
Education technology giant Instructure has confirmed that a security vulnerability allowed hackers to modify Canvas login portals and leave an extortion message.
BleepingComputer has learned that both the breach and defacements involved multiple cross-site scripting (XSS) vulnerabilities that enabled the attacker to obtain authenticated admin sessions.
The second hack was to draw attention and to pressure Instructure into entering negotiations to pay a ransom following an initial breach disclosed a week before.
Instructure is the developer of Canvas, a popular learning management system (LMS) used by schools and universities around the world to handle assignments and coursework.
On April 29, the company discovered that its network had been breached and “immediately revoked the unauthorized party’s access, started an investigation, and engaged outside forensic experts.”
A few days later, the company confirmed that data was stolen in the cyberattack, and ShinyHunters published Instructure on their data leak site, stating that they stole more than 3.6 terabytes of uncompressed data.
In an attempt to coerce Instructure into paying a ransom, the threat actor hacked Instructure again on May 7 using the same vulnerability used in the initial intrusion.
ShinyHunters injected malicious JavaScript exploiting XSS bugs within user-generated content features, which gave them access to authenticated admin sessions and allowed them to perform privileged actions.
In an email to BleepingComputer on Sunday, Instructure confirmed that the exploited security issue affected the Free-for-Teacher environment, the free, limited version of Canvas LMS for individual educators.
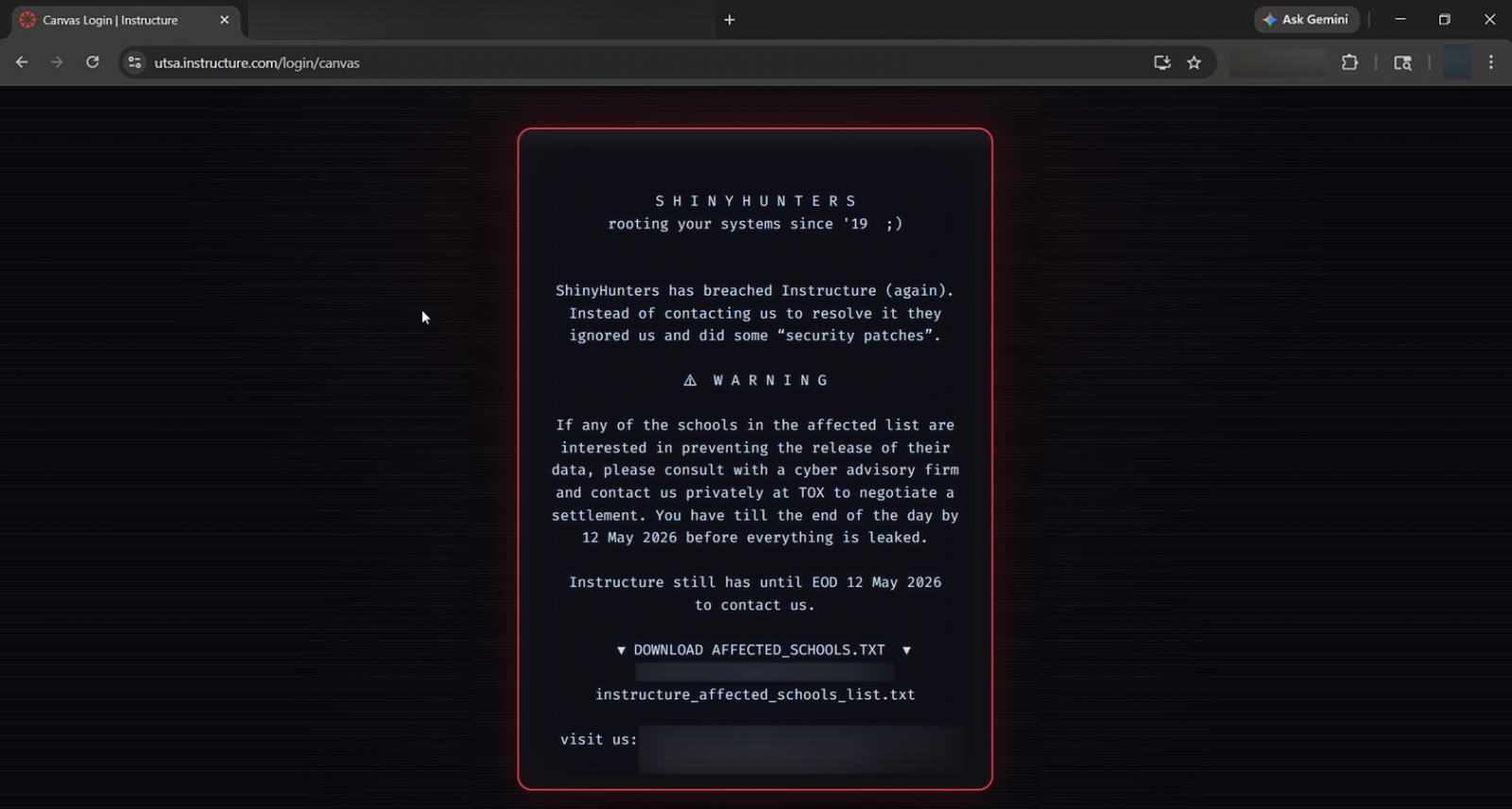
“The unauthorized actor made changes to the pages that appeared when some students and teachers were logged in through Canvas” – Instructure
At the time, the organization added that it temporarily took Canvas offline to prevent the malicious activity from spreading, determine the cause, and to “apply additional safeguards.”
ShinyHunters used the flaw to add a message to Canvas login portals, warning that the company, as well as schools using its platform, had until May 12 to reach out and negotiate a ransom.
Instructure has shut down Free-For-Teacher accounts until the issues have been resolved. However, Canvas has been restored and is available for use since May 9th.
While no data was compromised when defacing Canvas login portals, the data that ShinyHunters exfiltrated in the first breach likely includes usernames, email addresses, course names, enrollment information, and messages.
According to ShinyHunters, the Instructure breach impacts 8,809 educational organizations (schools, universities, colleges, online platforms) and the hackers claim to have stolen 275 million records belonging to students, teachers, and other staff members.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls hold, and closes the remediation loop.

