
Palo Alto Networks warned customers today that a critical-severity unpatched vulnerability in the PAN-OS User-ID Authentication Portal is being exploited in attacks.
Also known as the Captive Portal, the User-ID Authentication Portal is a PAN-OS security feature that authenticates users whose identities cannot be automatically mapped by the firewall.
Tracked as CVE-2026-0300, this zero-day bug stems from a buffer overflow weakness that allows unauthenticated attackers to execute arbitrary code with root privileges on Internet-exposed PA-Series and VM-Series firewalls via specially crafted packets.
“Limited exploitation has been observed targeting Palo Alto Networks User-ID™ Authentication Portals that are exposed to untrusted IP addresses and/or the public internet,” Palo Alto Networks said in a Wednesday advisory.
“Customers following standard security best practices, such as restricting sensitive portals to trusted internal networks are at a greatly reduced risk.”
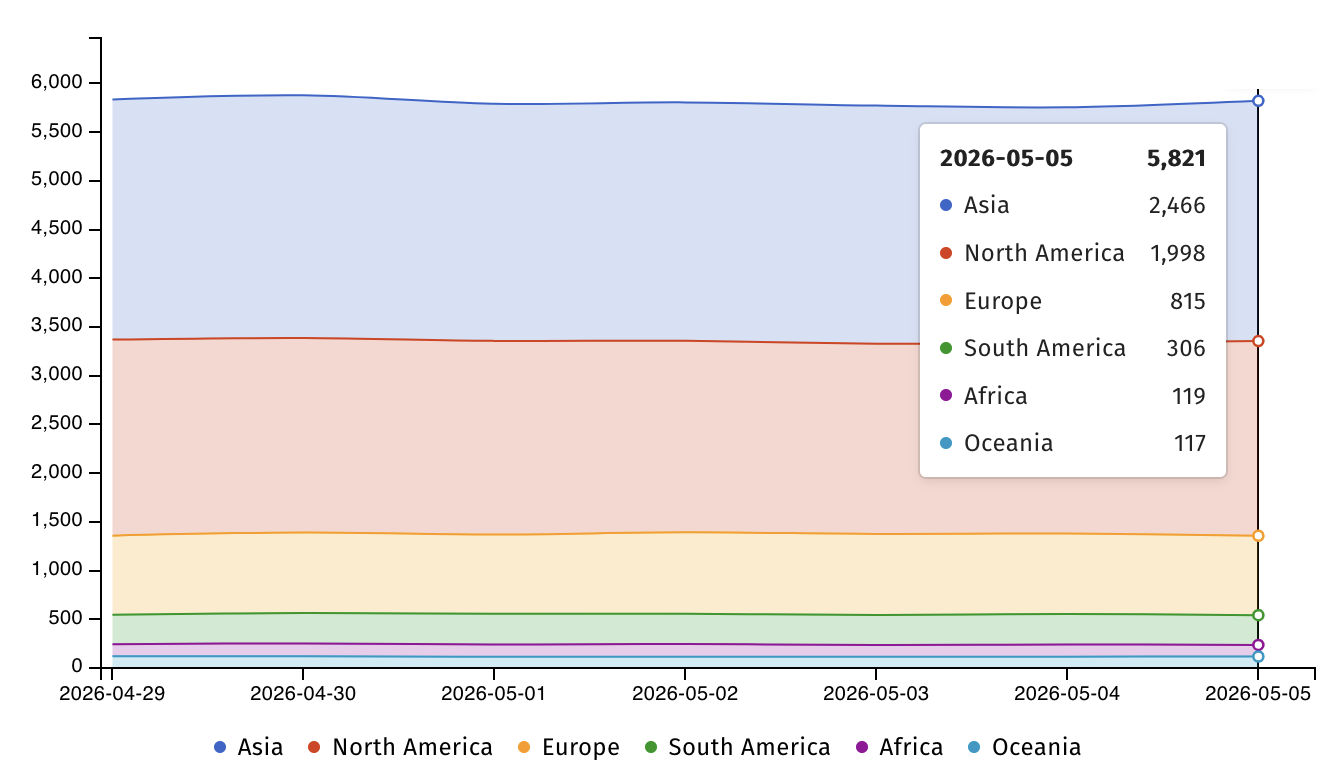
At the moment, Internet threat watchdog Shadowserver is tracking over 5,800 PAN-OS VM-series firewalls exposed online, most of them in Asia (2,466) and North America (1,998).
The company has also flagged the vulnerability as the highest possible severity and says that admins can quickly check whether their firewalls are configured to use the vulnerable service from the User-ID Authentication Portal Settings page, found under Device > User Identification > Authentication Portal Settings -> Enable Authentication Portal.
Palo Alto Networks is still working to address the zero-day, and until a patch is available, it “strongly” recommends that customers secure the User-ID Authentication Portal by restricting access to trusted zones only or disabling the portal if that’s not possible.
PAN-OS firewalls have frequently been targeted in attacks, often exploiting zero-day security vulnerabilities. For instance, in November 2024, Shadowserver revealed that thousands of firewalls had been compromised (even though the company said the attacks impacted only “a very small number”) in attacks that chained two PAN-OS firewall zero-days.
One month later, Palo Alto Networks warned that hackers were exploiting another PAN-OS DoS flaw to target PA-Series, VM-Series, and CN-Series firewalls, forcing them to reboot and disable firewall protections. Soon after, in February, attackers switched to abusing three other PAN-OS flaws to compromise Palo Alto Networks firewalls with internet-facing management interfaces.
Palo Alto Networks says its products and services are used by more than 70,000 customers worldwide, including 90% of Fortune 10 companies and most of the largest U.S. banks.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls hold, and closes the remediation loop.

