In May, VulnCheck identified evidence of 103 CVEs that were publicly disclosed for the first time as exploited in the wild, marking a 90.7% increase over April. This growth in public disclosure aligns with the rising trend in vulnerability exploitation, as highlighted by Verizon’s 2024 Data Breach Investigations Report (DBIR), which reported a massive 180% increase in vulnerability exploitation between 2022 and 2023.
- In May, VulnCheck identified 103 CVEs that were publicly disclosed for the first time as exploited in the wild – a 90%+ increase since April.
- Software that topped the list with new exploitation evidence includes Google Chrome, Microsoft Windows, Apple Safari and Adobe Acrobat Reader.
- New Exploitation Evidence sourced from Fortinet, CheckPoint, Aqua Security reports contributed to May’s spike in known exploited vulnerabilities.
- VulnCheck sourced known exploitation evidence faster than CISA for 71.4% of vulnerabilities from alternate sources in May.
- As of May 31st, 10 Known Exploited Vulnerabilities are still awaiting analysis by NIST NVD.
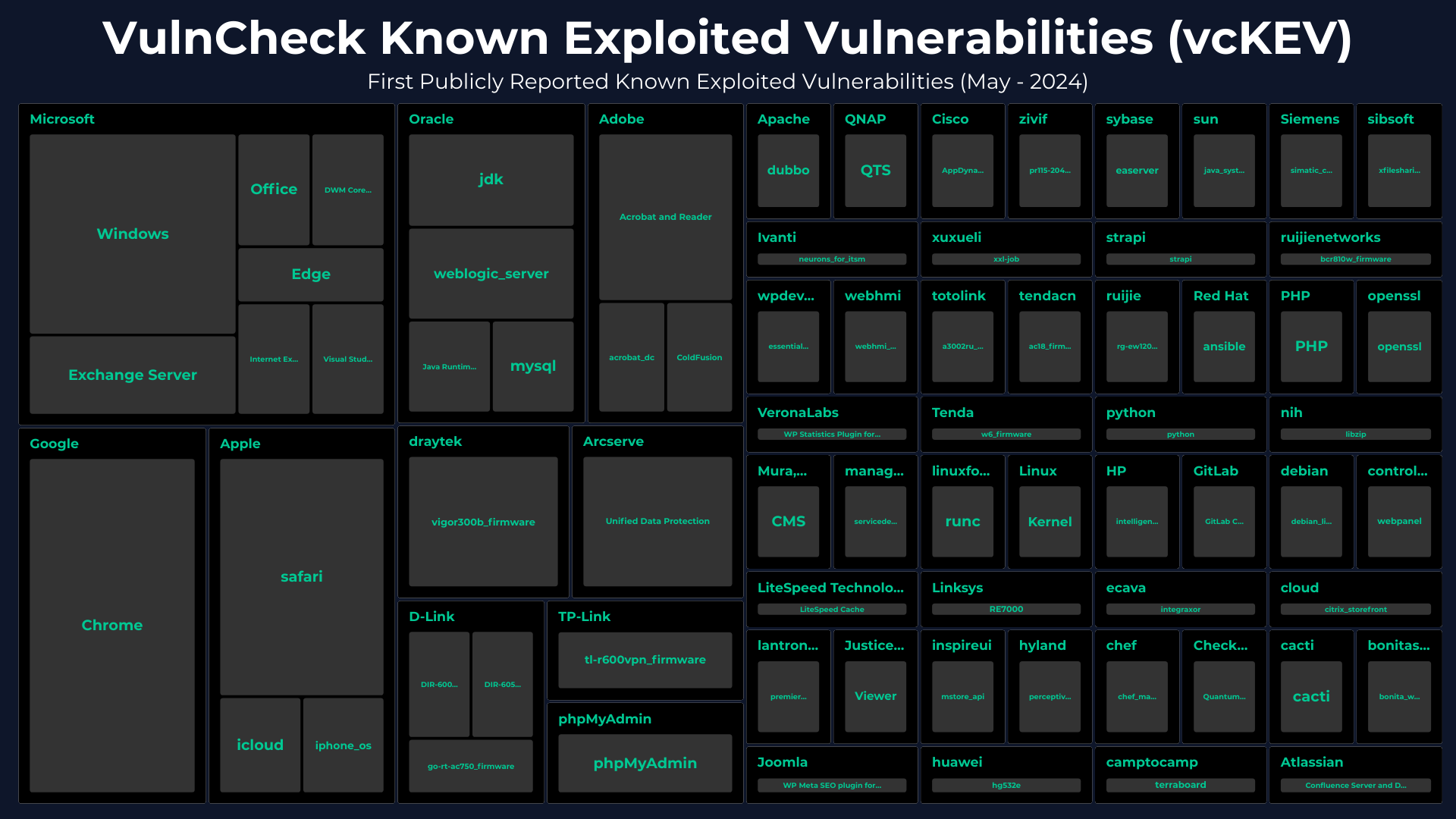
The 103 CVEs with known exploitation evidence were associated with 58 software suppliers across 73 unique products. The following software topped the list with two or more CVEs with known exploitation:
- Google Chrome: 7
- Microsoft Windows: 5
- Apple Safari: 5
- Adobe Acrobat Reader: 3
- Microsoft Exchange: 2
- Oracle JDK: 2
- phpMyAdmin: 2
TP-Link’s TL-R600VPN (2) is new to the VulnCheck Known Exploited Vulnerabilities (KEV), and Arcserve Unified Data Protection (3) has its first newly confirmed exploited vulnerabilities since early 2022.
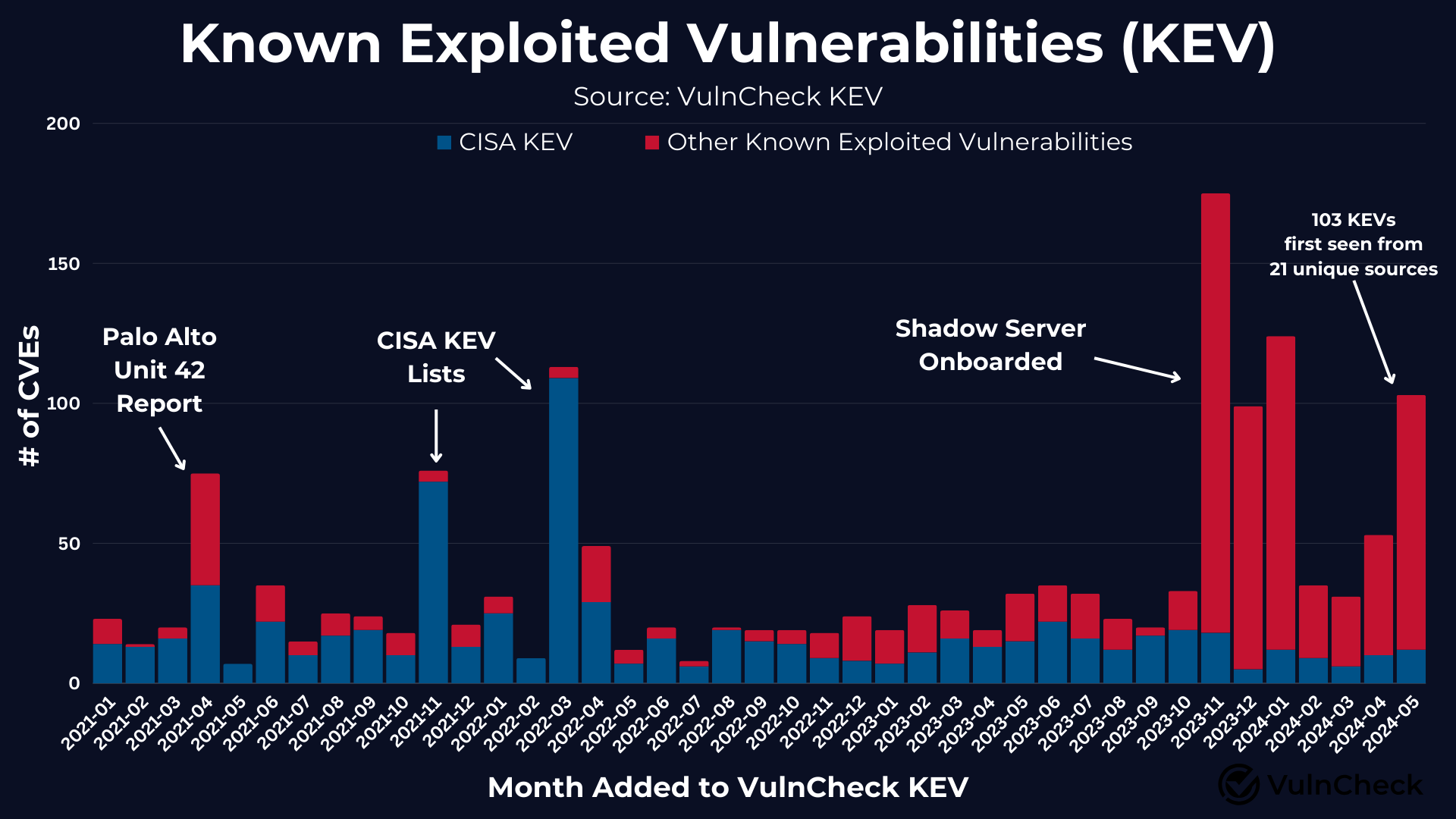
