
The U.S. House Committee on Homeland Security is calling on Instructure executives to testify about two cyberattacks by the ShinyHunters extortion group that targeted the company’s Canvas platform, allowing threat actors to steal student data and disrupt schools during final exams.
In a letter sent Monday afternoon to Instructure CEO Steve Daly, Homeland Security Committee Chairman Andrew R. Garbarino said the committee is investigating the massive breach at Instructure that impacts millions of students.
“The Committee on Homeland Security (Committee) is investigating the concerning reports related to recent cybersecurity incidents affecting Instructure Holdings, Inc. and the tens of millions of students, educators, and administrators who rely on its Canvas learning management platform,” reads the letter.
“Within the span of one week, the cybercriminal group known as ShinyHunters breached Instructure twice.”
As first reported by BleepingComputer, Instructure disclosed on May 3 that it had suffered a breach. The company later confirmed it detected the intrusion on April 29 after threat actors compromised its systems and stole data belonging to students and school staff using Canvas.
The company said the exposed information included names, email addresses, student identification numbers, and messages exchanged between students and teachers on the platform. However, the data did not include passwords, financial information, or government identifiers.
On May 3, the ShinyHunters extortion gang claimed responsibility for the attack, telling BleepingComputer that they stole 280 million data records from 8,809 colleges, school districts, and online education platforms.
The threat actor shared a list of impacted education organizations, with stolen record counts ranging from tens of thousands to several million for each institution.
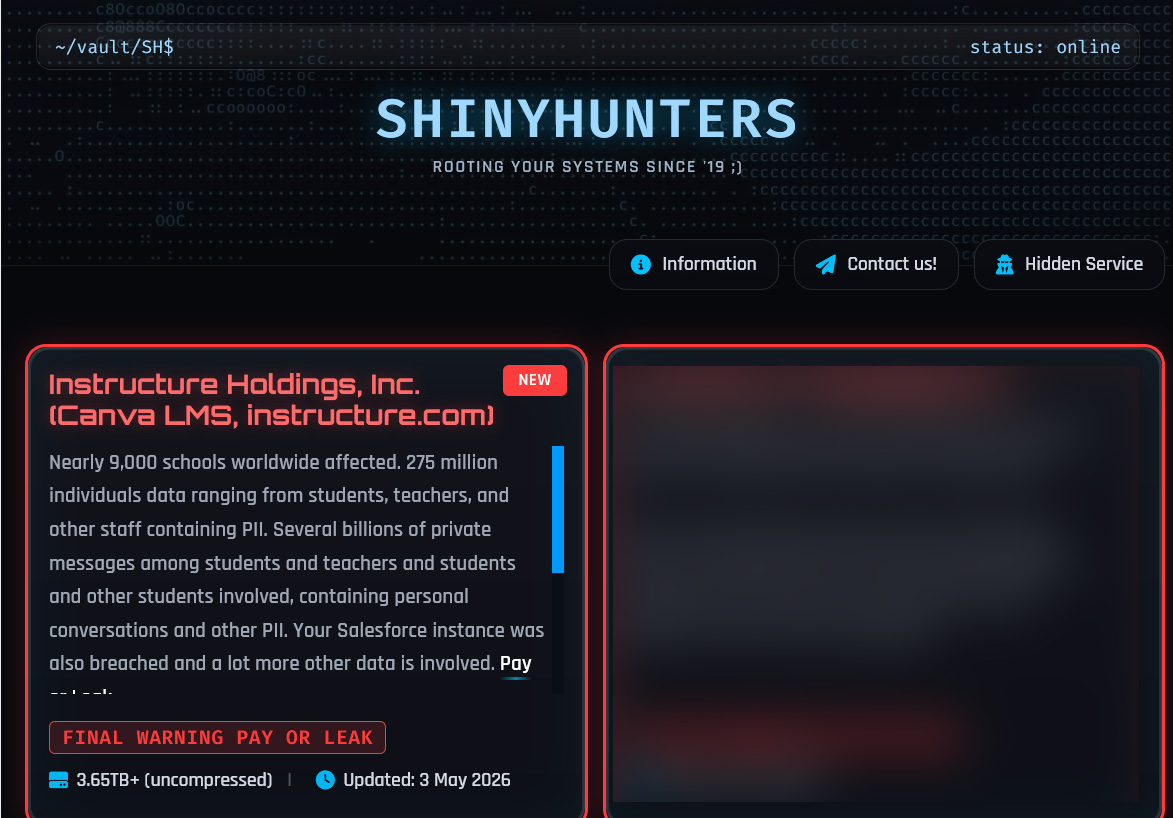
Source: BleepingComputer
The ShinyHunters group conducted a second attack that defaced Canvas login portals at schools and universities across the United States, displaying extortion messages demanding that Instructure negotiate with the group. The disruption affected institutions across multiple states during final exams and end-of-semester activities, with some colleges forced to cancel exams.
