
Educational tech giant Instructure has confirmed that data was stolen in a cyberattack, with the ShinyHunters extortion gang claiming responsibility.
Instructure is a U.S.-based education technology company best known for developing Canvas, a widely used learning management system that helps schools, universities, and organizations manage coursework, assignments, and online learning.
On Friday, Instructure disclosed that it suffered a cybersecurity incident and is working with third-party cybersecurity experts and law enforcement to investigate it.
On Saturday, the company issued an update stating that the personal information of users was exposed in the breach.
“While we continue actively investigating, thus far, indications are that the information involved consists of certain identifying information of users at affected institutions, such as names, email addresses, and student ID numbers, as well as messages among users,” reads the updated statement.
“At this time, we have found no evidence that passwords, dates of birth, government identifiers, or financial information were involved. If that changes, we will notify any impacted institutions.”
As part of the response, Instructure has deployed patches, increased monitoring, and rotated application keys as a precautionary step.
Customers are required to re-authorize access to Instructure’s API for new application keys to be issued.
While Instructure has not responded to BleepingComputer’s questions about when the breach occurred and whether they were being extorted, the ShinyHunters extortion gang has now listed the company on its data leak site.
“Nearly 9,000 schools worldwide affected. 275 million individuals data ranging from students, teachers, and other staff containing PII,” reads the data leak site.
“Several billions of private messages among students and teachers and students and other students involved, containing personal conversations and other PII. Your Salesforce instance was also breached and a lot more other data is involved.”
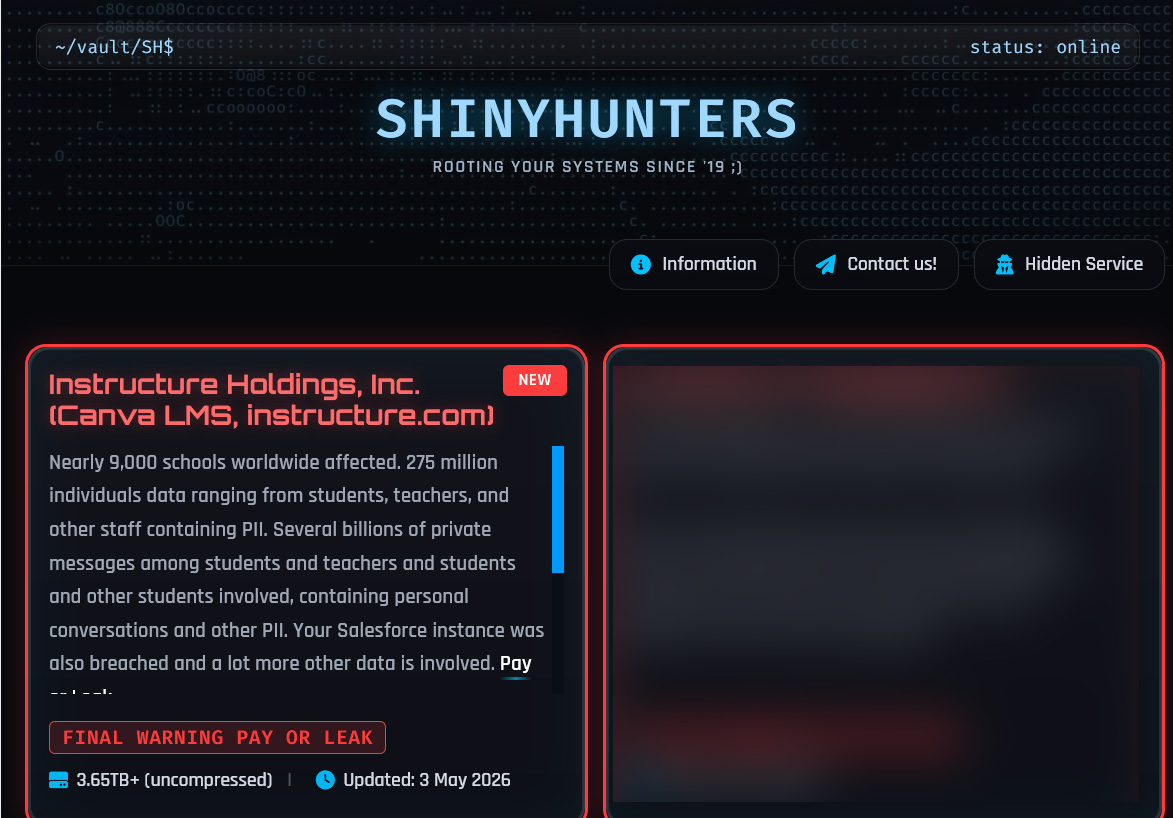
ShinyHunters claimed that the data was stolen from Instructure via a vulnerability in their systems, which has now been patched.
This data allegedly consists of over 240 million records tied to students, teachers, and staff. The threat actor says the data contains students’ names, email addresses, enrolled courses, and private messages to teachers.
Data shared by the threat actor indicates that the alleged dataset spans almost 15,000 institutions hosted across multiple geographic regions, including North America, Europe, and Asia-Pacific.
BleepingComputer has not been able to independently confirm which schools or how many individuals were impacted and has contacted Instructure with additional questions about the threat actor’s claims.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls hold, and closes the remediation loop.