Investigating the substantial increase in new vulnerability exploitation disclosures, we observe a significant spike from previous months.
VulnCheck KEV has been in existence since January 2021 and prior to May, the only significant spikes in VulnCheck KEV data were:
- In April of 2021, Palo Alto’s Unit 42 published a report including 2020’s top exploited vulnerabilities.
- Late 2021, the Cybersecurity and Infrastructure Security Agancy(CISA) launched CISA KEV resulting in a spike in November 2021 and March 2022.
- Late 2023/Early 2024 onboarding ShadowServer as a new source for known exploitation.
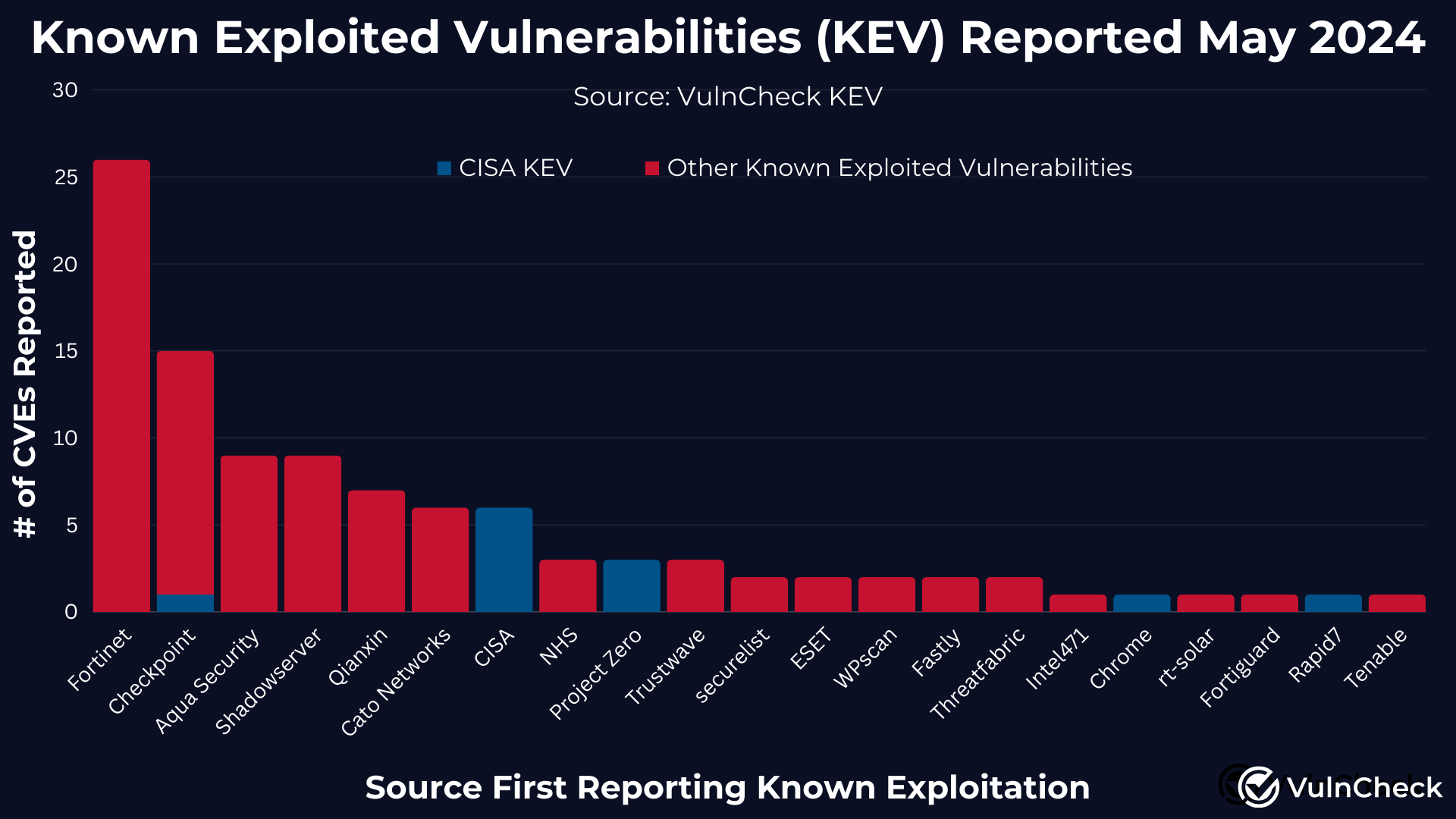
To understand the increase in the disclosure of known exploited vulnerabilities, we examined the reference sources provided with VulnCheck KEV. Three sources account for 49 unique vulnerabilities:
