
A threat group tracked as UNC6692 uses social engineering to deploy a new, custom malware suite named “Snow,” which includes a browser extension, a tunneler, and a backdoor.
Their goal is to steal sensitive data after deep network compromise through credential theft and domain takeover.
According to Google’s Mandiant researchers, the attacker uses “email bombing” tactics to create urgency, then contact targets via Microsoft Teams, posing as IT helpdesk agents.
A recent Microsoft report highlighted the growing popularity of this tactic in the cybercrime space, tricking users into granting attackers remote access via Quick Assist or other remote access tools.
In the case of UNC6692, the victim is prompted to click a link to install a patch that would block email spam. In reality, the victims get a dropper that executes AutoHotkey scripts loading “SnowBelt,” a malicious Chrome extension.
Source: Google
The extension executes on a headless Microsoft Edge instance, so the victim doesn’t notice anything, while scheduled tasks and a startup folder shortcut are also created for persistence.
SnowBelt serves as a persistence mechanism and a relay mechanism for commands the operator sends to a Python-based backdoor named SnowBasin.
Commands are delivered through a WebSocket tunnel established by a tunneler tool called SnowGlaze, to mask communications between the host and the command-and-control (C2) infrastructure.
SnowGlaze also facilitates SOCKS proxy operations, allowing arbitrary TCP traffic to be routed through the infected host.
SnowBasin runs a local HTTP server and executes attacker-supplied CMD or PowerShell commands on the infected system, relaying the results back to the operator through the same pipeline.
The malware supports remote shell access, data exfiltration, file download, screenshot capturing, and basic file management operations.
The operator can also issue a self-termination command to shut down the backdoor at the host.
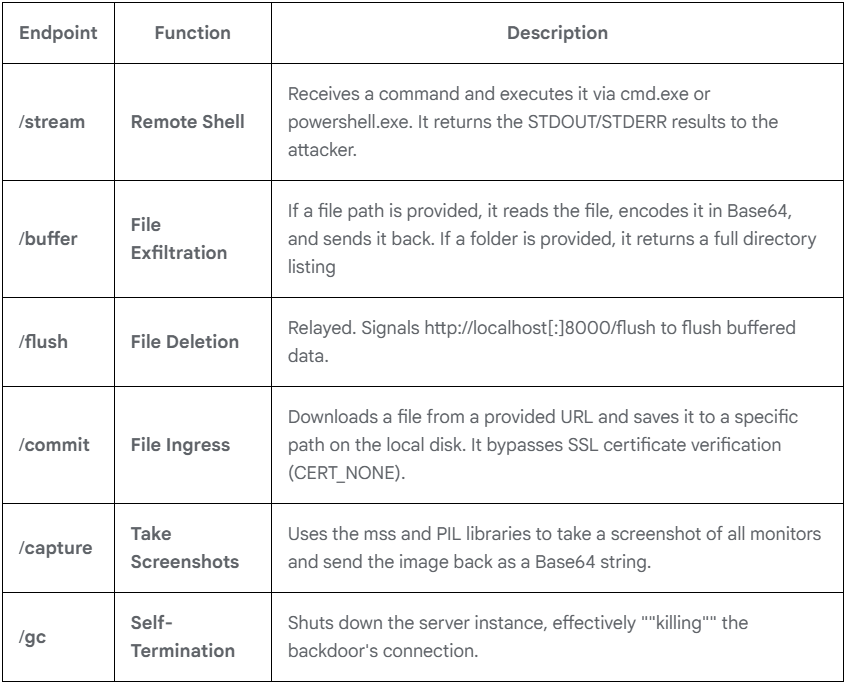
Source: Google
Mandiant has found that, post-compromise, the attackers performed internal reconnaissance, scanning for services such as SMB and RDP to identify additional targets, and then moved laterally on the network.
The attackers dumped LSASS memory to extract credential material and used pass-the-hash techniques to authenticate to additional hosts, eventually reaching domain controllers.
At the final stage of the attack, the threat actor deployed FTK Imager to extract the Active Directory database, along with SYSTEM, SAM, and SECURITY registry hives.
These files were exfiltrated from the network using LimeWire, giving the attackers access to sensitive credential data across the domain.
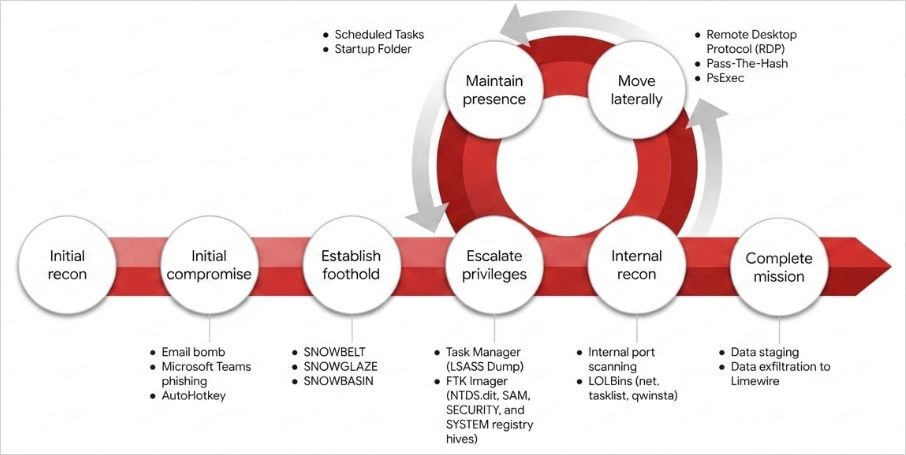
Source: Google
The report provides extensive indicators of compromise (IoCs) and also YARA rules to help detect the “Snow” toolset.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls hold, and closes the remediation loop.


