless you’re fighting cybercrime – the Dark Web is more risk than reward? Well, whilst OSINT tells you what’s going on out in public, DARKINT exposes what netizens intentionally work to hide. In practice, most investigators will combine OSINT and DARKINT to find all the data they need.
So, now you’ve taken your first steps into the shadowy side of the internet known as the Dark Web. You should now know:
-
The Internet is like an iceberg – 90% is below the surface
-
The Dark Web isn’t all dodgy; it does have legitimate uses
-
All DARKINT is OSINT, but not all OSINT is DARKINT
-
… and DARKINT investigators are like onions – they have layers.
See you next issue, investigators!
⭐ Sponsor: SockPuppet.io
SockPuppet delivers secure, isolated environments with persistent virtual desktops and phones, real carrier-based SMS for OTPs, and residential IP connectivity—selectable from hundreds of locations. All accessible through a simple web interface that scales as your investigations grow.
Visit SockPuppet.io to empower your investigations with technology trusted by intelligence professionals.
🏁 New CTF Challenge Live – Crowd Control
A new CTF challenge has been posted on our CTF website. This week’s challenge involves estimating the number of people in a photograph from the 2024 NATO Summit using a specific tool.
Start competing in our Capture the Flag (CTF)
🪃 If you missed the last CTF, here’s a link to catch up.
Last week’s CTF challenge featured a challenge titled “Digital Footprints” where participants needed to identify the domains linked to a specific email address using only OSINT techniques.
✅ That’s it for the free version of The OSINT Newsletter. Consider upgrading to a paid subscription to support this publication and independent research.
By upgrading to paid, you’ll get access to the following:
👀 All paid posts in the archive. Go back and see what you’ve missed!
🚀 If you don’t have a paid subscription already, don’t worry. There’s a 7-day free trial. If you like what you’re reading, upgrade your subscription. If you can’t, I totally understand. Be on the lookout for promotions throughout the year.
🚨 The OSINT Newsletter offers a free premium subscription to all members of law enforcement. To upgrade your subscription, please reach out to LEA@osint.news from your official law enforcement email address.