While this spike might align with seasonal trends and the RSA conference, it also demonstrates security vendors’ willingness to share broader vulnerability intelligence on known exploitation. This transparency is a significant positive for security teams, as it enhances their visibility into known exploitation.
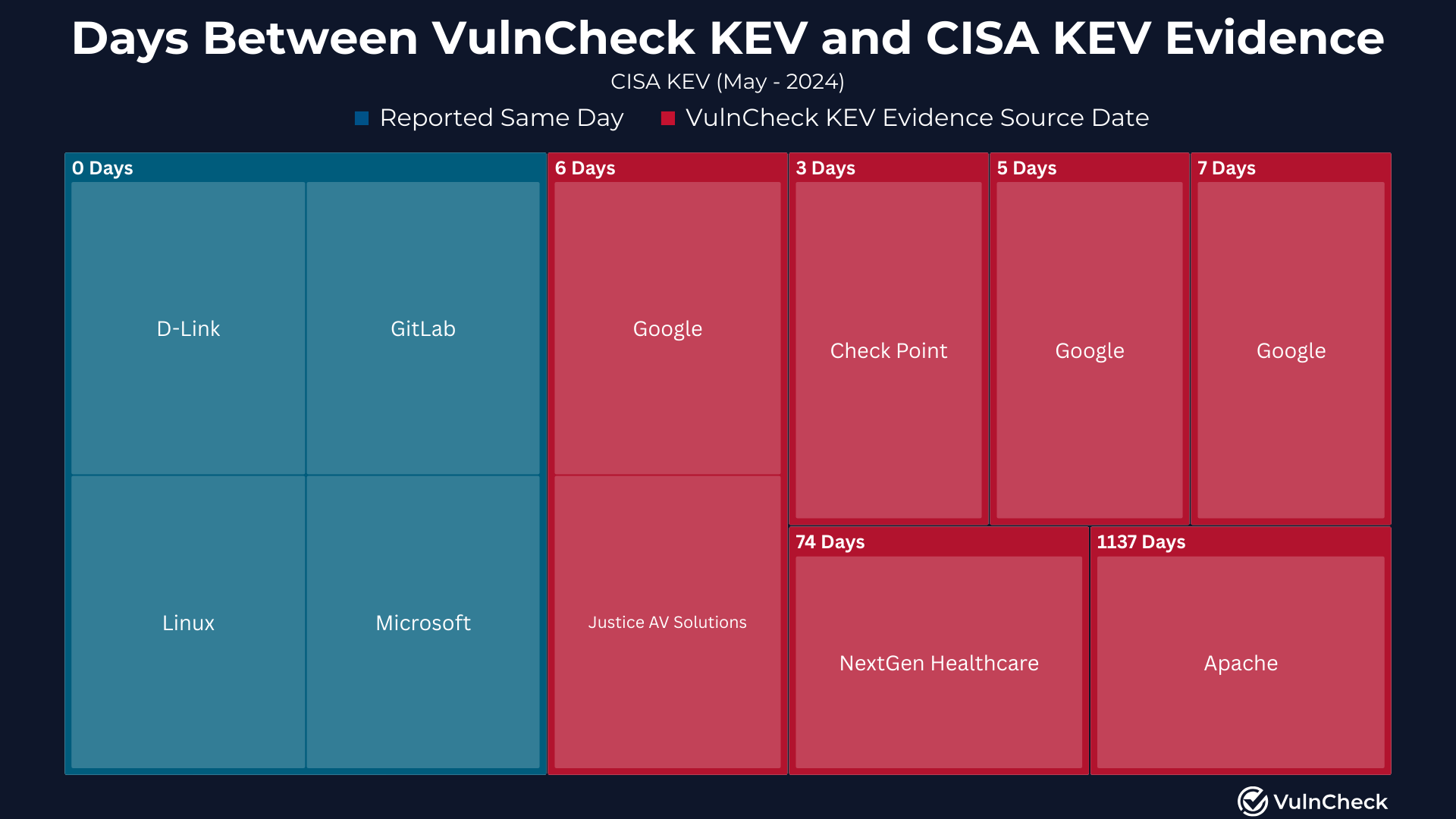
In May 2024, CISA added 14 vulnerabilities to its KEV, representing 13.6% of the vulnerabilities that VulnCheck discovered as having public exploitation evidence for the first time. VulnCheck sourced known exploitation evidence faster than CISA for 71.4% of these vulnerabilities from alternate sources.
In May, 22 out of 103 vulnerabilities added to VulnCheck KEV were published after February 12, 2024, when the NIST National Vulnerability Database (NVD) slowed down processing new vulnerabilities. Of these 22 known exploited vulnerabilities, 45% (10) were still awaiting analysis by NIST NVD as of May 31st.
For those eager to dive deeper into known exploited vulnerabilities, you can start by utilizing VulnCheck Community a free resource including VulnCheck KEV and VulnCheck NVD++.
VulnCheck is helping organizations not just to solve the vulnerability prioritization challenge – we’re working to help equip any product manager, CSIRT/PSIRT or SecOps team and Threat Hunting team to get faster and more accurate with infinite efficiency using VulnCheck solutions.
We knew that we needed better data, faster across the board, in our industry. So that’s what we deliver to the market. We’re going to continue to deliver key insights on vulnerability management, exploitation and major trends we can extrapolate from our dataset to continuously support practitioners.
Are you interested in learning more? If so, VulnCheck’s Exploit & Vulnerability Intelligence has broad threat actor coverage. Register and demo our data today.
