
A newly identified malicious implant named RoadK1ll is enabling threat actors to quietly move from a compromised host to other systems on the network.
The malware is a Node.js implant that communicates over a custom WebSocket protocol to sustain ongoing attacker access and enable further operations.
RoadK1ll was discovered by managed detection and response (MDR) provider Blackpoint during an incident response engagement.
The researchers describe it as a lightweight reverse tunneling implant that blends into normal network activity and turns an infected machine into a relay point for the attacker.
“Its sole function is to convert a single compromised machine into a controllable relay point, an access amplifier, through which an operator can pivot to internal systems, services, and network segments that would otherwise be unreachable from outside the perimeter,” Blackpoint says.
RoadK1ll does not rely on an inbound listener on the compromised host. It establishes an outbound WebSocket connection to attacker-controlled infrastructure, which is then used as a tunnel to relay TCP traffic on demand.
This approach allows the attacker to remain undetected for a longer period and forward traffic to internal systems through a single WebSocket tunnel.
“The attacker can instruct RoadK1ll to open connections to internal services, management interfaces, or other hosts that are not directly exposed externally,” Blackpoint says.
“Because these connections originate from the compromised machine, they inherit its network trust and positioning, effectively bypassing perimeter controls.”
Furthermore, RoadK1ll supports multiple concurrent connections over the same tunnel, allowing its operator to communicate with several destinations at once.
According to the researchers, the malware supports a small set of commands, which include:
- CONNECT – Instructs the implant to open a TCP connection to a specified host and port
- DATA – Forwards raw traffic through an active connection
- CONNECTED – Confirms that a requested connection was successfully established
- CLOSE – Terminates an active connection
- ERROR – Returns failure information to the operator
The CONNECT command triggers RoadK1ll’s primary function: initiating an outbound TCP connection to an adjacent target, extending the attacker’s reach into the compromised network.
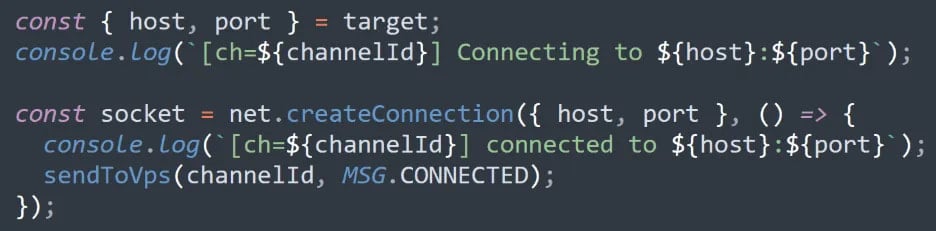
Source: Blackpoint
If the channel is interrupted, the tool attempts to restore the WebSocket tunnel using a re-connection mechanism, allowing the attackers to maintain persistent access without generating noise through manual intervention.
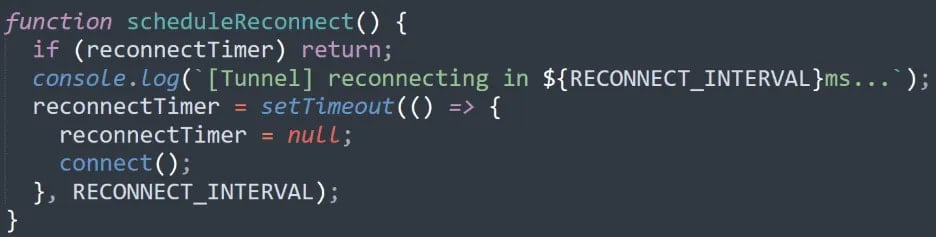
Source: Blackpoint
However, Blackpoint notes that RoadK1ll lacks a traditional persistence mechanism that uses registry keys, scheduled tasks, or services. Instead, it operates only as long as its process remains alive.
Despite this, the researchers say that the malware “shows a more modern and purpose-built implementation” of covert communication that makes it flexible, efficient, and easy to deploy.
It also allows the threat actor to move to internal systems and segments of the environment that are not reachable from outside the network.
Blackpoint provides a small set of host-based indicators of compromise that includes a hash for RoadK1ll and an IP address used by the threat actor for communication with the implant.

