
The Amazon Simple Email Service (SES) is being increasingly abused to send convincing phishing emails that can bypass standard security filters and render reputation-based blocks ineffective.
Although the resource has been leveraged for malicious activity in the past, the current spike may be due to a large number of AWS Identity and Access Management access keys exposed in public assets.
Because it is a legitimate, trusted resource, phishing operations can leverage Amazon SES to send out malicious emails that pass authentication checks.
Kaspersky researchers note in a report today that they’ve “observed an uptick in phishing attacks leveraging Amazon SES” to deliver links that redirect to a malicious site.
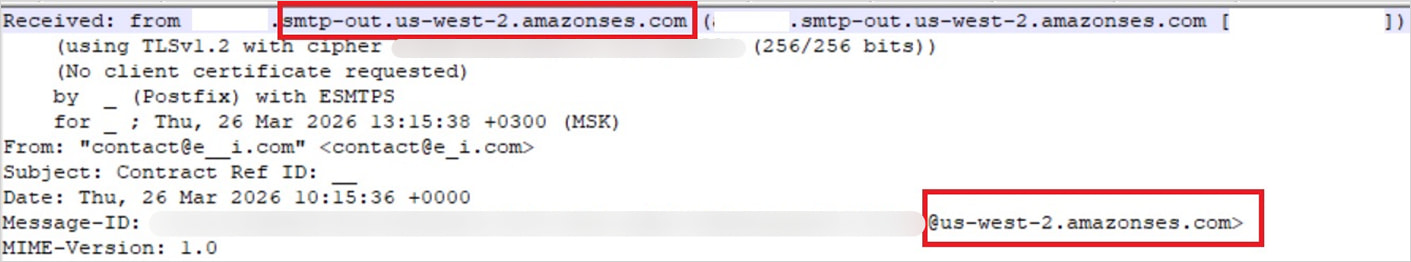
Source: Kaspersky
The researchers believe the main driver of this abuse is the increasing exposure of AWS credentials in GitHub repositories, .ENV files, Docker images, backups, and publicly accessible S3 buckets.
Finding the access keys is typically done in an automated way using bots built on the open-source TruffleHog utility, which is designed to scan for leaked secrets.
Threat actors now rely on automated attacks that streamline secret scanning, permission validation, and email distribution, enabling unprecedented levels of abuse.
“After verifying the key’s permissions and email sending limits, attackers are equipped to spread a massive volume of phishing messages,” Kaspersky explains.
Based on their findings, the researchers say that the phishing quality is high, featuring custom HTML templates that mimic real services and realistic login flows.
The observed attacks include fake document-signing notifications that imitate DocuSign to lead victims to AWS-hosted phishing pages, as well as more advanced business email compromise (BEC) attacks.
Attackers fabricate entire email threads to make the phishing messages appear more convincing and send fake invoices to trick finance departments into making payments.
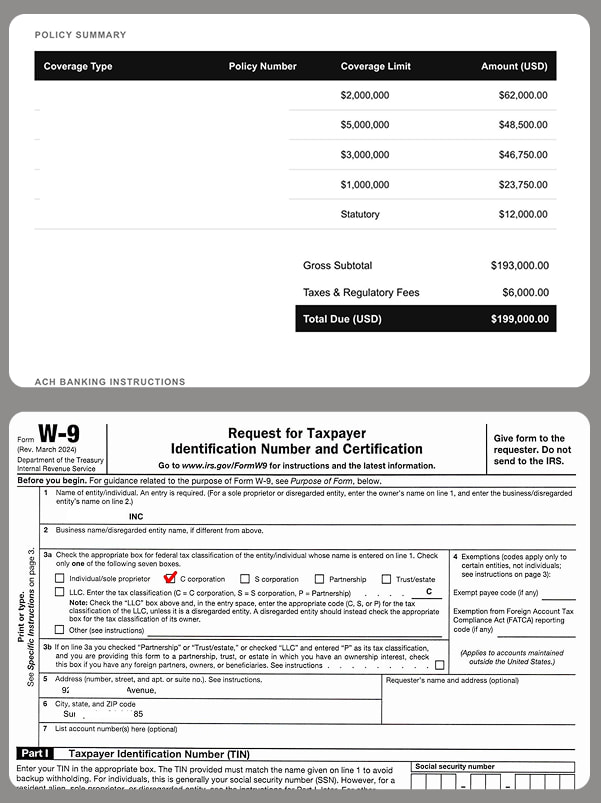
Source: Kaspersky
By leveraging Amazon SES, attackers no longer need to worry about authentication checks such as the SPF, DKIM, and DMARC protocols.
Additionally, blocking the offending IP addresses that deliver the phishing emails is not an acceptable solution because it would prevent all emails coming through Amazon SES.
Kaspersky recommends that companies restrict IAM permissions based on the “least privilege” principles, enable multi-factor authentication, regularly rotate keys, and apply IP-based access restrictions and encryption controls.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls hold, and closes the remediation loop.