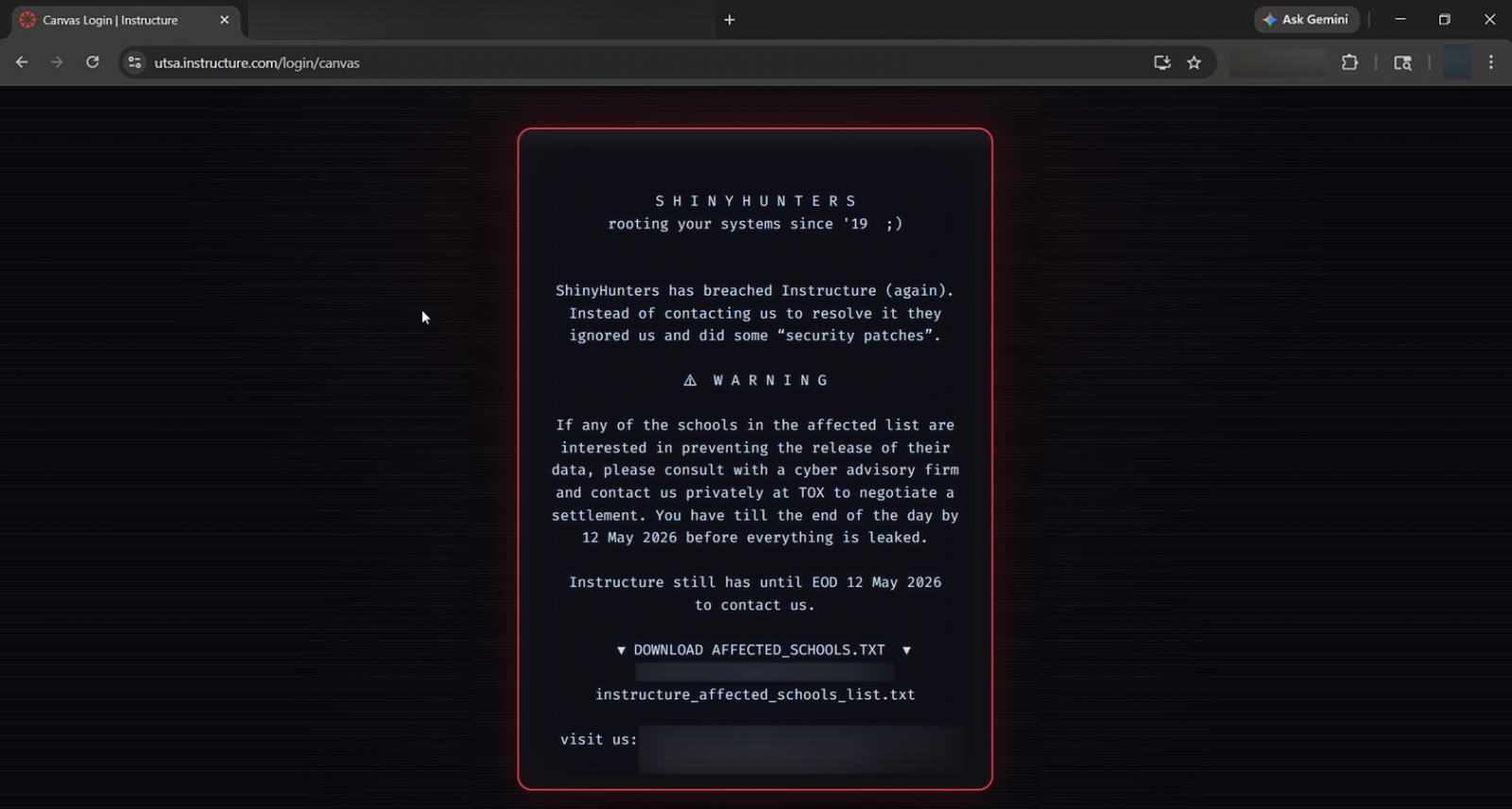
Source: BleepingComputer
BleepingComputer later learned that the threat actors used multiple cross-site scripting (XSS) vulnerabilities to obtain authenticated admin sessions and modify the login portal pages.
According to the Homeland Security Committee letter, schools in California, Florida, Georgia, Oklahoma, Oregon, Nevada, North Carolina, Tennessee, Utah, Virginia, and Wisconsin reported disruptions tied to the incident.
The committee also referred to messages posted by the attackers claiming they targeted Instructure again because the company refused to negotiate with the group.
Last night, soon after ShinyHunters mysteriously removed Instructure from its data leak site, the company disclosed that it had reached an agreement with ShinyHunters to stop the public leak and ensure the stolen data was deleted.
While the company did not outright state that it paid a ransom or directly confirm BleepingComputer’s questions on the matter via email, extortion groups rarely agree to delete stolen data or halt leaks unless some form of payment or agreement has been reached.
The Homeland Security Committee said the repeated compromises raise “serious questions” about the company’s incident response capabilities and its obligations to properly protect the data it stores.
The committee is requesting that Instructure or a senior company representative participate in a briefing no later than May 21 to discuss both intrusions, the stolen data, its containment and notification efforts, and coordination with federal agencies.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls hold, and closes the remediation loop.

