Over 10,000 Zimbra Collaboration Suite (ZCS) instances exposed online are vulnerable to ongoing attacks exploiting a cross-site scripting (XSS) security flaw, according to nonprofit security organization Shadowserver.
Zimbra is a popular email and collaboration software suite used by hundreds of millions of people worldwide, including hundreds of government agencies and thousands of businesses.
The vulnerability (tracked as CVE-2025-48700) affects ZCS 8.8.15, 9.0, 10.0, and 10.1 and can allow unauthenticated attackers to access sensitive information after executing arbitrary JavaScript within the user’s session.
Synacor released security patches to address the flaw in June 2025, when it warned that CVE-2025-48700 exploits require no user interaction and can be triggered when a user views a maliciously crafted email message in the Zimbra Classic UI.
On Monday, CISA flagged CVE-2025-48700 as being abused in the wild and added it to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation.
The U.S. cybersecurity agency also ordered Federal Civilian Executive Branch (FCEB) agencies to secure their Zimbra servers within three days, by April 23.
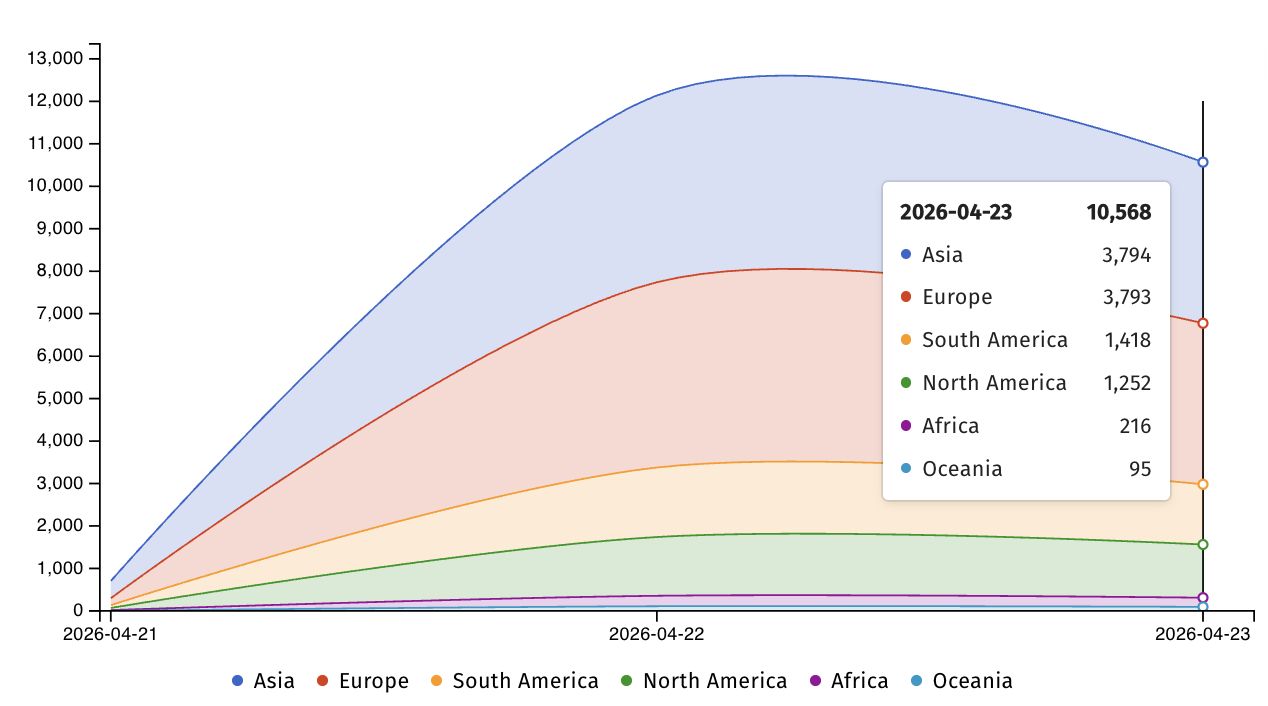
On Friday, Internet security watchdog Shadowserver also warned that over 10,500 Zimbra servers exposed online remain unpatched, most of them in Asia (3,794) and Europe (3,793).
While CISA didn’t share any details about CVE-2025-48700 attacks, another XSS vulnerability (tracked as CVE-2025-66376 and patched in early November) was exploited by the state-backed APT28 (a.k.a. Fancy Bear, Strontium) military hackers in phishing attacks targeting Ukrainian government entities starting in January.
This phishing campaign (codenamed Operation GhostMail by security researchers at Seqrite Labs) also targeted the Ukrainian State Hydrology Agency (a critical infrastructure entity under the Ministry of Infrastructure that provides navigational, maritime, and hydrographic support) and delivered an obfuscated JavaScript payload when recipients opened the malicious emails in vulnerable Zimbra webmail sessions.
“The phishing email has no malicious attachments, no suspicious links, no macros. The entire attack chain lives inside the HTML body of a single email, there are no malicious attachments,” Seqrite Labs said at the time.
Zimbra flaws are frequently exploited in attacks and have been used to breach thousands of vulnerable email servers in recent years.
For instance, Russian Winter Vivern cyberespies used another reflected XSS exploit to breach Zimbra webmail portals in February 2023 and steal emails sent and received by NATO-aligned organizations and individuals, including military personnel, government officials, and diplomats.
More recently, in October 2024, U.S. and U.K. cyber agencies warned that APT29 (a.k.a. Cozy Bear, Midnight Blizzard) hackers linked to Russia’s Foreign Intelligence Service (SVR) were targeting vulnerable Zimbra servers “at a mass scale,” exploiting a security issue that had been previously abused to steal email account credentials.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls hold, and closes the remediation loop.